Cell Line Cross-Contamination: A Comprehensive Guide for Researchers on Risks, Detection, and Prevention
Cell line cross-contamination and misidentification represent a critical, persistent challenge in biomedical research and drug development, leading to spurious scientific conclusions, wasted resources, and compromised therapeutic products.
Cell Line Cross-Contamination: A Comprehensive Guide for Researchers on Risks, Detection, and Prevention
Abstract
Cell line cross-contamination and misidentification represent a critical, persistent challenge in biomedical research and drug development, leading to spurious scientific conclusions, wasted resources, and compromised therapeutic products. This article provides a comprehensive overview for researchers and scientists, covering the foundational problem of contamination, methodological approaches for detection and authentication, troubleshooting and optimization strategies for prevention, and validation techniques to ensure research integrity. By synthesizing current data and best practices, this guide aims to equip professionals with the knowledge to safeguard their research against the detrimental effects of using false cell lines.
Understanding the Crisis: The Pervasive Problem of Cell Line Cross-Contamination
Defining Cell Line Cross-Contamination and Accidental Co-Culture
Cell line cross-contamination and accidental co-culture represent one of the most persistent and problematic issues in modern biomedical research, potentially compromising experimental validity and reproducibility on a global scale. Cross-contamination occurs when an unintended cell line infiltrates a culture, often through laboratory handling errors, while accidental co-culture refers to the unintentional mixing of two or more cell lines leading to their simultaneous propagation [1] [2]. This problem has plagued cell culture research for decades, with the first recognized cases tracing back to the widespread distribution of HeLa cells in the 1950s [3]. Despite long-standing awareness, the scientific community continues to grapple with these issues, as evidenced by the International Cell Line Authentication Committee (ICLAC) registry which currently lists 593 misidentified or cross-contaminated cell lines [4].
The significance of this problem cannot be overstated. Rough estimates suggest that approximately 16.1% of published papers have utilized problematic cell lines, creating a ripple effect of wasted resources, misleading follow-up studies, and compromised evidence-based conclusions [5] [4]. The pervasive nature of cell line misidentification affects basic research, drug discovery, and preclinical studies, ultimately threatening the translation of scientific findings into clinical applications. This technical guide examines the fundamental aspects of cell line cross-contamination within the broader context of research integrity, providing researchers, scientists, and drug development professionals with comprehensive strategies for prevention, detection, and remediation.
Defining the Problem: Scope and Classification
Terminology and Basic Concepts
Cell line cross-contamination involves the introduction and subsequent overgrowth of an unintended cell line into a culture, fundamentally altering its biological identity. This phenomenon must be distinguished from other forms of contamination, such as microbial or chemical contamination, though all can coexist and compound experimental errors [1]. The most notorious contaminant is the HeLa human adenocarcinoma cell line, which has cross-contaminated numerous other cell lines due to its prolific growth capacity [6] [4]. A closely related issue, accidental co-culture, occurs when two or more cell lines are unintentionally mixed and maintained together, potentially leading to complex cellular interactions that misinterpreted as biological phenomena [2] [7].
The problem manifests primarily through two mechanisms: inter- and intraspecific cross-contamination. Interspecific contamination involves cells from different species, while intraspecific contamination occurs between cell lines of the same species [5] [2]. Both forms present serious challenges to research validity, though intraspecific contamination can be particularly difficult to detect without specialized authentication methods.
Magnitude of the Problem: Quantitative Assessments
Table 1: Documented Misidentified Cell Lines in the ICLAC Registry
| Category | Number of Cell Lines | Common Contaminants |
|---|---|---|
| Liver cell lines | 21 | HeLa, HepG2 |
| Stomach cell lines | 14 | HeLa, HT-29 |
| Total misidentified cell lines | 593 | Various |
| Publications using misidentified lines | ~6,000 (for 5 selected lines alone) | N/A |
Recent data collection from the ICLAC registry reveals the alarming scope of this issue. The registry currently documents nearly 600 misidentified cell lines, with certain tissue types particularly affected [4]. A comprehensive search of the PubMed database identified almost 6,000 publications using just five commonly misidentified cell lines: QGY-7703, BGC-823, BEL-7402, L-02, and WRL-68 [4]. The persistence of these problematic lines in contemporary research underscores the critical need for enhanced awareness and systematic authentication practices.
The National Center for Advancing Translational Sciences (NCATS) experience further illustrates this point. Their systematic testing of over 2,000 cell line samples revealed that while only five misidentified cell lines were identified among 186 tested (approximately 2.7%), all these misidentified lines originated from external laboratories [6]. This finding highlights the importance of verifying cell line identity upon receipt, regardless of the source's reputation.
Causes and Consequences of Cross-Contamination
Cross-contamination typically originates from procedural failures in laboratory practice. The most common sources include simultaneous handling of multiple cell lines in the same biosafety cabinet, improper cleaning procedures between cell line manipulations, mislabelling of storage vessels, and use of shared equipment or media without adequate decontamination [1] [7]. Laboratories utilizing shared cell culture spaces face elevated risks, particularly when clear separation protocols for different cell lines are not established and consistently followed [1].
Highly proliferative cell lines pose the greatest contamination risk. Cells such as HeLa, HEK293, and other rapidly dividing lines can overgrow slower-growing populations from just a few contaminating cells, fundamentally altering the culture's characteristics within a few passages [1] [6]. This competitive advantage explains why certain cell lines appear repeatedly as contaminants across different culture systems.
Scientific and Practical Consequences
The consequences of undetected cross-contamination are far-reaching and potentially devastating to research integrity. Scientifically, the use of misidentified cell lines generates invalid data that can misdirect entire research fields. For example, Mycoplasma-contaminated HCT-116 colon cancer cells were found to be 5- to 100-fold more resistant to 5-fluorouracil and 5-fluorodeoxyuridine compared to uncontaminated cells, profoundly affecting drug response studies [6]. In another documented case, the apparent selective killing of multidrug-resistant cancer cell lines by tiopronin was later attributed to Mycoplasma contamination rather than genuine biological activity [6].
Practically, cross-contamination leads to irreproducible results, wasted resources, and compromised therapeutic development. In research settings, contamination affects data integrity and reproducibility, while in Good Manufacturing Practice (GMP) biopharmaceutical production, contamination can lead to complete batch failures, substantial financial losses, regulatory violations, and potential patient safety risks [1]. The cumulative impact across the biomedical research enterprise represents billions of dollars in misdirected funding and incalculable delays in scientific progress.
Detection and Authentication Methodologies
Established Authentication Techniques
Multiple well-established methods exist for cell line authentication, ranging from classical approaches to modern molecular techniques. Short tandem repeat (STR) profiling has emerged as the gold standard for human cell line authentication, providing DNA fingerprints based on highly polymorphic regions scattered throughout the genome [6] [4]. This method compares the STR profile of a cell line to reference databases, allowing for definitive identification and detection of cross-contamination.
Table 2: Cell Line Authentication and Contamination Detection Methods
| Method | Principle | Application | Limitations |
|---|---|---|---|
| STR Profiling | Analysis of short tandem repeat polymorphisms | Cell line authentication, intraspecies contamination | Limited discrimination for closely related lines |
| Isoenzyme Analysis | Electrophoretic separation of isoforms of metabolic enzymes | Species identification | Lower discrimination power than DNA methods |
| Karyotyping | Chromosome analysis and banding patterns | Genetic stability, species confirmation | Time-consuming, requires expertise |
| PCR-Based Methods | Species-specific amplification of target genes | Species identification | Limited to known sequences |
| Mycoplasma Testing (MycoAlert) | Detection of microbial enzyme activity | Mycoplasma contamination screening | May miss some species; requires culture |
| Viral Detection (ViralCellDetector) | RNA-seq mapping to viral databases | Viral contamination screening | Computational resource requirements |
Alternative methods include isoenzyme analysis, which examines electrophoretic mobility patterns of metabolic enzymes; karyotyping, which assesses chromosome morphology and number; and more recent approaches such as single nucleotide polymorphism (SNP) profiling [3]. Each method offers distinct advantages and limitations, with STR profiling generally providing the optimal balance of discrimination power, reproducibility, and cost-effectiveness for routine authentication of human cell lines.
Specialized Detection Approaches
Beyond general authentication, specialized methods target specific contamination types. Mycoplasma contamination detection typically employs PCR-based assays, enzymatic tests such as the MycoAlert system, or fluorescence staining [1] [6]. The MycoAlert assay, for example, detects ATP production by endogenous Mycoplasma enzymes through a luciferase-based chemiluminescence reaction, providing results within approximately one hour [6].
For viral contamination, traditional approaches focused on PCR-based detection of specific pathogens, but newer computational tools like ViralCellDetector offer broader screening capabilities. This tool processes RNA-seq data by first aligning reads to the host reference genome, then mapping unmapped reads to the comprehensive NCBI viral genome database using the BWA aligner [8]. Viral presence is determined using stringent criteria based on the number of mapped reads and viral genome coverage, with additional machine learning approaches using host gene expression biomarkers to identify infected samples [8].
Chemical authentication methods represent an emerging alternative. One innovative approach utilizes differential cellular responses to chemical compounds, such as tamoxifen derivatives, to distinguish between breast cancer cell lines based on their unique IC50 values and subsequent effects on cell cycle progression, caspase activity, and proliferation [3]. While not replacing DNA-based methods, this chemical approach provides complementary authentication data based on functional cellular responses.
Experimental Protocols for Authentication and Quality Control
STR Profiling Protocol
STR profiling represents the most widely accepted method for authenticating human cell lines. The standard protocol involves DNA extraction from cell pellets, PCR amplification of multiple STR loci using commercial kits, capillary electrophoresis of amplified fragments, and comparison of resulting profiles to reference databases [6] [4]. Critical steps include:
- Sample Preparation: Harvest cells in mid-log phase growth, ensuring ≥80% viability. Wash cell pellets with phosphate-buffered saline to remove culture media contaminants.
- DNA Extraction: Use standardized extraction methods to obtain high-quality DNA with A260/A280 ratios between 1.8-2.0.
- PCR Amplification: Utilize commercial STR profiling kits containing primers for 8-16 core STR loci plus amelogenin for gender identification. Include appropriate positive controls.
- Fragment Analysis: Separate amplified products by capillary electrophoresis on genetic analyzers with internal size standards for precise fragment sizing.
- Data Interpretation: Compare resulting allele calls with reference profiles from established databases such as ATCC or DSMZ. Match thresholds typically require ≥80% allele concordance.
Regular testing intervals are essential, with recommendations including authentication upon cell line receipt, during master cell bank preparation, and at regular passages during extended culture (every 3-6 months or approximately 10 passages) [6].
Mycoplasma Detection Protocol
Routine Mycoplasma testing represents a critical component of cell culture quality control. The MycoAlert assay protocol provides a standardized approach for biochemical detection:
- Sample Collection: Collect spent cell culture media after cells have been incubated for several days without antibiotic treatment, as antibiotics may suppress but not eliminate Mycoplasma contamination.
- Reagent Preparation: Equilibrate MycoAlert substrate and buffer to room temperature. Reconstitute lyophilized substrate with provided diluent if necessary.
- Assay Procedure: Transfer 100μL of spent media to a luminometer tube. Add 100μL of MycoAlert substrate, mix gently, and incubate for 5 minutes. Measure luminescence (Reading A). Add 100μL of MycoAlert buffer, mix gently, incubate for 10 minutes, and measure luminescence again (Reading B).
- Calculation and Interpretation: Divide Reading B by Reading A to obtain the Mycoplasma detection ratio. Ratios <1.0 indicate negative samples, ratios ≥1.0 suggest Mycoplasma contamination, and ambiguous results (e.g., 0.9-1.0) require retesting.
For confirmed contamination, immediate destruction of affected cell lines is recommended whenever possible. In exceptional circumstances where cell lines are irreplaceable, antibiotic treatments with compounds such as plasmocin may be attempted, though re-sourcing is generally preferred [6].
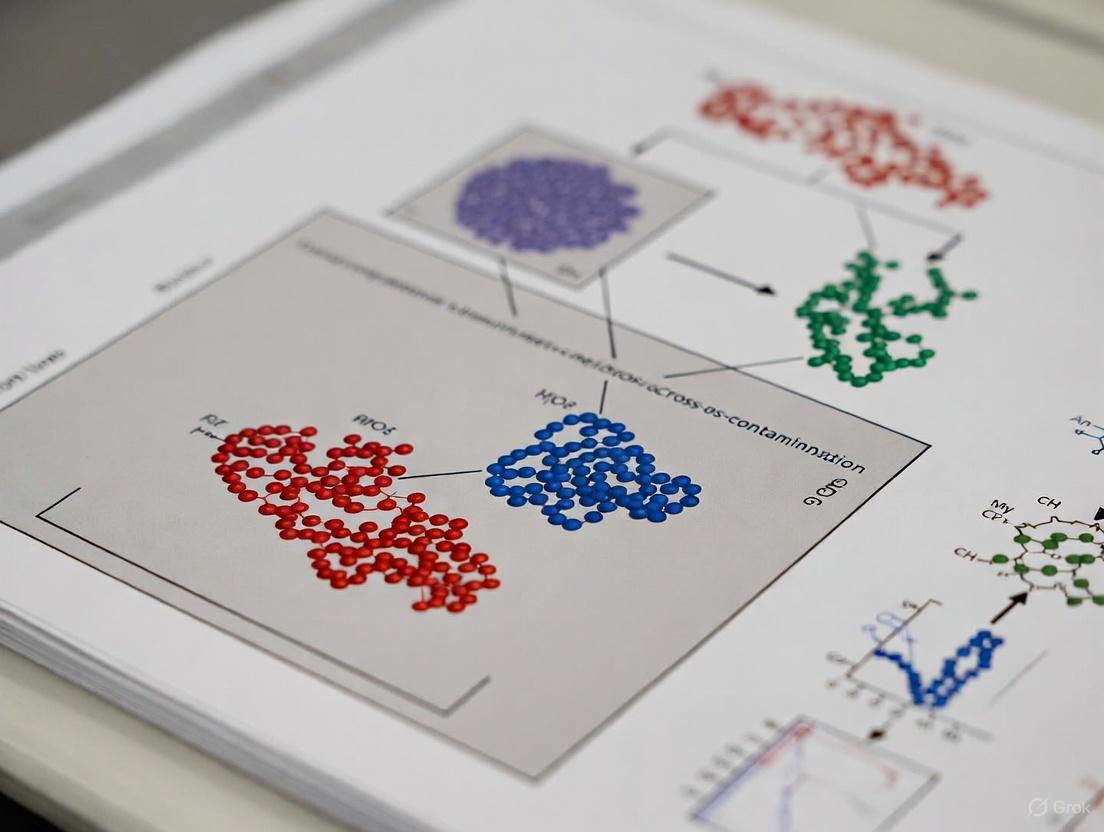
Diagram 1: Cell Line Authentication Workflow via STR Profiling
Prevention Strategies and Best Practices
Laboratory Practice and Technique
Meticulous laboratory practice forms the foundation of cross-contamination prevention. Essential techniques include working with only one cell line at a time within the biosafety cabinet, thoroughly cleaning surfaces between handling different cell lines, and using dedicated media and reagents for each cell line whenever possible [7]. Biosafety cabinets should be properly maintained and certified regularly, with work surfaces decontaminated with appropriate disinfectants before and after use.
Additional critical practices include regular freezing of authenticated cell stocks, systematic discard of highly passaged cells, and clear, indelible labeling of all storage vessels with cell line identifier, passage number, and date [7]. Laboratories should maintain accurate, redundant records of cell line stocks, including authentication data and processing history, to ensure traceability and accountability.
Systematic Quality Control Programs
Implementing structured quality control programs represents the most effective approach for preventing cross-contamination-related errors. The NCATS model provides an excellent framework, featuring mandatory Mycoplasma testing for all incoming cell lines, authentication testing upon receipt, regular monthly testing for cell lines in continuous culture, and confirmation testing immediately prior to critical experiments such as high-throughput screening [6].
Diagram 2: Comprehensive Cell Line Quality Control Pipeline
Effective programs establish clear policies for contaminated cell lines, typically requiring immediate destruction whenever possible. When irreplaceable cell lines become contaminated, strict quarantine procedures in dedicated incubators with separate equipment should be enforced until decontamination is verified [6]. Systematic documentation of all quality control activities, including testing results and subsequent actions, provides an auditable trail for troubleshooting and regulatory compliance.
Table 3: Essential Resources for Cell Line Authentication and Contamination Prevention
| Resource/Reagent | Function | Application Notes |
|---|---|---|
| STR Profiling Kits | Multiplex PCR amplification of STR loci | Standardized for human cell authentication |
| MycoAlert Assay | Biochemical detection of Mycoplasma | Weekly screening of active cultures |
| Plasmocin | Antibiotic treatment of Mycoplasma | Use only for irreplaceable contaminated lines |
| ViralCellDetector | Computational viral detection from RNA-seq | Broad-spectrum viral screening |
| ICLAC Register | Database of misidentified cell lines | Reference before acquiring new lines |
| Cellosaurus | Comprehensive cell line knowledge resource | Cross-referencing cell line information |
| SciScore | Methods analysis for authentication reporting | Automated assessment of methods sections |
Cell line cross-contamination and accidental co-culture represent preventable yet persistently problematic issues that fundamentally threaten biomedical research validity. The continued use of misidentified cell lines, despite decades of awareness and the availability of reliable authentication methods, suggests systemic challenges that require coordinated solutions across the research community. Through implementation of rigorous authentication protocols, adherence to strict laboratory practices, and institutional commitment to quality control, researchers can substantially reduce these risks. The scientific integrity of cell-based research depends on unequivocal confirmation that cell lines used in experiments genuinely represent the biological systems they purport to model. Only through sustained vigilance and systematic authentication can the research community ensure the reproducibility and translational potential of cell-based science.
Cell line cross-contamination represents a pervasive and enduring challenge in biomedical research, with the HeLa cell line being the most prolific contributor. This in-depth technical guide explores the historical origins and modern implications of this issue, detailing the evolution of authentication technologies and standardized protocols designed to safeguard scientific integrity. Framed within the context of a broader thesis on cross-contamination, this document provides drug development professionals and researchers with quantitative data on contamination rates, detailed experimental methodologies for cell line verification, and visual workflows for integration into routine laboratory practice.
The problem of cell line cross-contamination has persisted for nearly as long as cell culture itself. The first immortal human cell line, HeLa, was established from cervical cancer cells taken from Henrietta Lacks in 1951 [9]. Its remarkable vigor and immortality, while making it an invaluable research tool, also made it a potent source of contamination. Despite an early observation at Johns Hopkins that these vigorous lines could overgrow slower-growing cultures, the issue proliferated into a widespread concern that continues to affect research more than six decades later [10].
The seminal work of Stanley Gartler in the 1960s, using isoenzyme analysis, provided the first systematic evidence, showing that 18 cell lines of presumed independent origin were, in fact, HeLa contaminants [10]. This problem is not historical alone; a 2008 analysis of 40 human thyroid cancer cell lines revealed only 23 unique genetic profiles, with many cross-contaminants not even being of thyroid origin [10]. Today, it is estimated that 15–20% of cell lines in use may be misidentified, and the International Cell Line Authentication Committee (ICLAC) curates a register of hundreds of compromised lines [10] [5]. This persistent issue underscores the critical need for vigilant authentication and standardized practices in modern laboratories.
The Scale and Impact of Cross-Contamination
Cross-contamination poses a direct threat to the validity of research data, leading to wasted resources and flawed scientific conclusions. The scale of the problem is significant, with contamination events affecting a wide range of cell lines.
Table 1: Documented Instances of Cell Line Cross-Contamination
| Contaminated Cell Line | Documented Origin | Method of Discovery | Key Reference(s) |
|---|---|---|---|
| HES (Human Endometrial Epithelial) | HeLa (via WISH cells) | STR Analysis (9 loci) | [11] |
| WISH (Human Amnion Epithelium) | HeLa | STR Analysis | [11] |
| Multiple NPC* Cell Lines (CNE1, CNE2, etc.) | HeLa | STR Profiling & RNA Sequencing | [12] |
| 18 Various Cell Lines (e.g., Hep-2, KB) | HeLa | Isoenzyme Analysis | [10] |
| 40 Human Thyroid Cancer Lines | Various (non-thyroid) | Genetic Profiling | [10] |
*NPC: Nasopharyngeal Carcinoma
The impact extends beyond individual cell lines. A 2024 correspondence highlights that the use of HeLa-contaminated nasopharyngeal carcinoma (NPC) cell lines remains a common problem, risking the misinterpretation of data and misdirection of research efforts [12]. Furthermore, rough estimates suggest that approximately 16.1% of published papers may have used problematic cell lines, contaminating the scientific literature with false and irreproducible results [5].
Modern Authentication Methods and Protocols
The cornerstone of combating cross-contamination is rigorous cell line authentication. Several key methodologies have been developed and standardized.
Short Tandem Repeat (STR) Profiling
STR profiling has become the gold standard for the intra-species identity testing of human cell lines [10]. This PCR-based technique simultaneously amplifies multiple polymorphic STR loci (short, repeating DNA sequences) throughout the genome. The combination of alleles at these loci creates a unique DNA fingerprint for each cell line.
Detailed STR Protocol (as applied in HES/HeLa discovery [11]):
- Cell Preparation: Grow cells to confluence in a 100 mm dish. Harvest approximately 10^6 cells.
- DNA Isolation: Extract genomic DNA using a standardized commercial kit.
- PCR Amplification: Amplify DNA using a multiplexed PCR reaction targeting a panel of STR loci (e.g., CSF1PO, D13S317, D16S539, D5S818, D7S820, TH01, TPOX, vWA) and the amelogenin (AMEL) sex-determination locus. The StemElite ID system (Promega) is one such platform.
- Fragment Analysis: Separate the fluorescently-labeled PCR products by capillary electrophoresis.
- Data Analysis: Determine the allele sizes (number of repeats) at each locus using specialized software. Compare the resulting profile to reference databases (e.g., ATCC, DSMZ).
Table 2: Key Cell Line Authentication Techniques
| Method | Principle | Application | Advantages | Limitations |
|---|---|---|---|---|
| STR Profiling | Analysis of highly polymorphic microsatellite loci | Intra-species identification of human cell lines; forensic-style fingerprinting | High discrimination power; standardized; high-throughput | Less effective for non-human lines |
| Isoenzyme Analysis | Electrophoretic separation of species-specific enzyme isoforms | Detection of interspecies cross-contamination | Rapid; robust; low-tech | Low reproducibility; limited discrimination |
| Karyotyping | Examination of stained chromosomes for number and structure | Detection of genetic instability and large-scale changes | Identifies gross genomic alterations | Low resolution; labor-intensive |
| Cytochrome C Oxidase (COI) Subunit Analysis | DNA barcoding of a mitochondrial gene | Species identification (interspecies contamination) | High accuracy for species determination | Not for intra-species authentication |
Authentication Workflow
The following diagram illustrates the logical workflow for cell line authentication in a modern research setting, from culture to verification.
Implementing robust authentication requires specific reagents and resources. The following table details key solutions for the critical procedure of STR profiling.
Table 3: Research Reagent Solutions for Cell Line Authentication
| Item | Function/Description | Example/Note |
|---|---|---|
| STR Profiling Kit | Multiplex PCR kit containing primers for amplifying core STR loci. | Promega PowerPlex 16 System; StemElite ID [11] |
| DNA Extraction Kit | For isolation of high-quality, PCR-ready genomic DNA from cell pellets. | Phenol-chloroform or silica-membrane based kits. |
| Capillary Electrophoresis Instrument | For high-resolution separation and detection of fluorescently-labeled STR amplicons. | ABI Genetic Analyzers (Applied Biosystems). |
| Reference Database | Online database of published STR profiles for comparison. | ATCC STR Database; ICLAC Register of Misidentified Cell Lines [10] [12] |
| Cell Freezing Medium | Cryoprotectant for creating secure master cell banks. | Typically 5-10% DMSO in serum [13]. |
| Controlled-Rate Freezer | Equipment to freeze cells at -1°C/minute, preserving viability and stability. | Isopropyl alcohol (Mr. Frosty) or alcohol-free (CoolCell) containers [13]. |
Good Cell Culture Practice (GCCP) for Prevention
Prevention is the most effective strategy against cross-contamination. Adherence to GCCP minimizes risk at every stage [10] [5].
- Establish Master and Working Cell Banks: Upon receipt, create a characterized master cell bank from a low-passage culture. Generate working banks to limit continual culture and genetic drift [13].
- Implement Aseptic Technique: Always use biosafety cabinets and proper sterile technique. Regularly disinfect equipment and workspaces.
- Handle Cell Lines One at a Time: This simple practice prevents aerosol-mediated cross-contamination. Avoid using shared media bottles between different cell lines.
- Use Clear Labeling and Records: Label all vials and flasks unambiguously with the cell line name, passage number, and date. Maintain accurate, detailed inventory records [10].
- Perform Regular Authentication: Test cell lines upon arrival, when creating a bank, and at regular intervals during extended culture (e.g., every 3 months). Testing is also essential prior to initiating key experiments and before publication [10].
- Monitor Morphology and Behavior: Be vigilant for unexpected changes in growth rate, morphology, or culture medium turbidity, which can indicate contamination [13].
The scientific community is increasingly mandating authentication. Journals are adopting policies requiring evidence of cell line identity prior to publication, and organizations like ATCC and ICLAC are publishing standards (e.g., ANSI/ATCC ASN-0002) for authentication [10]. Emerging methods, such as single nucleotide polymorphism (SNP) examination and RNA sequencing, offer additional layers of verification [10] [12].
The journey from the initial discovery of HeLa's contaminating potential to the modern, authentication-focused laboratory highlights a critical evolution in research ethics and practice. While the legacy of HeLa contamination is long, it has driven the development of powerful tools and standards. For researchers and drug development professionals, the mandate is clear: rigorous authentication and impeccable cell culture practice are no longer optional but are fundamental to producing valid, reproducible, and impactful science.
Cross-contamination in cell culture represents a critical threat to biomedical research integrity, occurring when a cell line is inadvertently replaced by or mixed with another, often more aggressive, cell type. The pervasive nature of this problem, coupled with its profound scientific and financial consequences, constitutes a silent crisis undermining experimental reproducibility and therapeutic development. Misidentified and contaminated cell lines propagate through the scientific literature, generating invalid data, misleading conclusions, and substantial economic waste. This whitepaper synthesizes current, alarming statistics on the prevalence and financial impact of cell line cross-contamination, providing researchers with definitive data and essential protocols to safeguard research integrity.
Quantifying the Problem: Prevalence of Misidentified Cell Lines
The scale of the cell line misidentification problem is both vast and historically persistent. The International Cell Line Authentication Committee (ICLAC) maintains a authoritative register of known misidentified cell lines. The most recent data indicates this register now lists 593 cross-contaminated or misidentified cell lines [4]. A striking number of these are cell lines purportedly of hepatic origin; the register specifically identifies 21 misidentified "liver cell lines" and 14 misidentified "stomach cell lines" that are, in reality, contaminated by other cell types [4]. The HeLa cell line, derived from human cervical adenocarcinoma, is one of the most common contaminants due to its prolific growth capacity, and has effectively usurped the identity of numerous other cell lines [4] [14].
Table 1: Examples of Commonly Misidentified Liver Cell Lines (per ICLAC Registry)
| Cell Line | Claimed Tissue/Type | Actual Identity | Contaminating Cell | Number of Publications |
|---|---|---|---|---|
| SMMC-7721 | Human Hepatocellular Carcinoma | Cervical Adenocarcinoma | HeLa | 2,332 [14] |
| BEL-7402 | Human Hepatocellular Carcinoma | Cervical Adenocarcinoma / Colon Carcinoma | HeLa / HCT 8 | 1,371 [14] |
| L-02 (LO2, HL-7702) | Human Normal Hepatic Cells | Cervical Adenocarcinoma | HeLa | 562 [14] |
| Chang Liver | Human Normal Hepatic Cells | Cervical Adenocarcinoma | HeLa | 702 [14] |
| WRL 68 | Human Embryonic Liver Cells | Cervical Adenocarcinoma | HeLa | 248 [14] |
Despite being unmasked as misidentified, these cell lines continue to be used extensively in contemporary research. A recent analysis of recent PubMed entries identified nearly 6,000 publications that used just five of the known misidentified liver cell lines (QGY-7703, BGC-823, BEL-7402, L-02, and WRL-68) [4]. The continued use of falsified cells has a cascading effect, corrupting entire fields of study. It is estimated that approximately 16% of published scientific papers involve misidentified or contaminated cell lines, leading to a body of literature that is fundamentally irreproducible [15]. A peer-review study further revealed that at least 5% of cell lines in manuscripts submitted to a reputable cancer journal were misidentified, and the majority of these rejected papers were subsequently published in other journals without rectification, perpetuating the dissemination of faulty research [14].
The Financial and Operational Toll
The economic consequences of cell line cross-contamination are staggering, affecting individual laboratories, large institutions, and the global research ecosystem.
Table 2: Financial and Operational Impact of Cell Culture Contamination
| Impact Category | Key Statistic | Source/Reference |
|---|---|---|
| Global Annual Cost | Estimated in the hundreds of millions of dollars globally. | [15] |
| Contamination Rates | Ranges from 11% to 30% of mammalian cell cultures; can reach 25-80% in labs without regular monitoring. | [15] |
| Research Waste | Contaminated cultures waste expensive reagents, media, labware, and dedicated researcher time. | [15] |
| Environmental Impact | Contamination increases biohazard waste; labs generate ~5.5 million tons of plastic waste annually. | [15] |
| Therapeutic Development | Contamination in personalized cell therapies (e.g., CAR-T) can discard a patient-specific batch, causing critical treatment delays. | [15] |
Beyond the direct financial losses, contamination incidents impose severe indirect costs. They delay project timelines, jeopardize funding opportunities, and necessitate costly replication studies [15]. The problem also extends into the clinical and commercial sphere. A notable 2009 incident involving viral contamination in a Genzyme bioreactor halted production of an enzyme replacement therapy, causing a drug shortage that left patients with rare diseases without essential medication for months [15]. The expanding biopharmaceutical market, which relies heavily on reliable cell lines, is particularly vulnerable. The global cell line characterization and development market is projected to grow from $2.29 billion in 2025 to $8.38 billion by 2035, underscoring the massive financial value that depends on the integrity of these biological tools [16].
Essential Experimental Protocols for Authentication
Preventing the propagation of misidentified cell lines requires rigorous, routine authentication. The following core methodologies are considered the gold standard.
Short Tandem Repeat (STR) Profiling
- Principle: STR profiling analyzes highly polymorphic regions of the genome containing short, repetitive DNA sequences. The number of repeats at multiple loci is highly variable between individuals, creating a unique genetic fingerprint for each cell line [14] [16].
- Protocol:
- DNA Extraction: Isolate high-quality genomic DNA from the cell line in question.
- PCR Amplification: Amplify a standardized panel of STR loci (e.g., 8 or more core loci) using fluorescently-labeled primers.
- Capillary Electrophoresis: Separate the amplified fragments by size to determine the number of repeats at each locus.
- Data Analysis: Compare the resulting STR profile to reference databases from established cell banks (such as ATCC or DSMZ). A match of 80% or higher is typically required to confirm authenticity.
- Application: This is the international standard for authenticating human cell lines. It is required by many major journals and funding agencies.
Mycoplasma and Viral Testing
- Principle: Cell cultures can be contaminated by microorganisms like mycoplasma and viruses, which do not cause overt turbidity but can drastically alter cell behavior and data [17].
- Protocol:
- PCR-Based Detection: This is the most sensitive and rapid method. Use commercially available kits or design primers against conserved genomic regions of common contaminants like mycoplasma, Epstein-Barr virus (EBV), and others.
- Culture-Based Methods: Inoculate specialized broth and agar media to support mycoplasma growth. While definitive, this method can take up to 28 days.
- Indicator Cell Culture: Stain cells with a DNA-binding fluorochrome (e.g., Hoechst 33258) to visualize mycoplasma DNA adherent to the host cell cytoplasm under fluorescence microscopy.
- Application: Essential for ensuring culture purity, especially for cell lines used in the production of biologics and vaccines [17].
Morphological Verification
- Principle: Regular microscopic examination to confirm that the cell line's morphology (shape, size, growth pattern) is consistent with its tissue of origin and established descriptions.
- Protocol: Capture phase-contrast images of cells at low and high density during multiple passages. Compare these images to reference photographs from authenticated stocks. Significant, persistent deviations may indicate contamination or genetic drift.
- Application: A simple, low-cost, daily monitoring technique that provides an initial alert to potential problems.
The workflow for implementing a robust cell line authentication strategy is outlined below.
The Scientist's Toolkit: Key Research Reagent Solutions
A range of essential tools and reagents is available to support cell line authentication and contamination prevention.
Table 3: Essential Tools and Resources for Cell Line Integrity
| Tool/Resource | Function | Key Examples |
|---|---|---|
| ICLAC Register | Definitive database of known misidentified cell lines to check before use. | ICLAC Register of Misidentified Cell Lines [4] [14] |
| STR Profiling Services | Commercial and academic services providing definitive cell line authentication. | ATCC, DSMZ, Charles River Laboratories [16] |
| Cell Line Repositories | Source of authenticated, low-passage cell lines with provided characterization data. | ATCC, ECACC, RIKEN BRC [16] |
| Mycoplasma Detection Kits | PCR- or enzyme-based kits for rapid detection of mycoplasma contamination. | Commercial kits from vendors like Thermo Fisher, Sigma-Aldrich [17] |
| Automated Cell Culture Monitoring | Reduces operator error and provides real-time data on cell health and contamination. | Systems like CLYTE's Cadmus device [15] |
| Cellosaurus | A comprehensive knowledge resource on cell lines, providing extensive information and cross-references. | Cellosaurus database [4] |
The prevalence and financial impact of cell line cross-contamination present a clear and present danger to biomedical research and drug development. With hundreds of known misidentified lines polluting the scientific literature and incurring global costs in the hundreds of millions of dollars annually, the need for vigilant authentication is no longer optional but a fundamental component of responsible science. By leveraging the available resources—including the ICLAC registry, STR profiling, and routine mycoplasma testing—and adhering to the experimental protocols outlined in this guide, researchers and drug development professionals can protect their work from invalidation, conserve valuable resources, and uphold the integrity of the scientific enterprise.
Cell line cross-contamination represents a critical and persistent challenge in biomedical research, compromising data integrity and wasting valuable scientific resources. This phenomenon occurs when a foreign cell line is inadvertently introduced into another cell culture, eventually overgrowing and replacing the original population. The problem has been recognized for decades, yet it remains alarmingly prevalent in laboratories worldwide. Estimates suggest that 15-20% of cell lines currently in use may not be what they are documented to be, affecting hundreds of labs and leading to problematic papers that cannot be replicated [18] [19]. Among the most prolific contaminants are three notorious cell lines: HeLa (cervical cancer), T-24 (bladder cancer), and HT-29 (colon cancer). These vigorous, fast-growing lines have repeatedly contaminated other cultures, leading to widespread misidentification across diverse research fields. The consequences are particularly severe in drug development, where decisions about new anticancer therapies are sometimes based on work in misidentified cell lines, potentially derailing clinical translation efforts [19]. This technical guide examines the characteristics, contamination mechanisms, and detection methods for these high-profile contaminants, providing researchers with essential knowledge to safeguard their experimental systems.
Scope and Impact of Cross-Contamination
Cross-contamination in cell culture manifests primarily in two forms: interspecies contamination (between different species) and the more insidious intraspecies contamination (within the same species). The latter is particularly problematic as it is more difficult to detect through routine morphological observation. Historical surveys reveal the alarming extent of this issue, with one comprehensive study of 252 human tumor cell lines finding that 18% were cross-contaminated at source, affecting cell lines supplied by 29% of originating laboratories [20].
Table 1: Prevalence of Cross-Contamination in Cell Line Research
| Study Scope | Contamination Rate | Most Common Contaminants | Key Findings |
|---|---|---|---|
| 252 human tumor cell lines from repositories [20] | 18% | HeLa (11 cases), T-24 (4 cases), SK-HEP-1 (4 cases), U-937 (4 cases), HT-29 (3 cases) | Widespread intraspecies contamination; all 5 supposed normal immortalizations were false |
| 278 tumor cell lines from Chinese institutes [21] | 46% overall; 73.2% for Chinese-origin lines | HeLa (46.9% of contaminated cases) | Extremely high contamination in locally established lines; 35/52 misidentified Chinese lines were HeLa |
| International Cell Line Authentication Committee database [19] | 438 false cell lines with no evidence of authentic stock | HeLa (24% of false cell lines) | 138 different contaminating cell lines identified; 50 cell lines cross-contaminated by another species |
The impact of these contaminations extends far beyond the originally affected laboratories. Misidentified cell lines continue to be used in publications, with one estimate suggesting that nearly 33,000 papers may have included misidentified cell lines [19]. This creates a cascading effect through the scientific literature, as other researchers read these publications and subsequently use the compromised cell lines for their own work. The problem is self-perpetuating unless systematic authentication measures are implemented.
High-Profile Contaminants: Characteristics and Case Studies
HeLa: The Most Prolific Contaminant
First established in 1951 from a cervical adenocarcinoma, HeLa cells represent the first immortal human cell line and remain one of the most commonly used in research worldwide [18]. Their notoriety as contaminants stems from their vigorous growth properties, enabling them to easily overgrow slower-growing cultures. HeLa contamination was first systematically documented by Stanley Gartler in 1966 and brought to wider scientific attention by Walter Nelson-Rees in the 1970s [19].
HeLa cells are responsible for approximately 24% of false cell lines in the ICLAC database [19]. A 2017 study of 278 tumor cell lines found that HeLa accounted for 46.9% of cross-contamination cases, affecting 31 different cell lines [21]. The pervasiveness of HeLa contamination continues to the present day, as evidenced by a 2024 correspondence noting that multiple nasopharyngeal carcinoma (NPC) cell lines (CNE1, CNE2, SUNE1, 6-10B, and 5-8F) still show genetic profiles identical to HeLa, despite this issue being recognized since 2008 [12].
Case Study: HES Cell Contamination A 2014 study demonstrated HeLa contamination of the human endometrial epithelial cell line HES. Researchers discovered that HES cells showed molecular identity with HeLa cells at 9 unique genetic loci through short tandem repeat (STR) analysis. Further investigation revealed that the source of contamination was WISH cells (human amnion epithelium), which were simultaneously grown in the laboratory and are themselves known to be HeLa-contaminated. This case highlights how contamination can spread between cell lines within a laboratory setting, even when researchers are not directly working with HeLa cells [11].
T-24: Bladder Cancer-Derived Contaminant
T-24 is a widely used bladder cancer cell line that has emerged as a significant contaminant in urothelial cancer research. It ranks among the most common contaminants after HeLa, with documented cases of cross-contamination affecting multiple cell lines [20].
Case Study: UROtsa Cross-Contamination A 2013 investigation revealed that a UROtsa stock (an immortalized human urothelial cell line used to study toxicology and bladder carcinogenesis) had been cross-contaminated with T-24 cells. Researchers made this discovery when unusual molecular properties prompted identity verification. STR profiling unequivocally identified the UROtsa stock as T-24, differing from authentic UROtsa controls. The study further demonstrated that the contaminating T-24 cell line showed moderate changes in DNA methylation patterns and mRNA expression even after long-term culture of up to 56 weeks, while miRNAs and chromosome numbers varied more markedly [22] [23].
This case is particularly significant because UROtsa is frequently used to study mechanisms of carcinogenesis and early molecular changes during malignant transformation. Using cancer cell lines like T-24 (which already represent late-stage malignancy) to study early transformation events represents a fundamental methodological flaw that compromises research validity [23].
HT-29: Colon Cancer-Derived Contaminant
HT-29 is a human colon adenocarcinoma cell line commonly used in gastrointestinal research and cancer biology. Like T-24, it has been identified as a common contaminant that can silently take over cultures believed to represent other cancer types [19]. Despite its role as a contaminant, HT-29 remains a valuable research tool when properly authenticated, as evidenced by its use in studies of phage-bacteria interactions in gut models [24].
Table 2: Characteristics of Major Contaminating Cell Lines
| Cell Line | Origin | Key Growth Properties | Commonly Misidentified As | Documented Contamination Cases |
|---|---|---|---|---|
| HeLa | Cervical adenocarcinoma | Vigorous growth, high proliferation rate | Various cell types including breast, prostate, thyroid cancers | 24% of false cell lines in ICLAC database [19] |
| T-24 | Bladder carcinoma | Fast-growing epithelial cells | UROtsa (normal urothelium), other bladder and urothelial lines | Multiple independent cell lines [20] |
| HT-29 | Colorectal adenocarcinoma | Epithelial morphology, rapid duplication | Various cancer types including prostate, thyroid cancers | 3 documented false lines in survey [20] |
Mechanisms and Pathways of Contamination
Cell line cross-contamination typically occurs through procedural errors during routine cell culture work. The diagram below illustrates the primary pathways through which contamination spreads and the critical detection points.
The contamination process typically begins when a single cell from a vigorous line is introduced into another culture, often during establishment phases when the original cells show little growth. This contaminant can then outgrow the original culture without detection [19]. Common laboratory practices that facilitate contamination include:
- Simultaneous culture of multiple cell lines in the same workspace [11]
- Shared reagents and equipment (pipettes, media, trypsin) without proper decontamination
- Generation of aerosols during pipetting or bottle opening
- Improper labeling of cryovials and culture vessels [18]
- Lack of quarantine procedures for newly acquired cell lines
HeLa and other rapidly dividing tumor cells possess a selective growth advantage that allows them to dominate mixed cultures over time. This phenomenon is particularly problematic during the establishment of new cell lines, when primary cells may undergo a period of slow growth or senescence before a stable line emerges [19].
Detection Methods and Authentication Protocols
Short Tandem Repeat (STR) Profiling
STR profiling has emerged as the gold standard method for human cell line authentication. This technique examines highly polymorphic regions of the genome containing short, repetitive DNA sequences that vary in length between individuals. The International Cell Line Authentication Committee (ICLAC) maintains a database of STR profiles for comparison [18].
Experimental Protocol: STR Profiling
- DNA Isolation: Extract high-quality genomic DNA from approximately 10^6 cells grown to confluence in 100mm dishes [11]
- PCR Amplification: Simultaneously amplify multiple STR loci using commercial kits (e.g., StemElite ID System, Promega)
- Fragment Analysis: Separate amplified products by capillary electrophoresis to determine fragment sizes
- Data Interpretation: Compare resulting DNA fingerprint to reference databases (ATCC, DSMZ)
- Authentication: Match at ≥80% of loci suggests identity; discrepancies indicate possible contamination [21]
STR analysis unequivocally identified HES cells as HeLa by demonstrating identical genotypes at 9 genetic loci (AMEL, CSF1PO, D13S317, D16S539, D5S818, D7S820, TH01, TPOX, and vWA) [11]. Similarly, STR profiling revealed that supposed UROtsa cells showed complete identity with T-24 bladder cancer cells [22].
Supplementary Authentication Methods
While STR profiling is the primary method for intraspecies authentication, several complementary techniques provide additional verification:
Isoenzyme Analysis: This historical method detects species-specific differences in enzyme mobility via electrophoresis. While less discriminatory than DNA-based methods, it remains useful for detecting interspecies contamination [18].
Karyotyping: Chromosomal analysis reveals gross genetic abnormalities and species-specific chromosome patterns. However, chromosome numbers can vary in cultured cells, making interpretation challenging [18].
DNA Methylation Analysis: As demonstrated in the UROtsa/T-24 case, DNA methylation patterns of tumor suppressor genes (RARB, PGR, RASSF1, CDH1, etc.) can distinguish between cell lines with similar genetic backgrounds [22].
The workflow below illustrates the comprehensive approach to cell line authentication:
Table 3: Essential Resources for Cell Line Authentication
| Resource Type | Specific Examples | Application/Function | Key Features |
|---|---|---|---|
| Reference Databases | ICLAC Register of Misidentified Cell Lines [12]; ATCC STR Database [18]; DSMZ Database | Comparison of STR profiles; Identification of known contaminants | Publicly accessible; Regularly updated; Comprehensive listings |
| STR Profiling Kits | StemElite ID System (Promega) [11]; PowerPlex Systems | Multiplex PCR amplification of STR loci | Standardized markers; High discrimination power; Database compatibility |
| Cell Line Repositories | ATCC; ECACC; DSMZ | Source of authenticated cell lines; STR profiling services | Quality control; Authentication testing; Proper documentation |
| Analysis Software | GeneMapper; GeneMarker | Fragment analysis for STR data interpretation | Peak identification; Allele calling; Quality metrics |
| Online Tools | ATCC STR Database Alignment Tool [18] | Comparison of user STR data to reference profiles | Percentage match calculations; Match interpretation guidelines |
Cell line cross-contamination represents a significant threat to research integrity, with HeLa, T-24, and HT-29 ranking among the most problematic contaminants. The persistence of this issue decades after its initial identification underscores the need for systematic approaches to cell line authentication. Based on documented cases and expert recommendations, the following best practices are essential:
- Source cell lines from reputable repositories that provide authentication data
- Implement regular authentication testing using STR profiling, especially when establishing new cultures, before freezing down stocks, and prior to key experiments
- Maintain meticulous records of cell line sources, passage numbers, and authentication results
- Practice good cell culture technique including spatial separation of different lines, regular equipment decontamination, and use of dedicated reagents
- Validate cell line identity before publication and include authentication methods in materials and sections
Major journals and funding agencies increasingly require cell line authentication, reflecting growing recognition of this fundamental quality issue [18]. By adopting rigorous authentication practices and maintaining vigilance against contamination, researchers can ensure the validity of their cellular models and enhance the reproducibility of biomedical research.
Cell line cross-contamination represents a critical and persistent challenge in biomedical research, with profound implications for data integrity and scientific reproducibility. This phenomenon occurs when a cell culture is inadvertently replaced by or mixed with another, often more aggressive, cell line [25]. The problem, recognized as early as the 1950s, has worsened over decades despite increasing awareness, turning many researchers into both victims and perpetrators of a systemic issue that undermines research validity [25] [26]. The consequences extend beyond individual experiments to affect entire research trajectories, drug development pipelines, and the credibility of scientific evidence.
The widespread nature of this problem threatens the very foundation of biomedical research. When cells used in experiments do not authentically represent the intended biological system, resulting data becomes biologically misleading and irreproducible [4]. This whitepaper examines the quantifiable impact of cell line cross-contamination, details the mechanisms through which it compromises research outcomes, and presents standardized methodologies for authentication that researchers, journals, and funding agencies must implement to preserve scientific integrity.
Quantifying the Problem: Prevalence and Impact
The scale of cell line misidentification is substantial, with recent estimates indicating that between 20% and 36% of cell lines used in research are contaminated or misidentified [27]. The International Cell Line Authentication Committee (ICLAC) maintains a dedicated registry of known problematic cell lines, which in its version 13 (April 2024) lists 593 misidentified or cross-contaminated cell lines [4].
Commonly Misidentified Cell Lines
HeLa cells, derived from cervical cancer tissue in the 1950s, represent one of the most common contaminants due to their prolific growth capacity [4]. The table below illustrates several frequently misidentified cell lines used in liver and gastric cancer research, their intended characteristics, and their actual identity:
Table 1: Examples of Misidentified Cell Lines from the ICLAC Registry
| Cell Line | Claimed Tissue/Type | Actual Identity | Actual Tissue/Type |
|---|---|---|---|
| BEL-7402 | Human liver, hepatocellular carcinoma | HeLa/HCT 8 | Cervical adenocarcinoma/colon carcinoma [4] |
| L-02 | Human liver, normal hepatic cells | HeLa | Cervical adenocarcinoma [4] |
| QGY-7703 | Human liver, hepatocellular carcinoma | HeLa | Cervical adenocarcinoma [4] |
| WRL 68 | Human liver, embryonic cells | HeLa | Cervical adenocarcinoma [4] |
| BGC-823 | Human gastric carcinoma | HeLa | Cervical adenocarcinoma [4] |
| Chang Liver | Human liver, normal hepatic cells | HeLa | Cervical adenocarcinoma [4] |
The use of misidentified cell lines has propagated extensively through the scientific literature. Research by Christopher Korch identified nearly 5,800 articles that may have confused HeLa for HEp-2 cells, and another 1,336 articles that may have mixed up HeLa with INT 407 cells [27]. Collectively, these 7,000-plus papers have been cited approximately 214,000 times, embedding potentially erroneous findings into the scientific knowledge base [27].
The financial impact is equally staggering. The total cost of irreproducible preclinical research is estimated at $28.2 billion annually in the United States alone. Biological reagents and reference materials, including problematic cell lines, account for 36.1% of this cost, representing a waste of approximately $10 billion per year [28].
Consequences for Research Validity and Reproducibility
When research is conducted with misidentified cell lines, the resulting data reflects the biology of the contaminant rather than the intended tissue or disease model. This fundamental disconnect generates spurious findings that can misdirect research trajectories for years. For instance, studies using HeLa-contaminated liver cell lines (e.g., L-02, BEL-7402) have drawn incorrect conclusions about liver-specific disease mechanisms, drug metabolism, and gene regulation [4]. The table below summarizes the primary domains affected by such invalid data:
Table 2: Research Domains Compromised by Cell Line Misidentification
| Research Domain | Nature of Compromised Data | Potential Consequences |
|---|---|---|
| Disease Mechanisms | Incorrect signaling pathways and molecular profiles | Misunderstanding of disease biology; misplaced therapeutic targets [4] |
| Drug Discovery & Screening | Invalid efficacy and toxicity profiles | Failure in clinical trials; abandonment of potentially useful compounds [26] |
| Gene Expression & Regulation | Tissue-specific expression patterns attributed to wrong cell type | Flawed molecular signatures and biomarkers [4] |
| Preclinical Cancer Research | Drug responses from incorrect cancer type | Invalidated therapeutic approaches [4] [26] |
The Reproducibility Crisis
Cell line cross-contamination represents a significant contributor to the broader reproducibility crisis in biomedical science. The inherent variability of biological materials is compounded when the fundamental research tool—the cell line itself—is not what researchers assume it to be [28]. This problem is exacerbated by genetic drift, where extended cell culture leads to accumulated genetic changes that further compromise reproducibility and clinical translation [28].
The diagram below illustrates how cell line misidentification initiates a cascade of consequences that ultimately undermine the entire research ecosystem:
Methodologies for Authentication and Quality Control
Preventing the detrimental consequences of cell line misidentification requires rigorous implementation of authentication technologies. The following section details standardized experimental protocols for verifying cell line identity.
Short Tandem Repeat (STR) Profiling
Purpose: STR profiling is the gold standard method for authenticating human cell lines. It analyzes highly polymorphic regions of the genome containing short, repetitive DNA sequences to create a unique genetic fingerprint for each cell line [4].
Protocol:
- DNA Extraction: Isolate high-quality genomic DNA from the cell line of interest using standard phenol-chloroform extraction or commercial kits.
- PCR Amplification: Amplify 8-24 core STR loci using fluorescently labeled primers in a multiplex PCR reaction. Common loci include D5S818, D13S317, D7S820, D16S539, vWA, TH01, TPOX, and CSF1PO.
- Capillary Electrophoresis: Separate PCR products by size using capillary electrophoresis and detect fluorescent signals.
- Data Analysis: Compare the resulting STR profile to reference databases (e.g., ATCC, DSMZ). A match is typically defined as ≥80% alignment with the reference profile.
- Interpretation: Document the authentication date and passage number. Repeat testing every 3-6 months or after every 10 passages in culture.
Morphological Verification
Purpose: Regular microscopic examination provides a preliminary assessment of cell line characteristics and can reveal obvious contamination.
Protocol:
- Culture Observation: Examine living cells under phase-contrast microscopy for expected morphological characteristics (e.g., epithelial-like vs. fibroblast-like).
- Documentation: Capture digital images at regular intervals to establish a morphological baseline.
- Staining Techniques: Perform histological staining (e.g., H&E) or immunohistochemistry for tissue-specific markers to confirm expected phenotypes.
- Comparison: Compare morphology with reference images from authenticated stocks of the same cell line.
Species Verification by Isoenzyme Analysis
Purpose: To detect interspecies contamination by analyzing species-specific electrophoretic mobility patterns of intracellular enzymes.
Protocol:
- Cell Lysis: Prepare cell lysates under nondenaturing conditions.
- Electrophoresis: Separate enzymes by mobility on agarose or cellulose acetate gels.
- Enzyme Detection: Use specific enzyme activity stains to visualize patterns for glucose-6-phosphate dehydrogenase, lactate dehydrogenase, and malate dehydrogenase.
- Pattern Matching: Compare mobility patterns to species-specific controls to identify the species present in the culture [26].
The workflow below outlines a comprehensive cell line authentication strategy:
The Scientist's Toolkit: Research Reagent Solutions
Implementing rigorous authentication requires specific resources and tools. The following table details essential materials and databases for maintaining cell line integrity:
Table 3: Essential Resources for Cell Line Authentication
| Resource/Tool | Function | Application in Research |
|---|---|---|
| STR Profiling Kits | Multiplex PCR systems for DNA fingerprinting | Core authentication method for human cell lines [4] |
| ICLAC Registry | Database of misidentified cell lines | Due diligence before acquiring or using cell lines [4] |
| Cellosaurus | Knowledge resource on cell lines | Reference for cell line characteristics and authentication data [4] |
| Research Resource Identification Portal | Standardized reagent identification | Consistent reporting of cell lines in publications [4] |
| Precision-Engineered Cell Mimics | Synthetic controls with low variability | Reduce biological variability in assays; instrument calibration [28] |
| SciScore | Software for methods assessment | Automated evaluation of rigor criteria in manuscripts, including authentication [4] |
Cell line cross-contamination represents a critical threat to research integrity, generating spurious data and exacerbating the reproducibility crisis. The consequences permeate every aspect of biomedical science, from misguided basic research to failed clinical translations, wasting substantial resources and eroding scientific trust. The solution requires a collaborative effort between individual researchers, institutions, cell banks, journals, and funding agencies to implement and enforce standardized authentication practices. By adopting the methodologies and resources outlined in this whitepaper, the scientific community can safeguard research validity, enhance reproducibility, and ensure that future biomedical advancements are built upon a foundation of authentic biological materials.
In biomedical research, cell lines serve as fundamental tools for investigating disease mechanisms, drug discovery, and preclinical testing. However, a hidden problem threatens the validity of this research: cross-contamination and misidentification of cell lines. Cross-contamination occurs when a foreign cell line is inadvertently introduced into another culture, often through laboratory errors such as using the same pipette or media between different cell lines. When these contaminated cultures proliferate and replace the original cell line, they become misidentified—meaning the cells no longer correspond to their claimed donor or tissue of origin [29] [30]. Consequently, research data derived from these false models can be misleading or entirely false, leading to scientific confusion, wasted resources, and compromised therapeutic development.
The International Cell Line Authentication Committee (ICLAC) was established to combat this issue by promoting awareness, authentication testing, and providing critical resources to the scientific community. A cornerstone of these efforts is the ICLAC Register of Misidentified Cell Lines, a curated database that catalogs cell lines known to be cross-contaminated or otherwise misidentified [31]. This whitepaper details the scope of the problem, the content and application of the ICLAC Registry, and outlines the methodologies and best practices that researchers, scientists, and drug development professionals must adopt to ensure the integrity of their work in cell biology.
The ICLAC Registry: Scope, Composition, and Quantitative Analysis
The ICLAC Register of Misidentified Cell Lines is a dynamically curated resource that lists cell lines conclusively identified as misidentified. As of its latest version (version 13, released in April 2024), the register catalogs 593 cell lines [29]. The registry's structure and quantitative data offer profound insights into the nature and scale of the problem.
The following table breaks down the comprehensive statistics provided by ICLAC, illustrating the various categories of misidentification.
Table 1: Quantitative Analysis of Misidentified Cell Lines in the ICLAC Registry (Version 13, April 2024)
| Category of Misidentification | Number of Cell Lines | Details and Examples |
|---|---|---|
| Total Misidentified Cell Lines | 593 | The complete list of cell lines recognized as misidentified [29]. |
| Misidentified with No Known Authentic Stock | 545 | These cell lines are listed in Table 1 of the registry. Once contaminated, the original cell line is often lost permanently [29]. |
| Cell Lines with Rediscovered Authentic Stock | 48 | Listed separately in Table 2 of the registry. These are cases where authentic stocks of the original cell line have been found or re-established [29]. |
| Contaminant Identity Unknown | 78 | The cell line does not match its purported donor, but the specific contaminating cell line is unknown [29]. |
| Interspecies Contamination | 70 | Contamination where the cell line comes from a different species than claimed (e.g., a human cell line contaminated with mouse cells) [29]. |
| Non-Human Intraspecies Contamination | 9 | Contamination where a non-human cell line is contaminated by another cell line from the same species [29]. |
| Most Common Contaminants | 157 different contaminants | The identity of the contaminating cell lines is diverse, but a few are overwhelmingly common [29]. |
A deeper analysis of the most frequent contaminants reveals a striking pattern of dominance by a few prolific cell lines, which is critical information for risk assessment.
Table 2: Most Common Contaminating Cell Lines Listed in the ICLAC Registry
| Contaminating Cell Line | Number of Affected Cell Lines | Notes |
|---|---|---|
| HeLa | 145 | The oldest and most notorious human cell line, derived from Henrietta Lacks in 1951, is responsible for a vast proportion of cross-contamination incidents [29]. |
| T-24 | 21 | A human bladder carcinoma cell line that is a common contaminant [29]. |
| M14 | 18 | A cell line related to the MCF-7 breast cancer cell line, itself a known common contaminant [29]. |
The data in these tables underscore that cross-contamination is not a rare anomaly but a widespread issue affecting hundreds of cell lines. The dominance of HeLa as a contaminant highlights its aggressive growth properties, which allow it to easily overgrow other cultures. For researchers, the primary takeaway is that relying on the ICLAC Registry for due diligence is a non-negotiable first step in experimental design.
Methodologies for Cell Line Authentication
Knowing which cell lines are problematic is only half the solution. Proactive authentication of cell lines in use is essential. The consensus method for authenticating human cell lines is Short Tandem Repeat (STR) profiling. This technique PCR-amplifies specific, highly variable genomic regions and compares the resulting DNA "fingerprint" to a reference profile [30].
The following diagram illustrates the core workflow for cell line authentication and the role of the ICLAC Registry within it.
The experimental protocol for STR profiling and authentication involves several critical steps:
- DNA Extraction: High-quality genomic DNA is isolated from the cell line to be tested.
- PCR Amplification: Fluorescently labeled primers are used to amplify multiple specific STR loci (e.g., the 8 core loci recommended by ANSI/ATCC ASN-0002-2011).
- Capillary Electrophoresis: The amplified PCR fragments are separated by size, and the fluorescent data is captured to generate an electropherogram.
- Data Analysis and Allele Calling: Software analyzes the electropherogram to call the alleles at each locus, producing a numeric STR profile.
- Profile Comparison: The test profile is compared against a reference profile from an authenticated stock (e.g., from the original cell bank like ATCC or DSMZ). Researchers can use online STR matching tools provided by databases like CLASTR (Cellosaurus), DSMZ, or ATCC to perform this comparison objectively [32] [30].
- Match Interpretation: The ICLAC Match Criteria Worksheet provides guidelines to determine if two STR profiles are related. A match at 80% or more of the alleles is typically required to declare a cell line authentic. A lower match percentage indicates the cell line is likely misidentified [30].
Combating misidentification requires a suite of tools and databases. The table below details key resources that form an essential toolkit for any laboratory working with cell lines.
Table 3: Research Reagent Solutions and Resources for Cell Line Authentication
| Resource Name | Type | Function and Utility |
|---|---|---|
| ICLAC Register of Misidentified Cell Lines [29] | Database | The primary list to check for known problematic cell lines before purchase or use. |
| Cellosaurus [32] | Knowledge Resource | A comprehensive resource of information for ~120,000 cell lines, including STR profiles and cross-references. |
| CLASTR [32] | Search Tool | A tool to compare an STR profile against those in Cellosaurus to find similar cell lines and potential contaminants. |
| DSMZ/ATCC STR Databases [32] [30] | Database & Search Tool | Repositories of certified STR profiles with integrated tools to compare user-submitted data for match verification. |
| NCBI BioSample Database [32] [30] | Database | Archives STR profiles and descriptions for thousands of cell lines, as submitted by cell line repositories. |
| STR Profiling Kit | Laboratory Reagent | A commercial kit containing primers and reagents for multiplex PCR of standard STR loci. |
| Research Resource Identifiers (RRIDs) [33] | Identifier | A system to uniquely identify research resources, including cell lines, in publications to improve reproducibility (e.g., RRID:CVCL_0032). |
The adoption of Research Resource Identifiers (RRIDs) is a critical cultural shift supporting these efforts. The Resource Identification Initiative, launched in 2014, encourages authors to include RRIDs for key biological resources in their manuscripts. This practice, which is machine-readable, free, and consistent across publishers, dramatically improves the identifiability of research resources in the literature and allows for better tracking of cell line usage [33].
The ICLAC Registry is more than a simple list; it is a critical early-warning system and a foundational component of the scientific quality control ecosystem. Its existence underscores a sobering reality: the integrity of vast domains of cell-based research is perpetually at risk from cross-contamination. For the individual researcher, consulting the registry and implementing routine STR authentication are fundamental responsibilities. For the scientific community at large, the integration of RRIDs into publications and the enforcement of authentication mandates by journals and funders are powerful drivers for cultural change [33] [30].
The path forward requires a multi-faceted approach. First, education must emphasize the severe consequences of using misidentified lines. Second, authentication must be embedded as a non-negotiable step in cell culture practice, not an optional extra. Finally, reporting must be transparent, with the use of RRIDs and explicit descriptions of authentication methods becoming standard in materials and methods sections. By embracing these practices, researchers, scientists, and drug development professionals can safeguard their work, ensure the efficient use of resources, and fortify the very foundation of biomedical research upon which future therapies depend.
Detecting the Invisible: Essential Methods for Cell Line Authentication
Cell lines serve as indispensable tools in biomedical research, drug discovery, and therapeutic development. However, their scientific utility is critically dependent on one often-overlooked factor: identity assurance. Cross-contamination and misidentification of cell lines represent a pervasive, systemic problem that undermines research integrity and wastes valuable resources. Studies consistently reveal alarming contamination rates—one comprehensive analysis of 482 human tumor cell lines found that 20.5% were incorrectly identified, comprising intra-species cross-contamination (14.5%), inter-species cross-contamination (4.4%), and mixtures of multiple cell lines (1.7%) [34]. The HeLa cell line, originally derived from a cervical adenocarcinoma in 1951, has become a particularly problematic contaminant; currently, at least 209 cell lines in the Cellosaurus database are misidentified and have been shown to be HeLa [35]. The consequences of using misidentified cell lines extend far beyond laboratory walls, potentially invalidating years of research, misdirecting therapeutic development, and ultimately hindering progress in understanding disease mechanisms.
STR Profiling: Methodology and Technical Foundation
Fundamental Principles of STR Analysis
Short Tandem Repeats (STRs) are short DNA sequences, typically 2 to 6 base pairs in length, that are repeated in tandem and scattered throughout the genome [36]. These sequences demonstrate high variability between individuals in the number of repeat units, making them ideal genetic markers for identification purposes [35]. The core principle of STR profiling leverages this natural variation to create a unique genetic "fingerprint" for each cell line, enabling researchers to verify identity and detect contamination.
The technology draws heavily from forensic science, where STR analysis has been refined for human identification. For cell line authentication, the approach typically examines multiple STR loci simultaneously through multiplex PCR amplification. The resulting DNA profile allows for unambiguous authentication of human cell line samples when compared to reference databases or known standards [37].
Standardized STR Markers and Core Loci
Authentication systems typically target a specific set of STR loci to ensure consistency and comparability across laboratories. The Promega PowerPlex 16HS system, commonly used for this purpose, examines 15 STR loci plus the amelogenin gene for sex determination [38]. These loci include the 13 CODIS forensic markers plus Penta D and Penta E, providing a robust discrimination power [38].
The ANSI/ATCC ASN-0002 standard provides comprehensive specifications for STR profiling methodology, data analysis, quality control, and interpretation [37]. This standardization is crucial for ensuring that authentication results are consistent, reliable, and comparable across different testing facilities and over time.
Workflow for Cell Line Authentication
The complete STR authentication process follows a systematic workflow from sample preparation to data interpretation. This workflow can be visualized as follows:
Sample Preparation: The process begins with the collection of approximately 2 million cells, which are pelleted, washed, and processed for DNA extraction [38]. For laboratories working with viral or recombinant cell lines, submission of purified DNA is often required instead of cell pellets.
DNA Extraction and Quantification: DNA is typically extracted using automated systems such as the Promega Maxwell 16 Instrument with specialized DNA extraction kits [38]. The extracted DNA is then quantified to ensure adequate concentration (ideally around 50ng/μL) for subsequent analysis.
Multiplex PCR Amplification: This crucial step simultaneously amplifies the targeted STR loci using fluorescently-labeled primers in a single reaction mixture [35]. The PowerPlex 16 HS System co-amplifies 15 STR loci and the amelogenin sex determinant marker, with each set of primers labeled with different fluorescent dyes (fluorescein, JOE, or TMR) for detection [38].
Capillary Electrophoresis and Fragment Analysis: The amplified PCR products are separated by size using capillary gel electrophoresis on instruments such as the ABI 3500xl Genetic Analyzer [38]. Internal size standards are included to ensure accurate fragment sizing, and the GeneMapper software converts the data into interpretable peaks corresponding to specific alleles at each locus.
Interpretation and Analysis of STR Data
Analytical Approaches and Match Algorithms
Interpreting STR data requires specialized algorithms to determine the relationship between the tested cell line and reference profiles. Two primary algorithms are commonly used for authentication:
Tanabe Algorithm: This method calculates similarity as (2 × number of shared alleles) / (total alleles in query profile + total alleles in reference profile) × 100%. It applies strict thresholds: ≥90% indicates relatedness (same donor), 80-90% is ambiguous, and <80% indicates unrelated [39].
Masters Algorithm: This approach uses the formula: (number of shared alleles / total number of alleles in query profile) × 100%. It employs slightly more lenient thresholds: ≥80% indicates relatedness, 60-80% suggests mixed/uncertain results, and <60% indicates unrelated [39].
Essential Research Reagent Solutions
Successful STR profiling depends on specific, high-quality reagents and systems. The following table details key components essential for the authentication process:
| Reagent/System | Function | Specific Example |
|---|---|---|
| PowerPlex 16 HS System | Multiplex PCR amplification of 15 STR loci + Amelogenin | Promega [38] |
| Maxwell 16 LEV Blood DNA Kit | Automated DNA extraction from cell pellets | Promega [38] |
| ABI 3500xl Genetic Analyzer | Capillary electrophoresis for fragment separation | Applied Biosystems [38] |
| GeneMapper ID-X Software | STR profile analysis and allele calling | Applied Biosystems [38] |
| SiFaSTR 23-plex System | Forensic-grade STR analysis with 21 autosomal STRs + 2 sex markers | Academy of Forensic Sciences (China) [39] |
Contamination Detection and Profile Interpretation
STR profiling can detect intra-species contamination with sensitivity as low as 2-5% [36]. The electropherogram output provides visual indicators of potential contamination:
- Additional peaks at STR loci beyond the expected one (homozygous) or two (heterozygous) alleles suggest mixed cell populations [38].
- Significant peak height imbalances may indicate contamination, though this requires careful interpretation against established thresholds [35].
- Unexpected allele patterns that deviate from reference profiles suggest misidentification [34].
The interpretation of STR profiles must account for genetic instability that can occur in cell lines over time, including:
- Loss of heterozygosity (L): Disappearance of an allele compared to the reference [39].
- Additional alleles (Aadd): Appearance of extra alleles at a locus [39].
- New alleles (Anew): Replacement of original alleles with different ones [39].
Implementation in Research Practice
Authentication Frequency and Best Practices
Regular authentication is essential for maintaining cell line integrity throughout research projects. Recommended testing intervals include [38]:
- Upon receiving a cell line from another source
- Prior to freezing down stocks
- Every other month during active culture
- Before undertaking critical experiments
- Prior to manuscript submission for publication
Quantitative Evidence of Cross-Contamination
The scope and impact of cell line misidentification is demonstrated by multiple large-scale studies:
| Study Context | Sample Size | Misidentification Rate | Primary Contamination Types |
|---|---|---|---|
| Human tumor cell lines in China [34] | 482 cell lines | 20.5% (99/482) | Intra-species (14.5%), Inter-species (4.4%), Mixtures (1.7%) |
| Academic research submissions (2017) [38] | Not specified | 28.8% non-match rate | Misidentified lines (26.3%), Contamination (2.5%) |
| Academic research submissions (2019) [38] | Not specified | 3.8% non-match rate | Demonstrated improvement with regular testing |
Limitations and Complementary Techniques
While STR profiling represents the gold standard for human cell line authentication, it has limitations that researchers must recognize:
- Species Specificity: Standard human STR kits do not effectively authenticate non-human cell lines, requiring specialized approaches such as adapted STR panels for species like African green monkeys [40] or DNA barcoding [41].
- Detection Sensitivity: Most STR assays cannot reliably detect contamination below 2-5% [36], leaving low-level contaminants potentially undetected.
- Genetic Drift: Cell lines may accumulate genetic changes over extended culture periods, resulting in altered STR profiles that complicate interpretation [39].
To address these limitations, comprehensive quality control should include:
- Species identification by PCR to detect inter-species contamination [34]
- Mycoplasma testing to detect this common microbial contaminant [41]
- Morphological monitoring to identify obvious phenotypic changes [34]
Short Tandem Repeat profiling remains the unequivocal gold standard for human cell line authentication, providing a robust, standardized method for verifying cell line identity and detecting contamination. The persistent problem of cell line misidentification—affecting approximately 18-36% of cell lines used in research—demands rigorous authentication practices [38]. Implementation of regular STR profiling, following established standards such as ANSI/ATCC ASN-0002 and utilizing validated reagent systems, is essential for protecting research integrity, ensuring reproducible results, and maintaining scientific progress. As research becomes increasingly complex and dependent on cell-based models, commitment to rigorous cell line authentication represents not merely a technical formality, but a fundamental ethical imperative for the scientific community.
The integrity of biological models forms the foundation of reproducible biomedical research, particularly in drug development. Cross-contamination, the accidental introduction of cells from one culture to another, represents a critical threat to this integrity [42]. Initially resulting in a mixture of cultures, fast-growing contaminant cells—often from aggressive tumor lines like HeLa—can completely overgrow an original culture within several passages, leading to misidentified cell lines where the culture no longer corresponds to its supposed donor [42]. Astonishingly, it has been estimated that approximately 20% of cell lines are misidentified, and the International Cell Line Authentication Committee (ICLAC) currently lists 576 misidentified or cross-contaminated cell lines in its register [5] [43]. The consequences are severe: contaminated cell lines produce false and irreproducible results, compromising scientific validity, wasting resources, and potentially derailing drug development pipelines. This technical guide examines two classical techniques—karyotyping and isoenzyme analysis—that serve as essential tools for detecting cross-contamination and authenticating cell lines.
Technical Foundation of the Techniques
Karyotyping: Chromosomal Analysis
Karyotyping is the process of pairing and ordering all the chromosomes of an organism, providing a genome-wide snapshot of an individual's chromosomes [44]. A karyotype describes the chromosome count of an organism and the physical characteristics of chromosomes under a light microscope, including their length, centromere position, banding pattern, and differences between sex chromosomes [45]. Karyotyping is a cytogenetic technique that combines light microscopy and photography, typically during metaphase of the cell cycle when chromosomes are most condensed and visible [45].
Table 1: Human Chromosome Classification Based on Karyogram Characteristics
| Group | Chromosomes | Morphological Features |
|---|---|---|
| A | 1-3 | Large, metacentric or submetacentric |
| B | 4-5 | Large, submetacentric |
| C | 6-12, X | Medium-sized, submetacentric |
| D | 13-15 | Medium-sized, acrocentric, with satellite |
| E | 16-18 | Small, metacentric or submetacentric |
| F | 19-20 | Very small, metacentric |
| G | 21-22, Y | Very small, acrocentric (21, 22 with satellite) |
Isoenzyme Analysis: Protein Electrophoresis
Isoenzyme analysis is a traditional method for cell authentication that takes advantage of the different banding patterns and relative migration distances for individual isoforms of intracellular enzymes with similar substrate specificity but different molecular structures [46]. The technique evaluates electrophoretic mobility patterns of cytoplasmic enzymes on agarose gels to identify species of origin and detect interspecies contamination [47]. Unexpected extra bands in a gel for one or more isoenzymes indicate the presence of a second cell type in the mixture [46].
Experimental Protocols and Methodologies
Detailed Karyotyping Protocol
The standard karyotyping protocol involves multiple precise steps to obtain metaphase chromosomes for analysis [44]:
Figure 1: Karyotyping experimental workflow from sample collection to analysis.
Cell Culture and Division Arrest: Cells are cultured and arrested during cell division, typically in metaphase or prometaphase when chromosomes are most condensed, using a solution of colchicine [45] [44]. For human studies, white blood cells are frequently used because they are easily induced to divide and grow in tissue culture [45].
Hypotonic Treatment: Cells are treated with a hypotonic solution, causing them to swell and the chromosomes to spread apart [44].
Fixation: Cells are fixed using Carnoy's solution (3:1 methanol:acetic acid) to preserve chromosomal structure [44].
Slide Preparation and Staining: Fixed cells are dropped onto glass slides, causing chromosomes to spread. Staining is then performed using various banding techniques [44].
Chromosome Banding Techniques
Chromosome banding enables the identification of individual chromosomes and the detection of structural abnormalities. The principal banding techniques are classified based on their staining properties [44]:
Table 2: Chromosome Banding Techniques and Applications
| Technique | Staining Method | Target Regions | Primary Applications |
|---|---|---|---|
| Q-banding | Quinacrine mustard (fluorescent) | AT-rich regions | Study of chromosome heteromorphism; where G-banding is not applicable |
| G-banding | Giemsa stain (methylene blue, eosin, azure) | Sulfur-rich DNA regions | Standard for identifying chromosomal abnormalities and gene mapping |
| C-banding | Giemsa stain (after specific treatments) | Centromeric heterochromatin | Identifying centromere position; useful in plants and insects |
| N-banding | Silver nitrate solution | Nucleolar organizer regions (NOR) | Identifying rRNA gene clusters; superior for plants |
Detailed Isoenzyme Analysis Protocol
The standard isoenzyme analysis protocol utilizes commercially available kits for consistent results [47]:
Figure 2: Isoenzyme analysis workflow from sample preparation to interpretation.
Cell Extract Preparation: Prepare cell extracts from the test cell line alongside standard and control reagents (typically murine L929 and human HeLa extracts) [47].
Agarose Gel Electrophoresis: Load extracts onto an agarose gel and perform electrophoresis. This separates enzyme isoforms based on their charge and size, creating distinct banding patterns [47].
Enzyme-Specific Incubation: Incubate gels with specific substrates and color development reagents for intracellular enzymes including nucleoside phosphorylase (NP), lactate dehydrogenase (LD), glucose-6-phosphate dehydrogenase (G6PD), malate dehydrogenase (MD), peptidase B (PepB), aspartate amino transferase (AST), and mannose 6-phosphate isomerase (MPI) [47].
Band Pattern Analysis: Monitor color development and stop the reaction at the appropriate time to prevent over-development, which can obscure band resolution. Measure migration distances and compare them to standardized charts for species assignment [47].
Application in Detecting Cross-Contamination
Sensitivity and Detection Capabilities
Each technique offers different strengths in detecting cross-contamination, with varying levels of sensitivity and appropriate applications:
Table 3: Sensitivity Comparison for Cross-Contamination Detection
| Technique | Detection Sensitivity | Primary Contamination Type | Key Advantages |
|---|---|---|---|
| Karyotyping | As low as 1% (experienced cytogeneticist) [43] | Intraspecies | Provides highest versatility in characterization; detects aneuploidy, translocations |
| Isoenzyme Analysis | 10% of total cell population [46] [47] | Interspecies | Technically simple, robust, rapid, and inexpensive |
| STR Profiling | 5-30% depending on technique [43] | Intraspecies | Establishes identity to individual donor level; global standardization |
Strategic Implementation for Cell Line Authentication
For comprehensive cell line authentication, a strategic combination of techniques is recommended:
Isoenzyme Analysis for Routine Speciation: For rapid, cost-effective confirmation of species origin and detection of interspecies contamination during routine culture maintenance and at cell bank levels (master, working, end-of-production) [47].
Karyotyping for Intraspecies Contamination: When working with multiple human cell lines or when chromosomal abnormalities are suspected, karyotyping provides the sensitive detection needed for intraspecies contamination [43].
Enzyme Selection for Specific Contaminants: When using isoenzyme analysis, select enzymes based on potential contaminating species. For example, peptidase B (PepB) optimally differentiates Chinese hamster and mouse cells, while aspartate amino transferase (AST) is particularly useful for detecting human and cercopithecus monkey cell mixtures [47].
Table 4: Enzyme Selection for Detecting Specific Interspecies Contaminations
| Potential Cell Mixture | Most Diagnostic Enzymes | Visual Gel Pattern Indication |
|---|---|---|
| Chinese Hamster & Mouse | Peptidase B (PepB) | Distinct species-specific bands for PepB only |
| Human & Cercopithecus Monkey | Aspartate Amino Transferase (AST), Malate Dehydrogenase (MD) | Additional AST band; MD mitochondrial doublet |
| Chinese Hamster & Human | Lactate Dehydrogenase (LD) | Distinct LD bands for each species (≥11% each) |
The Scientist's Toolkit: Essential Research Reagents
Successful implementation of these classical techniques requires specific, high-quality reagents and materials:
Table 5: Essential Research Reagents for Karyotyping and Isoenzyme Analysis
| Reagent/Material | Technical Function | Application Context |
|---|---|---|
| Colchicine | Arrests cell division in metaphase by disrupting microtubule formation | Karyotyping: Essential for obtaining metaphase chromosomes for analysis |
| Giemsa Stain | DNA stain containing methylene blue, eosin, and azure; binds sulfur-rich regions | G-banding: Creates characteristic light/dark banding patterns for chromosome identification |
| Quinacrine Mustard | Fluorescent alkylating agent that binds AT-rich DNA regions | Q-banding: Produces fluorescent banding patterns; useful for heteromorphism studies |
| AuthentiKit System | Commercial kit providing substrates and reagents for multiple enzymes | Isoenzyme Analysis: Standardized system for reliable species identification via electrophoresis |
| Agarose Gels | Porous matrix for electrophoretic separation of biomolecules by charge/size | Isoenzyme Analysis: Medium for separating enzyme isoforms from different species |
| Carnoy's Solution (3:1 Methanol:Acetic Acid) | Fixative that preserves chromosomal structure while removing water | Karyotyping: Critical step after hypotonic treatment before slide preparation |
In the critical context of cell line cross-contamination, classical techniques like karyotyping and isoenzyme analysis remain essential components of proper cell authentication. While each method has distinct strengths—with karyotyping offering sensitive detection of intraspecies contamination and chromosomal abnormalities, and isoenzyme analysis providing rapid, cost-effective interspecies detection—they are most powerful when implemented as part of a comprehensive quality control strategy. For researchers and drug development professionals, incorporating these techniques at key points such as cell banking, after culture recovery from storage, and before initiating critical experiments provides a robust defense against the costly consequences of cell line misidentification. Following standardized protocols and understanding the specific applications and limitations of each technique ensures the reliability of cell-based research, ultimately contributing to reproducible science and valid therapeutic development.
DNA Fingerprinting and Barcode Assays for Precise Identification
Cross-contamination in cell line research represents one of the most persistent and damaging problems in biomedical science. When cell lines become contaminated with microorganisms or misidentified through mixing with other cell lines, the consequences reverberate throughout the entire research ecosystem, leading to unreliable data, irreproducible findings, and wasted resources. Studies have documented that between 18-36% of cell lines used in research are misidentified or contaminated [48] [49]. The scientific community has responded by developing sophisticated molecular techniques for cell line authentication, primarily through DNA fingerprinting using Short Tandem Repeat (STR) profiling and DNA barcoding for species identification. These methods provide essential tools for verifying cell line identity and ensuring research integrity in drug development and basic biological research.
The problem of cell line contamination is not new. The first human cell line, HeLa, was established in 1951, and by 1956, mycoplasma contamination had already been detected in it [48]. In recent years, new techniques have been developed for identifying contaminated and misidentified lines by DNA microsatellite fingerprinting, providing the scientific community with cost-effective, efficient, and highly reproducible assays [48]. As a result, many leading journals and funding agencies now require authentication data as a prerequisite for publication or grant approval [41] [49].
Technical Foundations: Core Methodologies for Cell Identification
DNA Fingerprinting via Short Tandem Repeat (STR) Profiling
STR profiling constitutes the gold standard for human cell line authentication. This technique targets specific locations in the genome where short sequences of DNA (typically 2-7 base pairs) are repeated in tandem [50]. The number of repeats at each locus varies significantly between individuals, creating a unique genetic fingerprint that can distinguish cell lines [48].
The fundamental workflow involves several key steps. First, genomic DNA is extracted from cell samples using commercial kits such as the QIAGEN Blood & Cell Culture DNA Maxi Kit [48]. Next, multiplex PCR simultaneously amplifies multiple STR loci using commercially available kits that typically include the 13 CODIS (Combined DNA Index System) loci plus amelogenin for gender determination [48]. The resulting PCR products are then separated by capillary electrophoresis, which precisely sizes the DNA fragments [49]. Finally, specialized software like GeneMapper analyzes the data to determine allele sizes and generate a unique STR profile for the cell line [48] [49].
The international standard for human cell line authentication (ANSI/ATCC ASN-0002-2022) recommends testing a core set of 13 STR loci plus amelogenin [49]. However, expanded kits analyzing 21-24 loci provide superior discrimination power by lowering the Probability of Identity (POI), making it significantly less likely for different cell lines to share the same STR profile [49].
Table 1: Core STR Loci in Commercial Authentication Kits
| STR Locus | 13-Core Loci (ANSI/ATCC) | 14-Loci Kits | 24-Loci Kits |
|---|---|---|---|
| D8S1179 | ● | ● | ⬤ |
| D21S11 | ● | ● | ⬤ |
| D7S820 | ● | ● | ⬤ |
| CSF1PO | ● | ● | ⬤ |
| D3S1358 | ● | ● | ⬤ |
| TH01 | ● | ● | ⬤ |
| D13S317 | ● | ● | ⬤ |
| D16S539 | ● | ● | ⬤ |
| vWA | ● | ● | ⬤ |
| TPOX | ● | ● | ⬤ |
| D18S51 | ● | ● | ⬤ |
| D5S818 | ● | ● | ⬤ |
| FGA | ● | ● | ⬤ |
| Amelogenin | ● | ● | ⬤ |
| D2S1338 | ● | ⬤ | |
| D19S433 | ● | ⬤ | |
| SE33 | ⬤ | ||
| DYS391 | ⬤ | ||
| Yindel | ⬤ | ||
| D10S1248 | ⬤ | ||
| D1S1656 | ⬤ | ||
| D22S1045 | ⬤ | ||
| D2S441 | ⬤ | ||
| D12S391 | ⬤ |
STR profiling has proven highly effective in identifying cases of cross-contamination. For example, analysis of the NCI-60 cell line panel revealed that several lines had common origins, including the melanoma lines MDA-MB-435, MDA-N, and M14; the central nervous system lines U251 and SNB-19; and the ovarian lines OVCAR-8 and OVCAR-8/ADR [48]. The technique is sufficiently sensitive to detect contamination levels of 5-10% when using standard protocols [51].
Figure 1: STR Profiling Workflow for Cell Line Authentication
DNA Barcoding for Species Identification
DNA barcoding provides a complementary approach for species identification that is particularly valuable for non-human cell lines and detecting interspecies contamination. This method identifies species by analyzing a short, standardized gene region that shows sufficient sequence variation to distinguish between species [52]. For animal cells, the most common barcode is the cytochrome c oxidase subunit 1 (CO1) gene, a mitochondrial gene expressed in all animal species [53]. The CO1 gene is ideal for species identification due to its relatively easy amplification, the presence of only one variant per individual, and a high degree of evolutionary divergence among species-specific homologs [53].
The standard DNA barcoding workflow begins with tissue sampling from the organism or cell line, followed by DNA extraction [54]. The target barcode region (e.g., CO1 for animals, ITS for fungi, or matK/rbcL for plants) is amplified using PCR with species-specific primers [52]. The amplified PCR product is then sequenced, typically using Sanger sequencing, and the resulting sequence is compared against reference databases like the National Center for Biotechnology Information (NCBI) using the Basic Local Alignment Search Tool (BLAST) to identify the species [52].
The U.S. Food and Drug Administration (FDA) has developed a validated protocol for DNA barcoding of fish species, highlighting its importance in regulatory science [54]. The ATCC CO1 assay can distinguish cell lines from 14 different species, including human, cat, Chinese hamster, Rhesus monkey, mouse, rat, and others [53]. This capability makes it invaluable for detecting interspecies contamination, which remains a common problem in cell culture facilities.
Figure 2: DNA Barcoding Workflow for Species Identification
Advanced Applications and Emerging Technologies
Next-Generation Sequencing Approaches
Next-generation sequencing (NGS) technologies are revolutionizing cell line authentication by providing unprecedented sensitivity and comprehensive analysis capabilities. Deep NGS-based methods can achieve detection sensitivity of ≤1% for contaminants, significantly outperforming conventional STR (5-10% sensitivity) and SNP (3-5% sensitivity) assays [51]. These methods can simultaneously authenticate hundreds of samples in a single run through barcoding technology, making them highly efficient for large biobanks [51].
NGS-based authentication provides multiple functionalities in a single assay. It can authenticate human and mouse cell lines, xenografts, and organoids; identify and quantify contamination in human cell line samples; detect species-specific components in human-mouse mixed samples with 0.1% sensitivity; screen for mycoplasma contamination; and infer population structure and gender of human samples [51]. This multifunctional capability addresses several quality control challenges simultaneously, making it particularly valuable for comprehensive biobank management.
Multiplex Contamination Detection
For comprehensive contamination screening, multiplex PCR approaches have been developed that can simultaneously detect multiple potential contaminants in a single reaction. The Multiplex Cell Contamination Test (McCT) can detect 37 different contamination markers, including various Mycoplasma species, viruses such as squirrel monkey retrovirus (SMRV), and interspecies contamination [55]. This high-throughput approach can analyze more than 1000 cell lysates per week, providing a powerful tool for maintaining cell line purity in large research facilities [55].
The McCT assay is based on multiplex PCR with target-specific primers, followed by hybridization of amplimers to specific oligonucleotide probes. This approach has proven to be highly specific, sensitive, and robust, allowing researchers to assess cell line purity comprehensively rather than testing for single contaminants individually [55].
Experimental Protocols and Best Practices
STR Profiling Protocol for Cell Line Authentication
The following detailed protocol is adapted from established methods used for authenticating the NCI-60 cell line panel [48] and commercial providers [49]:
Cell Culture and DNA Extraction: Culture cells under standard conditions until 60-80% confluent. Harvest cells during logarithmic growth and extract genomic DNA using commercial kits (e.g., Qiagen Blood & Cell Culture DNA Maxi Kit). Quantify DNA using spectrophotometry and verify quality (OD260/280 ratio of ~1.8) [48].
Multiplex PCR Amplification: Perform PCR amplification using commercial STR kits (e.g., AmpFℓSTR Identifiler, GlobalFiler). Typical reaction conditions include: 15-minute enzyme activation at 95°C, followed by 40 cycles of denaturation at 94°C for 30 seconds, annealing at 61°C for 90 seconds, and extension at 72°C for 60 seconds, with a final extension at 72°C for 10 minutes [48] [55].
Capillary Electrophoresis: Separate PCR products using capillary electrophoresis systems (e.g., ABI 3730xl DNA Analyzer). Include appropriate size standards for accurate fragment sizing [49].
Data Analysis: Analyze results using specialized software (e.g., GeneMapper). Compare allele calls to reference databases. Calculate percent similarity between samples by dividing the number of identical alleles by the total number of surveyed alleles then multiplying by 100 [48].
Interpretation: Use 80% similarity as a cutoff for declaring samples as matching. Consider a more relaxed definition that allows for a difference of one STR at one site to account for minor genetic drift in cultured cells [48].
DNA Barcoding Protocol for Species Identification
The FDA-approved protocol for DNA barcoding of fish species provides a validated framework that can be adapted for cell line authentication [54]:
Tissue Sampling and DNA Extraction: Obtain tissue samples (musculature preferred) using sterile techniques to prevent cross-contamination. Extract DNA using commercial kits (e.g., DNeasy Blood & Tissue Kit). Verify DNA concentration (≥5 ng/μL) and purity (260/280 nm ratio of ~1.8) [54].
PCR Amplification of Barcode Region: Amplify the target barcode region using species-specific primers. For animal cells, amplify the CO1 gene using primers such as FishF1 (5'-TCAACCAACCACAAAGACATTGGCAC-3') and FishR1 (5'-TAGACTTCTGGGTGGCCAAAGAATCA-3') [54]. PCR conditions typically include an initial denaturation at 94°C for 2 minutes, followed by 35 cycles of 94°C for 30 seconds, 52°C for 30 seconds, and 72°C for 1 minute, with a final extension at 72°C for 10 minutes [54].
PCR Product Cleanup and Sequencing: Purify PCR products to remove excess primers and nucleotides. Perform cycle sequencing reactions using BigDye Terminator chemistry. Purify sequencing reactions to remove unincorporated dye terminators [54].
Sequence Analysis and Species Identification: Analyze sequence chromatograms for quality. Compare the resulting barcode sequence to reference databases using BLAST or specialized barcoding databases. Species identification is confirmed when the query sequence shows high similarity (typically >98%) to a reference sequence of known origin [52] [54].
Table 2: Comparison of Authentication Methods
| Parameter | STR Profiling | DNA Barcoding | NGS-Based |
|---|---|---|---|
| Primary Application | Human cell line authentication | Species identification | Comprehensive authentication |
| Sensitivity | 5-10% contamination | Varies by method | ≤1% contamination |
| Throughput | Medium | Low | High (100-200 samples/run) |
| Cost | Low to moderate | Low | Moderate to high |
| Multiplexing Capability | 16-24 loci simultaneously | Typically single-plex | 630+ amplicons |
| Standardization | ANSI/ATCC ASN-0002 | FDA protocols for fish | Emerging standards |
| Database Support | Extensive (CLS, ATCC) | BOLD, GenBank | Custom databases |
Table 3: Essential Research Reagents for Cell Line Authentication
| Reagent/Kit | Application | Key Features | Provider Examples |
|---|---|---|---|
| GlobalFiler STR Kit | Human cell line authentication | 24 STR loci, 3 sex markers | Thermo Fisher [49] |
| Identifiler Plus Kit | Human cell line authentication | 16 STR loci | Thermo Fisher [50] |
| DNeasy Blood & Tissue Kit | DNA extraction | High-quality DNA from cells | Qiagen [48] [51] |
| CO1 Barcoding Primers | Species identification | Species-specific amplification | ATCC [53] |
| VenorGeM Mycoplasma Kit | Mycoplasma detection | Multiplex Mycoplasma detection | Minerva Biolabs [55] |
| AmpF STR Identifiler PCR Kit | STR profiling | 15 tetranucleotide repeat loci + amelogenin | Applied Biosystems [48] |
Quality Assurance and Authentication Guidelines
Implementing rigorous cell line authentication protocols requires adherence to established best practices and quality assurance guidelines. The International Cell Line Authentication Committee (ICLAC) provides essential resources and maintains a register of misidentified cell lines to help researchers avoid problematic lines [41] [50]. Leading journals including those published by the American Association for Cancer Research (AACR) and Nature Publishing Group now require cell line authentication for publication [49].
Key recommendations for maintaining cell line integrity include:
Authenticate upon receipt: Quarantine and authenticate all new cell lines before use, comparing STR profiles to reference databases [50].
Regular monitoring: Re-authenticate cell lines every 10 passages or approximately every 3 months, whichever comes first [49] [50].
Maintain records: Keep detailed documentation of authentication results, passage numbers, and morphological observations [50].
Use validated methods: Employ commercial STR kits rather than "homebrew" methods to ensure reliability and reproducibility [50].
Comprehensive testing: Implement mycoplasma testing regularly and conduct species verification when working with multiple species [41] [50].
The development of advanced technologies like deep NGS-based authentication represents the future of cell line quality control, offering unprecedented sensitivity and comprehensive analysis capabilities [51]. As these methods become more accessible and cost-effective, they will further strengthen the foundation of reproducible biomedical research.
By implementing robust DNA fingerprinting and barcode assays according to these established protocols and guidelines, researchers and drug development professionals can significantly reduce the risk of cross-contamination, ensure the validity of their experimental results, and maintain the integrity of the scientific record.
Cross-contamination in cell line research represents a fundamental threat to scientific integrity, potentially invalidating experimental data and compromising therapeutic development. Within this context, morphological verification serves as the first and most immediate line of defense. This technical guide details how trained researchers can identify contaminants through visual cues, a crucial skill set given that studies estimate up to 20% of published papers could be invalid due to misidentified or cross-contaminated cell lines [56]. While microbial contamination like bacteria and fungi often manifest obvious signs, cross-contamination with other cell lines presents a more insidious challenge, where highly proliferative lines like HeLa can overgrow slower-growing populations, fundamentally altering study outcomes [4] [1]. The International Cell Line Authentication Committee (ICLAC) registry lists 593 misidentified or cross-contaminated lines [4], making morphological monitoring an essential, accessible tool for maintaining research validity alongside molecular authentication methods.
Morphological Characteristics of Common Contaminants
Routine microscopic examination allows for early detection of biological contaminants. The table below summarizes key visual indicators across major contaminant types.
Table 1: Visual Identification of Common Cell Culture Contaminants
| Contaminant Type | Macroscopic Culture Appearance | Microscopic Morphology | pH Change |
|---|---|---|---|
| Bacteria | Cloudy, turbid medium; possibly thin surface film [57] [58] | Tiny, moving granules between cells; shapes (rods, spheres) resolvable under high power [57] | Sudden drop; medium often turns yellow with phenol red [57] [58] |
| Yeast | Turbid medium, especially in advanced stages [57] | Individual ovoid or spherical particles; may show budding of smaller particles [57] | Stable initially, then increases with heavy contamination [57] |
| Mold | Turbid medium; possible visible mycelial clumps [1] | Thin, wispy filaments (hyphae); denser clumps of spores [57] | Stable initially, then rapidly increases with heavy contamination [57] |
| Mycoplasma | No change in turbidity [1] | No definitive visual signs; may cause subtle changes in cell growth and morphology [1] [58] | None detectable by eye [58] |
| Cross-Cell Line Contamination | No change in turbidity [4] | Overgrowth by a morphologically distinct cell type; loss of expected characteristics [4] [1] | None directly associated |
Bacterial and Fungal Contaminants
Bacterial contamination typically manifests rapidly, often within a few days [57]. Under low-power microscopy, bacteria appear as tiny, shimmering granules between cultured cells. With higher magnification, individual bacterial shapes (e.g., rod-shaped E. coli) become distinguishable [57]. The culture medium often becomes cloudy and acidic, turning yellow in the presence of phenol red [58]. Fungal contaminants, including molds and yeasts, present differently. Yeast cells are unicellular, ovoid particles that may be observed budding off smaller particles, while mold contamination appears as multicellular, wispy filaments (hyphae) that can develop into denser mycelial networks [57].
Mycoplasma and Viral Contaminants
Mycoplasma contamination is particularly problematic as it is impossible to detect using standard light microscopy alone [1]. It does not cause turbidity or other obvious signs, but can alter cellular function, leading to misleading experimental results [1] [58]. Similarly, viral contamination rarely causes visible changes in culture conditions, making detection reliant on specialized techniques like electron microscopy, PCR, or immunoassays [57] [58]. The inability to visually identify these contaminants underscores the necessity for regular, rigorous biochemical testing.
Cross-Contamination by Other Cell Lines
Cross-contamination occurs when an unintended cell line infiltrates a culture, leading to misidentification. Fast-growing cell lines, such as HeLa (cervical adenocarcinoma) or HEK293, can overgrow slower-growing populations [4] [1]. For example, the ICLAC registry lists several cell lines, including L-02 (claimed as human normal liver) and WRL 68 (claimed as human embryonic liver), that are actually cross-contaminated with HeLa cells [4]. Morphologically, this may appear as an overgrowth by a morphologically distinct cell type and a gradual loss of the expected cellular characteristics for the original culture [4]. This type of contamination necessitates authentication through methods like STR profiling rather than visual identification alone [59] [56].
Experimental Protocols for Morphological Verification
Daily Microscopic Examination Workflow
A standardized protocol for routine morphological assessment is critical for early contaminant detection.
Table 2: Essential Research Reagent Solutions for Morphological Verification
| Reagent/Equipment | Function in Verification Protocol |
|---|---|
| Phase Contrast Microscope | Enables observation of live, unstained cells and fine cellular details. |
| Hemocytometer | Allows for cell counting and assessment of concentration and viability. |
| Phenol Red Medium | Acts as a pH indicator; color changes (yellow/acidic, pink/alkaline) signal microbial metabolism. |
| Mycoplasma Detection Kit (e.g., PCR, Luminescence) | Essential for detecting occult mycoplasma contamination, which is invisible by light microscopy. |
| Gram Stain Kit | Used for differentiating between major groups of bacteria (Gram-positive vs. Gram-negative). |
Procedure:
- Pre-examination: Prior to removing cultures from the incubator, visually inspect the flask or dish against a neutral background. Look for macroscopic signs like turbidity or unexpected color changes in the medium [57] [58].
- Microscopic Observation:
- Use a phase-contrast microscope for optimal visualization of live cells.
- Begin with a low-power objective (e.g., 10x) to scan the entire culture area. Look for signs of contamination like tiny, moving granules (bacteria) or filamentous structures (mold) [57].
- Switch to a higher-power objective (e.g., 40x) to resolve finer details. Examine cell morphology, including size, shape, and granularity. Compare these observations to the established morphological profile for the cell line.
- Pay close attention to the spaces between cells, as this is where microbial contaminants are often most visible [57].
- Documentation: Record observations, including cell density, confluence, morphology, and any potential anomalies. Note the color of the culture medium.
Contamination Identification and Response Protocol
Upon identifying potential contamination, a systematic response is required.
Procedure:
- Quarantine: Immediately move the contaminated culture to a separate, designated incubator to prevent spread [1] [58].
- Identification: Use additional methods to confirm the contaminant:
- For suspected bacteria/fungi: Perform Gram staining or culture on microbiological media [58].
- For general unknown microbes: Use qPCR or 16S rRNA sequencing [1].
- For suspected mycoplasma: Use a dedicated mycoplasma detection assay (e.g., PCR, luminescence) [1] [56].
- For suspected cross-contamination: Perform cell line authentication via STR profiling [59] [56].
- Decontamination:
- In Research Labs: Typically, contaminated cultures are disposed of following biosafety guidelines. All associated lab surfaces, incubators, and equipment must be decontaminated [1].
- Antibiotic Treatment: If a culture is irreplaceable, treatment with high concentrations of specific antibiotics (e.g., Penicillin-Streptomycin for bacteria, Amphotericin B for fungi) may be attempted. This requires a dose-response test to determine toxicity and subsequent culture in antibiotic-free medium to confirm decontamination [57] [58]. It is critical to note that antibiotics should not be used routinely, as they can mask low-level contamination [57].
- Prevention Review: Reevaluate aseptic techniques, train personnel, and verify that stock cell lines and reagents are not contaminated before restarting work [1].
Integrating Morphological Verification into a Comprehensive Quality Control Framework
While morphological verification is indispensable, it is not infallible. It must be integrated into a broader quality control framework to fully address the problem of cross-contamination. This integrated approach is summarized in the following workflow.
This holistic strategy includes:
- Routine Authentication: Employ Short Tandem Repeat (STR) profiling to confirm cell line identity, a method now required by many high-impact journals [59] [56].
- Regular Microbial Testing: Implement frequent testing for mycoplasma and other microbes using PCR, luminescence, or other assays [1] [56].
- Aseptic Technique: Maintain strict handling procedures, use sterile single-use consumables, and control access to cell culture areas [1].
- Cell Banking: Create authenticated master cell banks and replace working cultures regularly from frozen stock to limit phenotypic drift and cross-contamination [59].
Morphological verification remains a cornerstone technique for recognizing cell culture contaminants by eye. Its integration with molecular methods and rigorous laboratory practices forms an essential defense, safeguarding the validity and reproducibility of biomedical research and drug development.
Cell line cross-contamination represents a fundamental challenge in biomedical research, compromising experimental validity and contributing to the reproducibility crisis. The problem originates from the aggressive overgrowth of fast-replicating cell lines—notably HeLa—over slower-growing cultures, which can occur undetected without proper authentication protocols [60] [61]. This issue is not trivial; studies indicate that approximately 8.6% of cell lines reported in scientific literature appear on problematic lists, affecting an estimated 16.1% of published papers [60]. The scientific community has responded by establishing specialized databases and resources to authenticate cell lines, with ICLAC, Cellosaurus, and ATCC representing the cornerstone of these efforts. This technical guide provides researchers, scientists, and drug development professionals with comprehensive methodologies for integrating these critical resources throughout the research lifecycle to ensure cell line integrity.
Understanding the Landscape of Problematic Cell Lines
The Scope and Impact of Cell Line Misidentification
Cross-contamination and misidentification of cell lines generate profound scientific and economic consequences:
Prevalence: The International Cell Line Authentication Committee (ICLAC) Register of Misidentified Cell Lines currently documents 593 cell lines known to be cross-contaminated or otherwise misidentified [29]. Among these, 545 cell lines have no known authentic stock, while 48 cell lines initially thought misidentified now have authenticated stocks available [29].
Common Contaminants: HeLa cells represent the most prevalent contaminant, appearing in 145 entries on the ICLAC register. Other frequent contaminants include T-24 (21 entries) and M14 (18 entries) [29].
Publication Impact: Analysis of approximately two million papers revealed that 8.6% of reported cell lines were problematic, with these appearing in 16.1% of publications [60]. Alarmingly, the use of contaminated nasopharyngeal carcinoma cell lines continues in hundreds of papers even after contamination has been officially documented [61].
Economic Consequences: The use of misidentified cell lines generates invalid data, wasting research resources and compromising evidence-based conclusions. One analysis identified nearly 6,000 publications using just five common misidentified liver cell lines [4].
Table 1: Categories of Misidentified Cell Lines in the ICLAC Register (Version 13, April 2024)
| Category | Number of Cell Lines | Description |
|---|---|---|
| Total Misidentified Cell Lines | 593 | All known problematic lines |
| No Known Authentic Stock | 545 | Contaminated with no authentic reference |
| Authentic Stock Available | 48 | Initially misidentified but authentic stock found |
| Unknown Contaminant | 78 | Donor doesn't match original but contaminant unknown |
| Interspecies Contamination | 70 | Contamination from different species |
| Non-Human Intraspecies | 9 | Contamination within non-human species |
Case Study: The NCI-H157 Example
The NCI-H157 cell line exemplifies typical authentication challenges. According to Cellosaurus, this line is registered as problematic because it has been shown to be identical to NCI-H1264 [62]. Designated as a lung squamous cell carcinoma from a 59-year-old male, it carries multiple significant mutations including in KRAS (p.Gly12Arg) and TP53 (p.Leu35Phefs*8 and p.Glu298Ter) [62]. This case demonstrates how even well-characterized lines can have identity issues that compromise their experimental utility.
The Authentication Database Ecosystem
ICLAC: The Authority on Misidentified Cell Lines
The International Cell Line Authentication Committee (ICLAC) provides the definitive international standard for identifying problematic cell lines:
Primary Resource: The ICLAC Register of Misidentified Cell Lines serves as the authoritative list of cross-contaminated or misidentified cell lines [29]. Updated regularly (currently version 13, released April 2024), this register is licensed under Creative Commons for non-commercial use [29].
Educational Mission: Beyond maintaining the register, ICLAC provides educational resources on cell line authentication, including testing guidance, policy frameworks for institutions, and information on good cell culture practice [63].
Composition Data: The register documents that 157 different contaminants are represented, with 78 cell lines having unknown contaminants despite not matching their original donor [29].
Cellosaurus: The Comprehensive Cell Line Knowledgebase
Cellosaurus represents a expansive knowledge resource that attempts to describe all cell lines used in biomedical research:
Scope: Contains information on approximately 120,000 cell lines with extensive characterization data [32].
Authentication Integration: Provides STR profiles for approximately 7,000 cell lines and incorporates CLASTR, a specialized STR similarity search tool [32].
Rich Annotation: For each cell line, Cellosaurus provides origins, disease associations, molecular data (genomic, transcriptomic, proteomic), mutations, and bibliographic references [62] [64].
RRID Assignment: Cellosaurus issues Research Resource Identifiers (RRIDs), unique identifiers that facilitate proper citation and tracking of cell lines in publications [60].
ATCC: The Gold Standard for Authenticated Materials
The American Type Culture Collection (ATCC) provides both biological materials and associated authenticated data:
Quality Standards: ATCC maintains rigorous authentication protocols including STR profiling, karyotyping, and mycoplasma testing [65].
ATCC Cell Line Land: This innovative resource combines fully authenticated cell lines with curated transcriptomic and genomic datasets, creating reference standards for precision therapeutics [65].
Educational Resources: Offers webinars, workshops, and online courses to enhance researcher understanding of cell line authentication and quality control [65].
Table 2: Core Database Resources for Cell Line Authentication
| Resource | Primary Function | Key Features | Authentication Method |
|---|---|---|---|
| ICLAC Register | Listing misidentified lines | 593 problematic lines; Educational resources | Reference list for comparison |
| Cellosaurus | Comprehensive cell line knowledgebase | 120,000+ cell lines; STR profiles; CLASTR tool | STR similarity searching |
| ATCC | Biological materials & data | Authenticated cell banks; STR databases; Omics data | Gold-standard STR profiling |
| CLASTR | STR similarity search | Compares query profiles to Cellosaurus database | Algorithmic matching (Tanabe/Masters) |
| AuthentiCell | STR profile search | ECACC service; Extensive human STR profile database | STR comparison |
| DSMZ Database | STR profile repository | Collaborative bank database (ATCC, JCRB, RIKEN) | STR analysis |
Experimental Protocols for Cell Line Authentication
STR Profiling: The Gold Standard Methodology
Short Tandem Repeat (STR) profiling represents the internationally recognized gold standard for human cell line authentication. The methodology involves:
Sample Preparation and DNA Extraction
- Culture cells under standard conditions for 3-5 passages to ensure logarithmic growth [39]
- Extract genomic DNA from 5 × 10^6 cells using commercial kits (e.g., QIAamp DNA Blood Mini Kit) [39]
- Quantify DNA using fluorometric methods (e.g., Qubit fluorometer) to ensure adequate quality and concentration [39]
STR PCR Amplification
- Utilize multiplex PCR systems containing core STR markers. The ATCC standard recommends 8 core loci (TH01, TPOX, vWA, CSF1PO, D16S539, D7S820, D13S317, D5S818) plus Amelogenin for gender identification [61]
- Forensic-grade approaches expand to 21 autosomal STRs plus sex markers for enhanced discrimination power [39]
- Perform PCR amplification according to manufacturer protocols with appropriate controls
Capillary Electrophoresis and Analysis
- Separate amplified fragments using capillary electrophoresis (e.g., Classic 116 Genetic Analyzer) [39]
- Analyze results with specialized software (e.g., GeneManager) to generate allele calls [39]
- Compare obtained profiles with reference databases using standardized algorithms
Algorithmic Matching for STR Profiles
Two primary algorithms govern STR profile comparison:
Tanabe Algorithm
- Related: ≥90% similarity
- Ambiguous: 80-90% similarity
- Unrelated: <80% similarity [39]
Masters Algorithm
- Related: ≥80% similarity
- Ambiguous: 60-80% similarity
- Unrelated: <60% similarity [39]
The Tanabe algorithm's stricter criteria (≥90% for relatedness) makes it more conservative for authentication purposes.
Implementing a Comprehensive Authentication Strategy
Effective cell line authentication requires a systematic approach:
Primary Authentication (STR Profiling)
- Test upon receipt of new cell lines
- Conduct authentication every 3 months for actively cultured lines
- Perform authentication before preserving stocks and after thawing
- Use at least the 8 core STR markers recommended by ATCC standards [61]
Secondary Characterization Methods
- Isoenzyme Analysis: Species verification through electrophoretic mobility patterns of intracellular enzymes [61]
- HLA Typing: Human Leukocyte Antigen profiling using serological methods or molecular typing for intraspecies discrimination [61]
- Whole Genome/Exome Sequencing: Comprehensive genomic characterization to identify mutations and confirm tissue origin [62] [65]
Documentation and Tracking
- Maintain detailed records of authentication results, passage numbers, and storage conditions
- Implement a cell line management system that tracks testing schedules and results
- Include RRIDs in all publications to precisely identify biological resources [60]
Integrated Database Utilization in Research Workflows
Pre-Experimental Planning Phase
Before initiating experiments, researchers should consult authentication databases:
Cell Line Selection
- Query the ICLAC register to verify prospective cell lines are not listed as misidentified [29]
- Check Cellosaurus for comprehensive characterization data and potential issues [62]
- Source cell lines from authenticated repositories like ATCC when possible [65]
Experimental Design
- Review existing omics data in Cellosaurus and ATCC Cell Line Land to inform baseline expectations [62] [65]
- Identify appropriate authentication methods based on cell line history and characterization needs
- Plan authentication timepoints throughout the experimental timeline
Active Research Phase
During experimentation, maintain authentication vigilance:
Regular Monitoring
- Implement STR profiling at predetermined intervals using standardized protocols [39]
- Compare results with database references using CLASTR or similar tools [32]
- Document any profile changes that may indicate genetic drift or contamination
Contingency Response
- If authentication fails, immediately quarantine affected cultures
- Consult databases to identify potential contaminants based on STR profile matching
- Source replacement materials from authenticated banks when available
Publication and Documentation Phase
When disseminating research results:
Resource Identification
- Include RRIDs for all cell lines used, facilitating proper attribution and database linking [60]
- Detail authentication methods, timepoints, and results in methods sections
- Provide STR profiles in supplementary materials when possible
Database Contribution
- Report novel cell lines to appropriate databases
- Contribute STR profiles and characterization data to enhance community resources
- Update database entries with new information from your research
Table 3: Research Reagent Solutions for Cell Line Authentication
| Reagent/Resource | Function | Application Context |
|---|---|---|
| STR Profiling Kits (e.g., SiFaSTR 23-plex) | Amplification of STR loci | Human cell line authentication; 21 autosomal STRs + sex markers [39] |
| DNA Extraction Kits (e.g., QIAamp DNA Blood Mini) | High-quality DNA isolation | Sample preparation for STR analysis and other molecular authentication [39] |
| Fluorometric Quantification (e.g., Qubit) | Accurate DNA quantification | Quality control pre-STR analysis [39] |
| CLASTR Tool | STR profile similarity search | Comparing experimental STR profiles against Cellosaurus database [32] |
| ICLAC Register | Misidentified cell line reference | Pre-screening cell lines for known contamination issues [29] |
| ATCC Cell Line Land | Authenticated omics reference data | Comparative analysis of transcriptomic and genomic profiles [65] |
Emerging Trends and Future Directions
Cell line authentication continues to evolve with technological advancements:
Forensic-Grade STR Panels: Expansion beyond standard 8-marker panels to forensic-grade 21+ STR loci for enhanced discrimination power, particularly valuable for biobanks and long-term studies [39]
Integrated Omics Authentication: Combining STR profiling with genomic, transcriptomic, and proteomic characterization for multidimensional validation [65]
Automated Authentication Platforms: Development of tools like SciScore that automatically scan methods sections for problematic cell lines during manuscript review [60]
Blockchain for Provenance Tracking: Emerging approaches to create immutable records of cell line lineage, passage history, and authentication results
International Standardization: Growing consensus on authentication requirements among journals, funders, and regulatory agencies, mandating database consultation and regular testing
The integrated use of ICLAC, Cellosaurus, and ATCC databases provides a robust framework for addressing the persistent challenge of cell line cross-contamination. By implementing systematic authentication protocols that leverage these resources throughout the research lifecycle, scientists can significantly enhance experimental reproducibility and reliability. The scientific community must prioritize cell line authentication as a fundamental practice rather than an optional verification step. As technological advancements continue to improve authentication methods, researchers have an expanding toolkit to ensure the integrity of their cellular models, ultimately strengthening the foundation of biomedical research and drug development.
Developing a Standard Operating Procedure (SOP) for Authentication
Purpose and Scope
This Standard Operating Procedure (SOP) establishes the mandatory process for authenticating human cell lines used in research. Its purpose is to verify cell line identity and ensure the absence of cross-contamination, thereby safeguarding experimental integrity and data reproducibility. This procedure applies to all researchers and laboratory personnel who initiate, maintain, or use human cell lines for research experiments.
Cross-contamination in cell culture occurs when one cell line is inadvertently replaced by or mixed with another, more aggressive cell line. This is not a minor issue; studies have identified misidentified or cross-contaminated cell lines as a primary cause of irreproducible research, wasting billions of dollars annually and invalidating published findings [5] [21].
The most notorious example is the HeLa cell line, which has contaminated numerous cell lines worldwide [6] [21]. One investigation of 278 tumor cell lines from Chinese institutes found a 46.0% cross-contamination/misidentification rate, with 73.2% of cell lines established in Chinese laboratories being misidentified [21]. Furthermore, initial quality control screenings at the National Center for Advancing Translational Sciences (NCATS) identified a Mycoplasma contamination rate of over 10% [6]. These contaminants alter cell behavior, metabolism, and gene expression, leading to spurious and irreproducible data [66] [6]. The table below summarizes key quantitative findings on the prevalence and impact of this issue.
Table 1: Documented Prevalence and Impact of Cell Line Contamination
| Study Focus | Key Finding | Statistical Result | Source |
|---|---|---|---|
| Misidentification in China | Cross-contamination/misidentification rate in a panel of tumor cell lines | 128/278 cases (46.0%) | [21] |
| Chinese-origin Cell Lines | Misidentification rate for cell lines established within China | 52/71 cases (73.2%) | [21] |
| HeLa Contamination | Proportion of misidentified cases caused by HeLa cell contamination | 60/128 cases (46.9%) | [21] |
| Mycoplasma at NCATS | Initial Mycoplasma contamination rate upon cell line receipt | >10% | [6] |
| Literature Impact | Estimated proportion of published papers that may be invalid due to misidentified cells | Up to ~20% | [67] |
Definitions
- Authentication: The process of verifying a cell line's identity and confirming it is free from cross-contamination and microbial contaminants like Mycoplasma [66].
- Cross-Contamination: The accidental introduction of one cell line into another culture, leading to overgrowth and replacement of the original cell line [5] [21].
- Short Tandem Repeat (STR) Profiling: A DNA profiling method that analyzes highly polymorphic repetitive sequences to generate a unique genetic fingerprint for a human cell line [66] [67].
- Mycoplasma: A class of bacteria that lack a cell wall and are a common, covert contaminant in cell cultures, capable of altering cellular functions [66] [6].
Authentication Testing Methodology
A comprehensive authentication strategy combines multiple tests to assess cell line identity and purity.
Morphology and Growth Analysis
- Morphology Check: Frequently observe cells under a microscope. Document cellular shape (e.g., epithelial, fibroblast-like) and size with digital images. Be alert for sudden changes in appearance, which can indicate problems [66].
- Growth Curve Analysis: Establish a baseline growth curve by plating cells at a specific density and counting them at regular intervals. This determines the population doubling time and helps monitor culture consistency. Variable growth can be a sign of contamination or genetic drift [66].
Short Tandem Repeat (STR) Profiling
STR profiling is the gold standard for confirming human cell line identity. The process involves amplifying specific genomic loci via multiplex PCR and analyzing the fragment sizes via capillary electrophoresis to create a unique DNA profile [66] [67].
Table 2: Core STR Loci for Cell Line Authentication as per ANSI/ATCC ASN-0002 Revised 2022
| Locus Name | Locus Name | Locus Name | Locus Name |
|---|---|---|---|
| CSF1PO | D3S1358 | D5S818 | D7S820 |
| D8S1179 | D13S317 | D16S539 | D18S51 |
| D21S11 | FGA | TH01 | TPOX |
| vWA |
Experimental Protocol: STR Profiling
- DNA Extraction: Purify genomic DNA from a cell pellet following a standard phenol-chloroform or kit-based protocol. A starting amount of 2-5 ng of DNA is optimal for amplification [67].
- PCR Amplification: Perform a multiplex PCR reaction using a commercial STR kit (e.g., GenePrint 24 System) that contains primers for the core STR loci and the amelogenin gene for sex determination [67].
- Capillary Electrophoresis: Analyze the PCR amplicons using a capillary electrophoresis instrument (e.g., Spectrum Compact CE System). The instrument separates the DNA fragments by size and detects fluorescent labels [67].
- Profile Analysis: Software generates an electropherogram from which the allele calls (number of repeats) at each locus are determined [67].
Species Verification
- Isoenzyme Analysis: Verifies the species of origin by analyzing the electrophoretic mobility of enzymes like lactate dehydrogenase. The pattern of isoenzymes is characteristic of a particular species [66].
Mycoplasma Detection
- Fluorescent Staining: Use a DNA-binding fluorescent dye like Hoechst 33258. Stain the cells and examine under a fluorescence microscope at 500X magnification. Mycoplasma contamination appears as characteristic patterns of extracellular particulate or filamentous fluorescence on the cell surface or in spaces between cells [66].
- Biochemical Assays: Use commercially available kits that detect specific enzymatic activities of Mycoplasma. These assays are rapid and can be performed in about one hour [6].
Procedural Workflow
The following workflow outlines the key decision points and steps for effective cell line authentication.
Interpretation of Results and Acceptance Criteria
STR Profile Matching
Compare the obtained STR profile to a reference profile from a certified cell bank (e.g., ATCC, DSMZ) or the original donor. Due to genetic drift in culture, a perfect match is not always expected.
- Acceptance Criterion: A match of 80% or greater between the test sample and the reference profile is considered authenticated [67].
- Cross-Contamination Indicator: The presence of more than two alleles at three or more loci is a strong indicator of a mixed population and cross-contamination [67].
Mycoplasma Testing
- Acceptance Criterion: All cell lines must test negative for Mycoplasma prior to use in critical experiments or high-throughput screening [6].
Frequency of Testing and Documentation
Authentication is not a one-time event. Testing must be performed at critical points in the cell line's lifecycle.
Table 3: Mandatory Testing Schedule and Documentation
| When to Authenticate | Primary Test(s) | Documentation Requirement |
|---|---|---|
| Upon acquiring a new cell line | STR, Mycoplasma, Morphology | STR profile, Mycoplasma result, passage number |
| When establishing a new frozen stock | STR, Mycoplasma | Entry in cell stock inventory with test data |
| After cells have been in culture for 2-3 months | STR | Updated STR profile at current passage |
| Before starting a new series of experiments | STR, Mycoplasma | Results in experimental notebook |
| When preparing a manuscript for publication | STR, Mycatica | Data for inclusion in Materials & Methods |
| When observing unexpected results or morphology changes | STR, Mycoplasma, Morphology | Investigation report in lab notebook |
The Scientist's Toolkit: Essential Reagents and Materials
Table 4: Key Research Reagent Solutions for Cell Line Authentication
| Item | Function/Description | Example Product/Kit |
|---|---|---|
| STR Multiplex Kit | Contains primers for co-amplifying core STR loci for DNA fingerprinting. | GenePrint 24 System [67] |
| Capillary Electrophoresis System | Instrument for separating and detecting fluorescently labeled STR amplicons to determine allele sizes. | Spectrum Compact CE System [67] |
| Mycoplasma Detection Kit | Biochemical or PCR-based kit for sensitive detection of Mycoplasma contamination in culture media. | MycoAlert Assay [6] |
| Fluorescent DNA Stain | Dye used for microscopic detection of Mycoplasma (e.g., Hoechst 33258) [66]. | Hoechst 33258 |
| Mycoplasma Eradication Reagent | Antibiotic treatment used to decontaminate infected cultures in quarantine. | Plasmocin [6] |
| STR Profile Database | Online repository of reference STR profiles for comparison (e.g., ATCC, DSMZ, Cellosaurus). | ATCC STR Database [66] [67] |
Troubleshooting and Contingency Plans
- STR Match <80% or Evidence of Cross-Contamination: Immediately quarantine the cell culture. Discard the culture and thaw a new, low-passage vial from an authenticated stock. If no stock exists, the cell line must be re-sourced from a certified cell bank [66] [67].
- Mycoplasma Positive Result: Immediately quarantine the cell culture. The preferred action is to discard the culture and replace it from a clean, authenticated stock. In exceptional circumstances where the cell line is irreplaceable, decontamination with an agent like Plasmocin may be attempted in a dedicated quarantine incubator. Success must be confirmed by post-treatment Mycoplasma testing [6].
- Genetic Drift: If a cell line shows consistent, gradual changes in its STR profile over a very high number of passages but remains a single, pure population, it may be necessary to return to an earlier, lower-passage stock to maintain experimental consistency [66].
Building a Defensive Strategy: Preventing Contamination in the Lab
Cell culture serves as an indispensable tool in basic, biomedical, and translational research, yet its reliability hinges entirely on the consistent application of Good Cell Culture Practice (GCCP). Cross-contamination, the unwanted introduction of foreign cells or microorganisms into a culture, represents one of the most significant threats to scientific integrity in cell-based research. The International Cell Line Authentication Committee (ICLAC) registry currently lists 593 misidentified or cross-contaminated cell lines, creating a ripple effect of wasted resources, misleading follow-up studies, and compromised evidence-based conclusions [4]. Astonishingly, rough estimates suggest that approximately 16.1% of published papers have used problematic cell lines, potentially compromising tens of thousands of studies [5]. This technical guide examines the foundations of GCCP with particular emphasis on combating cross-contamination, providing researchers, scientists, and drug development professionals with actionable strategies to ensure data reproducibility and integrity.
Defining Cross-Contamination: Scope and Impact
Cross-contamination in cell culture manifests in several distinct forms, each with unique challenges for detection and prevention:
Inter- and Intra-species Cell Line Cross-Contamination: Occurs when unintended cell lines infiltrate a culture, leading to misidentification. Highly proliferative cell lines like HeLa or HEK293 can overgrow slower-growing populations, fundamentally altering study results [1]. The ICLAC registry documents numerous examples, including liver cell lines (e.g., L-02, WRL 68) that are actually HeLa cervical adenocarcinoma cells [4].
Microbial Contamination: Includes bacteria, fungi, and yeast introduced through improper aseptic techniques, contaminated reagents, or non-sterile equipment [68].
Mycoplasma Contamination: Particularly problematic as it doesn't cause turbidity or other obvious signs, instead altering gene expression, metabolism, and cellular function while remaining undetectable by standard light microscopy [1] [66].
Viral Contamination: Often introduced through contaminated raw materials without causing immediate visible changes in culture conditions [1].
Chemical and Particulate Contamination: Can stem from residual detergents, endotoxins, or extractables from plastic consumables, negatively impacting cell viability and differentiation potential [1].
Quantitative Impact of Cell Line Misidentification
Table 1: Commonly Misidentified Cell Lines in Research [4]
| Cell Line | Claimed Tissue Origin | Actual Identity | Documented Publications |
|---|---|---|---|
| L-02 (HL-7702) | Human liver, normal hepatic cells | HeLa (Cervical adenocarcinoma) | Nearly 6,000 publications using misidentified liver cell lines |
| BEL-7402 | Human hepatocellular carcinoma | HeLa/HCT 8 (Cervical/Colon) | |
| QGY-7703 | Human hepatocellular carcinoma | HeLa (Cervical adenocarcinoma) | |
| WRL 68 | Human embryonic liver cells | HeLa (Cervical adenocarcinoma) | |
| BGC-823 | Human gastric carcinoma | HeLa (Cervical adenocarcinoma) | |
| Chang Liver | Human normal hepatic cells | HeLa (Cervical adenocarcinoma) |
The impact of cross-contamination extends throughout the research ecosystem. A comprehensive PubMed search identified almost 6,000 publications using just five misidentified liver cell lines (QGY-7703, BGC-823, BEL-7402, L-02, and WRL-68), highlighting the staggering dissemination of potentially invalid data [4]. The consequences include irreproducible results, wasted resources estimated in millions of dollars annually, misleading therapeutic targets, and compromised evidence-based conclusions that can stall scientific progress for years.
Core Principles of Good Cell Culture Practice
Implementing GCCP requires a systematic approach to laboratory practice, focusing on six fundamental principles that work synergistically to prevent cross-contamination and maintain research integrity.
Characterization and Maintenance of Essential Characteristics
Proper characterization forms the foundation of reliable cell culture work. This includes:
- Authentication: Verifying cell line identity through STR profiling, DNA barcoding, or isoenzyme analysis [66] [69]
- Functional Characterization: Assessing morphology, growth curve analysis, and specific functional markers [66]
- Stability Monitoring: Regular assessment of genetic and phenotypic stability across passages [69]
Maintaining detailed records of culture history, including passage numbers, media formulations, and any morphological changes, enables researchers to detect subtle deviations that might indicate contamination or genetic drift. Establishing baseline characteristics and comparing them regularly throughout experimentation provides crucial quality control.
Comprehensive Quality Management
Quality management in cell culture encompasses both preventive measures and routine monitoring:
- Standardized Procedures: Developing and adhering to standardized protocols for all cell culture manipulations
- Documentation: Meticulous record-keeping of all procedures, reagents, and observations
- Regular Quality Control: Implementing scheduled testing for microbial contamination, mycoplasma, and cross-contamination
The most cost-effective and efficient methodology for confirming cell line identity has been identified as CO1 DNA Barcoding performed by a commercial vendor [70]. Regular morphological checks, while insufficient alone, provide valuable ongoing monitoring when combined with periodic comprehensive authentication.
Documentation and Reporting Standards
Proper documentation creates an audit trail essential for troubleshooting and reproducibility:
- Cell Line Designation: Using unambiguous, unique designations that maintain donor anonymity when applicable [69]
- Reagent Tracking: Recording sources, batch numbers, and preparation dates for all media and supplements
- Experimental Context: Documenting passage numbers, culture conditions, and any deviations from standard protocols
Publications should include complete cell line designations, authentication methods used, passage numbers under which experiments were conducted, and verification of mycoplasma-free status [69].
Safety Considerations
Safety in cell culture encompasses protection for both the researcher and the cellular environment:
- Biosafety Cabinets: Proper use and regular maintenance of biological safety cabinets [68]
- Personal Protective Equipment: Consistent use of gloves, lab coats, and other barrier protections [68]
- Decontamination Procedures: Established protocols for handling contaminated cultures and waste disposal
For genetically modified cell lines (GMCLs), additional safety considerations and classifications apply, particularly for lines transformed with oncogenic agents or modified using technologies like CRISPR/Cas9 [5].
Education and Training
Proper training in aseptic technique represents the first line of defense against contamination:
- Aseptic Technique: Comprehensive training in maintaining sterility throughout all manipulations
- Mentorship Programs: Pairing inexperienced researchers with skilled mentors
- Continuous Education: Regular updates on emerging best practices and technologies
Human error remains a significant source of contamination, highlighting the critical importance of proper training and adherence to established protocols [1] [68].
Ethical Compliance
Ethical considerations include:
- Donor Consent: Proper informed consent for human-derived materials [69]
- Regulatory Compliance: Adherence to local and international regulations governing tissue use
- Material Transfer Agreements: Proper documentation for shared cell lines
When deriving new cell lines, particularly from human tissues, storing additional material for authentication and histopathological confirmation is essential [69].
Practical Strategies for Preventing Cross-Contamination
Aseptic Technique and Laboratory Practice
Table 2: Essential Practices for Preventing Cross-Contamination [68] [71]
| Practice Category | Specific Measures | Rationale |
|---|---|---|
| Personal Practice | Wear gloves and lab coats; bind long hair; minimize talking; avoid working when ill | Reduces introduction of contaminants from researchers |
| Workspace Management | Work within sterile field of biosafety cabinet; spray everything with 70% ethanol; clean hood before and after use | Maintains sterile environment for cell handling |
| Reagent Handling | Use sterile, single-use consumables; aliquot reagents; filter media through 0.2μm membranes | Prevents introduction of contaminants through reagents |
| Equipment Maintenance | Regular cleaning of incubators and water baths; service biosafety cabinets regularly | Eliminates environmental reservoirs of contamination |
| Cell Handling | Handle one cell line at a time; use dedicated media; implement good labeling practices | Prevents cross-contamination between cell lines |
Cell Line Authentication Methods
Regular authentication represents the most reliable defense against the use of misidentified cell lines. Multiple complementary methods provide layers of verification:
Short Tandem Repeat (STR) Profiling: The gold standard for human cell lines, STR analysis uses multiplex PCR to amplify polymorphic markers, creating a unique DNA fingerprint for each cell line [66] [69]. This method can detect cross-contamination between cell lines through profile discrepancies.
Cytochrome C Oxidase Subunit 1 (CO1) DNA Barcoding: Particularly effective for species verification, this method was identified as the most cost-effective and efficient methodology for confirming cell line identity in a study that discovered commercially marketed rabbit aortic endothelial cells were purely of bovine origin [70].
Isoenzyme Analysis: This technique verifies species of origin through electrophoretic properties of enzymes, simultaneously confirming species identity and revealing contamination by another line of different species [66].
Karyotyping: Analysis of chromosome number and structure provides insights into chromosomal abnormalities and variations, helping distinguish between cell lines with similar morphological characteristics but different chromosomal profiles [72].
Morphological Analysis: Regular observation of physical characteristics under microscopy provides ongoing, though incomplete, verification of cell identity. Changes in morphology can signal potential problems requiring further investigation [66] [72].
Diagram 1: Cell line authentication workflow for research use
Mycoplasma Detection and Prevention
Mycoplasma contamination represents a particularly insidious challenge in cell culture due to its inability to be detected by routine microscopy. Effective management requires:
- Regular Testing: Implementation of periodic PCR, fluorescence staining, or ELISA-based detection methods [1] [71]
- Quarantine Procedures: Isolating new cell lines until mycoplasma status is verified
- Antibiotic Management: Avoiding continuous antibiotic use that can mask contamination
Fluorescent Hoechst staining reveals mycoplasma contamination through characteristic patterns of extracellular particulate or filamentous fluorescence at 500X magnification, providing a relatively easy and reliable detection method [66].
Cell Banking and Passage Management
Proper cell banking practices preserve authentic low-passage cells for future use:
- Master and Working Cell Banks: Establishing comprehensive banking systems with proper documentation
- Passage Number Monitoring: Recording and controlling passage numbers to avoid genetic drift
- Regular Replenishment: Replacing cultures from frozen stocks before excessive passaging
Unlike counting rings in a tree cross-section to determine age, passage number is not a property that can be tested with a straightforward method, making careful documentation essential [66]. Cell lines that have been excessively subcultured can experience phenotypic and genotypic changes (genetic drift), compromising experimental reproducibility.
Table 3: Key Research Reagents and Resources for GCCP Implementation
| Resource Category | Specific Examples | Function in GCCP |
|---|---|---|
| Authentication Services | STR profiling (ATCC), CO1 DNA barcoding, Isoenzyme analysis | Verifies cell line identity and detects cross-contamination |
| Reference Databases | ICLAC Misidentified Cell Line Registry, Cellosaurus, ATCC STR Database | Provides reference data for comparison and contamination alerts |
| Detection Tools | Mycoplasma PCR kits, Hoechst staining, microbial culture tests | Identifies microbial contamination |
| Quality Reagents | Characterized FBS, validated media, sterile consumables | Reduces introduction of contaminants through reagents |
| Documentation Tools | Electronic lab notebooks, cell culture management software | Maintains records for traceability and troubleshooting |
GCCP in Research Versus GMP Environments
While the core principles of GCCP remain consistent across environments, their implementation differs significantly between research and Good Manufacturing Practice (GMP) settings:
Research Laboratories: Focus on data integrity and reproducibility, with contamination primarily affecting experimental outcomes and literature quality [1]. Prevention strategies emphasize aseptic techniques, routine testing, and cell bank validation.
GMP Manufacturing: Emphasizes patient safety, batch consistency, and regulatory compliance, where contamination can lead to batch failures, financial losses, and regulatory action [1]. Prevention requires strict cleanroom standards, closed processing systems, and comprehensive environmental monitoring.
In research settings, contaminated cultures are typically disposed of following biosafety guidelines, while GMP environments require formal quarantine, root cause analysis, and regulatory compliance actions [1].
Good Cell Culture Practice represents far more than a set of technical procedures—it constitutes an essential framework for ensuring the validity and reproducibility of cell-based research. In an era where the reproducibility of scientific findings faces increasing scrutiny, implementing comprehensive GCCP protocols becomes both a scientific and ethical imperative. The pervasive problem of cross-contamination, evidenced by the thousands of publications using misidentified cell lines, highlights the critical need for systematic authentication and quality control measures. By integrating the core principles of characterization, quality management, documentation, safety, education, and ethics, researchers can protect their investments of time and resources while contributing to a more robust and reliable scientific literature. As cell culture continues to evolve with emerging technologies like 3D culture systems and stem cell applications, the foundational principles of GCCP will remain essential for maintaining research integrity across all areas of biomedical science.
In cell line research, cross-contamination—the inadvertent introduction of one cell line into another—poses a significant threat to data integrity, experimental reproducibility, and the validity of scientific conclusions. The International Cell Line Authentication Committee (ICLAC) lists hundreds of misidentified or cross-contaminated cell lines, which can lead to the publication of false and irreproducible results, wasting invaluable resources and time [5]. Unlike microbial contamination, cross-contamination is often invisible, leaving no cloudiness or pH change in the medium. Instead, a more aggressive cell line can silently overgrow the intended culture, fundamentally altering experimental outcomes [73] [1].
Human error is the single greatest risk vector in introducing this and other forms of contamination. Even with advanced automation, personnel can unintentionally become a source of error through lapses in technique, incorrect sampling, or failures in adherence to established protocols [74]. This guide details a systematic approach to aseptic technique, focusing on practical strategies to mitigate human error, thereby safeguarding the purity of cell lines and the integrity of research.
Understanding and Classifying Human Error in the Workflow
In the context of contamination control, human error is seldom a matter of simple carelessness. It is more frequently the consequence of systemic weaknesses, including inadequate training, poorly designed workflows, and cognitive overload [74]. Proactively managing these human factors is as critical as controlling equipment or environmental variables.
Errors can be categorized based on their point of introduction in the research workflow. The table below summarizes common errors, their impact, and the primary preventive strategy.
Table 1: Common Human Errors and Their Impact on Cell Culture
| Error Category | Specific Example | Potential Consequence | Primary Prevention Strategy |
|---|---|---|---|
| Work Area Preparation | Failure to disinfect work surface before and after use [75] [76]. | Introduction of bacterial/fungal contaminants. | Use of checklists and rigorous disinfection protocols. |
| Personal Hygiene & Gowning | Skipping glove changes between handling different cell lines [74]. | Cross-contamination between cell lines. | Strict SOPs, observation, and retraining. |
| Handling & Technique | Talking, whistling, or rapid movement over open containers [75]. | Introduction of airborne microbes; disruption of laminar airflow. | Cultivation of disciplined, slow, and deliberate movements. |
| Reagent & Equipment Management | Using non-sterile or shared reagents/media between cell lines [73] [1]. | Cross-contamination and microbial contamination. | Use of single-use, sterile consumables; dedicated reagents per cell line. |
| Procedural Compliance | Multitasking by handling more than one cell line at a time [73]. | Cross-contamination via aerosols or contaminated pipettes. | Implementing workflow design that enforces sequential processing. |
A Proactive Framework: Strategies to Minimize Human Error
Reducing human-related risk requires a holistic strategy that integrates training, process design, and technology. A robust Contamination Control Strategy (CCS) manages human factors alongside equipment and environmental controls [74].
Comprehensive Training and Competency Assessment
Training must go beyond simply reciting Standard Operating Procedures (SOPs). Personnel should understand the scientific rationale behind each step, as this knowledge significantly improves adherence and reduces mechanical, error-prone execution [74].
- Practical Skill Validation: Competency should be assessed through direct observation, practical testing, and simulated contamination events [74].
- Fight Knowledge Decay: Schedule periodic refresher training and competency evaluations to maintain high levels of skill and operational readiness [74] [76].
Ergonomic Workflow and SOP Design
Processes should be designed to make the correct action the easiest one. A poorly designed workflow can inadvertently increase contamination risk even for well-trained staff [74].
- Minimize Interventions: Arrange workspaces to reduce unnecessary hand movements and crossing over critical open containers [77] [74].
- Visual Management: Use floor markings, signs, and color-coded labels for reagents and equipment to guide behavior and reinforce SOP adherence [74].
- SOP Usability: Write SOPs that are intuitive, with clear step-by-step instructions, visual aids, and checklists. Test SOPs with operators to ensure they are practical and easily understood [74].
Leveraging Technology and Automation
Automation and technology can significantly reduce reliance on human action for critical, repetitive steps.
- Robotics and Automation: The use of robotics for tasks like component addition, sampling, and lyophilizer loading removes a major source of variability and contamination risk [77] [78].
- Single-Use Systems: Pre-sterilized, single-use consumables (flasks, pipettes, closed systems) eliminate complex cleaning and sterilization validation, reducing the risk of human error during these processes [77] [1] [78].
- Real-Time Monitoring: Advanced environmental monitoring systems can provide real-time data on particles and viable microbes, allowing for immediate response to excursions rather than waiting days or weeks for results [78].
The Scientist's Toolkit: Essential Reagents and Materials
The selection of high-quality, verified reagents is a foundational element of contamination prevention. The following table details key materials and their functions in supporting aseptic practice.
Table 2: Key Research Reagent Solutions for Contamination Prevention
| Reagent/Material | Function | Key Consideration |
|---|---|---|
| 70% Ethanol | Broad-spectrum disinfectant for work surfaces, gloves, and outside of containers [75] [76]. | Effective against many bacteria and fungi; allows for sufficient surface contact time. |
| Sterile, Single-Use Pipettes | Aseptic transfer of liquids without cross-contamination [75]. | Use each pipette only once; do not use for multiple cell lines. |
| Chemically Defined, Serum-Free Media | Supports cell growth without the high risk of viral or mycoplasma contamination associated with fetal bovine serum (FBS) [73] [1]. | Reduces adventitious agent risk; improves batch-to-batch consistency. |
| Mycoplasma-Free Certified Cell Lines | Starting material verified free of the most common and insidious contaminant [73] [79]. | Source from reputable cell banks; quarantine and test new lines upon arrival. |
| Pre-Sterilized Single-Use Bioreactors/Culture Vessels | Closed-system culture eliminates cleaning and sterilization steps [77] [78]. | Mitigates risk from improper cleaning or sterilization. |
| Sterile Filter Tips | Prevents aerosol contamination and cross-contamination during pipetting. | Essential when working with multiple cell lines in sequence. |
Experimental Protocol: A Detailed Methodology for Aseptic Cell Passaging
This protocol outlines the critical steps for the aseptic passaging of adherent mammalian cells, incorporating specific checks to mitigate common human errors.
Principle: To detach and subculture adherent cells while maintaining sterility and viability, minimizing the risk of cross-contamination and microbial introduction.
Materials:
- Pre-warmed, antibiotic-free complete medium (to avoid masking low-level contamination [73] [79])
- Dulbecco's Phosphate Buffered Saline (DPBS), without calcium and magnesium
- Trypsin-EDTA or a milder dissociation agent (e.g., Accutase) for sensitive cells [5]
- Trypsin inhibitor or complete medium for neutralization
- T-75 culture flask containing the adherent cell monolayer
- Sterile, single-use pipettes and a pipettor
- 70% ethanol spray and lint-free wipes
- Personal Protective Equipment (PPE): lab coat, gloves, and safety glasses [75]
Procedure:
- Preparation (Error Prevention):
- Disinfect all surfaces of the biosafety cabinet with 70% ethanol before introducing materials [75] [76].
- Wipe the outside of all media and reagent bottles with 70% ethanol before placing them in the cabinet [75].
- Organize the workspace to ensure a logical workflow and prevent overcrowding, which disrupts laminar airflow [76].
Media Aspiration and Washing:
- Carefully aspirate and discard the spent culture medium from the flask.
- Add a sufficient volume of pre-warmed DPBS to the cell monolayer to rinse away any residual serum and calcium, which can inhibit trypsin.
- Gently swirl the flask and aspirate the DPBS completely.
Cell Detachment:
- Add the pre-warmed calculated volume of trypsin-EDTA to cover the monolayer.
- Gently tilt the flask to ensure even coverage.
- Incubate the flask at 37°C for the predetermined time (typically 2-5 minutes). Do not agitate the flask during incubation, as this is a common source of uneven detachment.
Neutralization and Seeding:
- Observe the cells under a microscope to confirm >90% have rounded up and detached.
- Quickly add a pre-determined volume of complete medium (or trypsin inhibitor) to neutralize the trypsin.
- Pipette the cell suspension gently across the surface of the flask to ensure a homogeneous single-cell suspension.
- Transfer the required volume of the cell suspension to a new flask containing fresh, pre-warmed complete medium.
- Cap the flasks securely and place them in the incubator.
The following workflow diagram visualizes this multi-step process and its critical control points.
Monitoring, Auditing, and Cultivating a Culture of Quality
Monitoring Human Performance
A proactive CCS involves continuous monitoring of human performance through direct observation, environmental monitoring data, and deviation reports [74]. Identifying patterns—such as repeated microbial excursions on a specific shift—allows for targeted retraining or workflow modifications.
The Role of Cell Line Authentication
Regular cell line authentication is a critical defense against cross-contamination. Techniques like Short Tandem Repeat (STR) profiling should be performed every 6-12 months to verify cell line identity [73] [5]. This non-negotiable quality control step protects against the use of misidentified lines, which can invalidate entire research programs.
Fostering a Culture of Quality and Accountability
Ultimately, technical controls are only as effective as the culture that supports them. A strong culture of quality encourages personnel to follow procedures meticulously, report deviations without fear, and participate in continuous improvement [74]. Leadership must reinforce that quality and aseptic technique are uncompromising priorities, directly impacting patient safety and scientific discovery.
In cell line research, cross-contamination occurs when an unintended cell line is introduced into a culture, leading to misidentification and invalid experimental outcomes [1]. This problem is not merely a theoretical risk but a widespread issue with profound consequences. The International Cell Line Authentication Committee (ICLAC) registry documents 593 misidentified or cross-contaminated cell lines, creating a ripple effect of wasted resources, misleading follow-up studies, and compromised evidence-based conclusions [4]. In shared research environments, the risk escalates significantly due to improper labeling, inadequate cleaning procedures, or unintentional mixing of cultures [1]. Highly proliferative cell lines, such as HeLa, can overgrow slower-growing populations, fundamentally altering study results and undermining research reproducibility [4] [1]. This guide provides comprehensive strategies for managing multiple cell lines in shared spaces to mitigate these critical risks.
Defining the Problem: Scope and Impact of Cell Line Misidentification
Cell line misidentification and cross-contamination represent a fundamental threat to scientific integrity. The scale of this problem is substantial, with one analysis suggesting that nearly 16.1% of published papers may have used problematic cell lines [5]. The ICLAC registry specifically lists numerous commonly used lines that are, in fact, misidentified.
Table 1: Examples of Commonly Misidentified Cell Lines from the ICLAC Registry [4]
| Misidentified Cell Line | Claimed Tissue Origin | Actual Identity | Contaminating Cell Line |
|---|---|---|---|
| BEL-7402 | Human liver, hepatocellular carcinoma | Cervical adenocarcinoma/colon carcinoma | HeLa/HCT 8 |
| L-02 (HL-7702) | Human liver, normal hepatic cells | Cervical adenocarcinoma | HeLa |
| QGY-7703 | Human liver, hepatocellular carcinoma | Cervical adenocarcinoma | HeLa |
| WRL 68 | Human liver, embryonic cells | Cervical adenocarcinoma | HeLa |
| BGC-823 | Human gastric carcinoma | Cervical adenocarcinoma | HeLa |
| Chang Liver | Human liver, normal hepatic cells | Cervical adenocarcinoma | HeLa |
The impact of using misidentified cells extends beyond individual experiments. Researchers drawing conclusions about disease mechanisms, drug responses, and gene regulation based on contaminated lines generate invalid data that misdirects scientific progress and jeopardizes the development of future therapies [4]. The scientific community incurs substantial costs through irreproducible studies, with one analysis identifying almost 6,000 publications that have used just five of the known misidentified liver cell lines [4].
Foundational Prevention Strategies in Shared Spaces
Implementing robust logistical and procedural frameworks is the first line of defense against cross-contamination in multi-user laboratories.
Aseptic Technique and Sterile Work Area Management
Maintaining aseptic conditions is non-negotiable. The core principle is to create a barrier between microorganisms in the environment and the sterile cell culture [75]. Key practices include:
- Work Area Discipline: The biosafety cabinet should be in a low-traffic area, free from drafts. The work surface must be uncluttered and thoroughly disinfected with 70% ethanol before and during work, especially after any spillage [75].
- Sterile Handling: Always wipe gloved hands and the outside of all containers with 70% ethanol before introducing them into the cabinet. Avoid pouring media directly from bottles; instead, use sterile pipettes. Never leave sterile containers uncovered, and if a cap must be placed down, position it with the opening facing down [75].
- Personal Protective Equipment (PPE): Proper PPE forms a crucial barrier between personnel and cell cultures, while also reducing the probability of contamination from shed skin or clothing particles [75].
Procedural and Administrative Controls
- Scheduling and Access: Implement a scheduling system for shared equipment like biosafety cabinets and incubators to reduce user traffic and crowding, minimizing the opportunity for errors and cross-contamination [1].
- Single-Use Consumables: Whenever possible, use pre-sterilized, single-use consumables such as culture flasks and disposable pipettes to eliminate risks from improper cleaning and sterilization of reusable items [1].
- Dedicated Reagents: Assign dedicated media, reagents, and pipettes for each cell line worked on in a shared space. This prevents a contaminant from one cell line from being transferred to another via a shared reagent bottle [1].
Technical Solutions for Authentication and Tracking
Beyond preventative practices, leveraging technical tools for authentication and sample tracking is essential for ensuring long-term cell line integrity.
Cell Line Authentication Methods
Regular authentication is a critical quality control measure. Key methodologies include:
- Short Tandem Repeat (STR) Profiling: This is the gold-standard method for authenticating human cell lines. It analyzes highly variable regions of the genome to create a unique genetic fingerprint for each cell line, which can be compared to reference databases [5].
- Morphological Verification: Routine microscopic observation of cells in culture helps researchers become familiar with the characteristic shape and growth pattern of their cell lines. Significant, persistent changes in morphology can be an early indicator of potential contamination or misidentification [80].
- Isoenzyme Analysis: This method can be used to confirm the species of origin by examining the pattern of enzyme variants specific to different species [80].
- Mycoplasma Testing: Contamination with mycoplasma does not cause turbidity but can alter gene expression, metabolism, and cellular function, leading to misleading results. Routine screening via PCR, fluorescence staining, or ELISA-based assays is necessary as mycoplasma cannot be detected by standard light microscopy [1].
Digital Management and Sample Tracking
Manual record-keeping is prone to error. Digital systems provide a robust solution for managing complex cell line information.
- Sample Lineage Records: Software tools can automatically track the ancestor samples of any cell line as cells are passaged and new banks are created, creating a complete audit trail [81].
- Comprehensive Storage Management: Digital systems can accurately model the entire hierarchy of sample storage, including liquid nitrogen tanks and ultra-low temperature (ULT) freezers, helping users quickly identify free space and locate specific vials [81] [82].
- Barcode Integration: Scanning barcoded vials, flasks, and media bottles into a digital system automatically tracks passage numbers, media lot numbers, and parent-child relationships, drastically reducing manual entry errors [82].
The following workflow diagram summarizes the integrated process for managing cell lines from introduction to the lab through their experimental use, incorporating key authentication and tracking checkpoints.
The Scientist's Toolkit: Essential Research Reagents and Solutions
A successful cell culture laboratory relies on a suite of essential reagents and materials, each with a specific function in maintaining cell health and preventing contamination.
Table 2: Essential Research Reagents and Solutions for Cell Culture Management
| Item | Primary Function | Key Considerations |
|---|---|---|
| Standard Media (DMEM, RPMI) | Provides essential nutrients (carbohydrates, amino acids, vitamins, salts) for cell growth and maintenance [5]. | Should be supplemented with serum or defined growth factors; use pre-screened, low-endotoxin lots. |
| Cell Dissociation Reagents (Trypsin, Accutase) | Detaches adherent cells for subculturing (passaging) [5]. | Enzymatic activity can degrade surface proteins; milder alternatives (Accutase) preserve epitopes for analysis [5]. |
| Sterile Phosphate-Buffered Saline (PBS) | Used for washing cells to remove residual media, serum, or dissociation agents. | A calcium- and magnesium-free solution is typically used to prevent cell clumping. |
| Cryopreservation Medium | Protects cells during freezing and long-term storage in liquid nitrogen. | Typically contains a high concentration of serum and a cryoprotectant like DMSO. |
| 70% Ethanol Solution | The primary disinfectant for decontaminating work surfaces, gloves, and the outside of containers [75]. | Effective against a broad spectrum of microbes; evaporates quickly without leaving a residue. |
| Validated Sera (e.g., FBS) | Provides a complex mixture of growth factors, hormones, and attachment factors. | A major source of potential viral or mycoplasma contamination; use virus-inactivated, characterized lots. |
Special Considerations for GMP vs. Research Environments
While the core principles of contamination prevention are consistent, their implementation differs significantly between research and Good Manufacturing Practice (GMP) environments, primarily due to the focus on patient safety and regulatory compliance in the latter.
- Impact of Contamination: In research, contamination primarily affects data integrity and reproducibility, leading to wasted resources and misleading publications [1]. In GMP manufacturing, contamination presents serious financial, regulatory, and patient safety risks, potentially leading to entire batch failures and regulatory action [1].
- Prevention Strategies: Research labs focus on aseptic techniques, routine testing, and cell bank validation [1]. GMP facilities employ more stringent measures, including HEPA-filtered cleanrooms, closed processing systems, rigorous environmental monitoring, and full batch traceability to ensure patient safety and meet regulatory standards like FDA 21 CFR 211.113 [1].
- Facility Design: For advanced therapies like cell therapy products, GMP layout requires strict segregation of core functional zones, including dedicated warehousing, production, and QC laboratory areas, to prevent cross-contamination between products and processes [83].
The integrity of biomedical research hinges on the authenticity of its fundamental tools, with cell lines serving as a cornerstone for countless experiments. However, the widespread cross-contamination and misidentification of these cell lines present a grave and persistent threat to scientific validity. This problem is particularly acute when cell lines are acquired from non-repository sources, such as other laboratories, where the chain of custody is informal and quality control is variable. Cross-contamination occurs when a fast-growing cell line is inadvertently introduced into another culture, eventually overgrowing and replacing the original cell line [84]. Misidentification can arise from this cross-contamination or from simple mislabeling. Despite being a known issue for more than six decades, it remains a significant source of erroneous and irreproducible data, wasting invaluable research resources and time [84] [26].
The historical context of this issue is epitomized by the HeLa cell line. Shortly after its establishment in the 1950s, scientists observed that this vigorous line could contaminate and overgrow slower-growing cultures [84]. In the 1960s, Stanley Gartler used isoenzyme analysis to demonstrate that 18 cell lines of presumed independent origin were, in fact, HeLa contaminants [84]. Tragically, this legacy continues. A 2008 analysis of 40 human thyroid cancer cell lines revealed only 23 unique genetic profiles, with many cross-contaminated lines not even being of thyroid origin, meaning they had been incorrectly used in thyroid cancer research for two decades [84]. This underscores the critical need for source vigilance, as the use of unauthenticated materials jeopardizes the entire scientific enterprise.
Quantitative Evidence: The Scale of the Problem
The scope of cell line misidentification is not trivial. It is estimated that 15–20% of cell lines currently in use may not be what they are documented to be [84]. A 2004 survey highlighted a widespread lack of vigilance, with more than a third of over 400 respondents obtaining cell lines from other laboratories, and almost half failing to perform any identity testing [84].
Table 1: Prevalence of Cell Line Cross-Contamination and Misidentification
| Study / Context | Sample Size | Misidentification Rate | Most Common Contaminants |
|---|---|---|---|
| General Estimate [84] | N/A | 15-20% | HeLa and other fast-growing lines |
| Survey of Labs (2004) [84] | >400 respondents | ~50% (no identity testing) | N/A |
| Tumor Cell Lines in China [21] | 278 cell lines | 46.0% (128/278) | HeLa (46.9% of contaminants) |
| Cell Lines from Non-Repository Sources [84] | >400 survey respondents | ~33% obtained from other labs | N/A |
| Chinese-origin Cell Models [21] | 71 cell lines | 73.2% (52/71) | HeLa or HeLa hybrids (67.3%) |
Recent empirical evidence paints a starker picture. A 2017 study analyzing 278 widely used tumor cell lines from 28 institutes in China found a staggering 46% misidentification rate [21]. The data becomes even more revealing when comparing cell line origins. The misidentification rate for cell lines established outside China was 33.2%, which is concerning enough. However, for cell lines established within Chinese laboratories, the rate soared to 73.2% [21]. Among these misidentified Chinese-origin cell lines, 67.3% were HeLa cells or a possible hybrid of HeLa and another cell line [21]. This quantitative data unequivocally demonstrates that obtaining cell lines from non-curated, non-repository sources dramatically increases the risk of working with a false cell line.
Consequences of Using Misidentified Cell Lines
The repercussions of using misidentified cell lines are severe and far-reaching, affecting everything from individual research projects to the broader scientific landscape.
- Invalidated Research Findings: Data generated from a misidentified cell line is, by definition, unreliable. It reflects the biology of the contaminating cell line, not the presumed model system. This leads to the publication of false conclusions, which can misdirect entire research fields for years, as seen in the case of thyroid cancer research [84].
- Irreproducibility of Results: The reproducibility crisis in science is exacerbated by the use of unauthenticated materials. When one laboratory publishes findings using a particular cell line, and another lab attempts to replicate the work using a different, misidentified cell line also purporting to be the same model, the experiments will inevitably fail, wasting time and funding.
- Wasted Resources and Economic Impact: Billions of dollars in research funding are consumed by studies that use false cell lines. This includes the costs of reagents, personnel time, and animal experiments. Furthermore, the development of a misidentified cell line can render manuscripts unpublishable after project completion, negating years of effort [84].
- Ethical and Safety Concerns: The use of misidentified cells is an ethical breach, as it misuses public and private funds and violates the trust inherent in the scientific process. From a safety perspective, some cell lines are known to harbor pathogens, and working with cells of unknown origin can pose a biosafety risk to laboratory personnel [5].
Authentication Methodologies: The Scientific Toolkit
Preventing the use of misidentified cell lines requires rigorous and regular authentication. Several methodologies have been established as standards for confirming cell line identity.
Short Tandem Repeat (STR) Profiling
STR profiling has become the international reference standard for the intra-species identity testing of human cell lines [84] [43]. This method measures the exact number of repeating nucleotides at multiple polymorphic loci in the genome. The combination of allele sizes across these loci creates a unique DNA fingerprint for each cell line.
- Principle: The technique is a PCR-based analysis that simultaneously amplifies multiple STR loci. The number of repeats at each locus is highly variable between individuals, creating a unique profile [84].
- Protocol:
- DNA Extraction: Isolate genomic DNA from the cell line to be tested.
- PCR Amplification: Amplify multiple selected STR loci using fluorescently labeled primers in a multiplex PCR reaction.
- Capillary Electrophoresis: Separate the amplified fragments by size using capillary electrophoresis.
- Data Analysis: Determine the allele sizes (number of repeats) for each locus. Compare the resulting profile to reference databases, such as those from ATCC or DSMZ, to find a match or confirm uniqueness [84] [21].
- Advantages: STR profiling is a rapid, high-throughput, and highly discriminatory technique. It is the method endorsed by major cell banks and is increasingly required by scientific journals prior to publication.
Isoenzyme Analysis
Isoenzyme analysis is a traditional method primarily used for detecting inter-species cross-contamination.
- Principle: This technique uses band patterns from the electrophoresis of proteins to detect species-specific differences in the structure and mobility of intracellular enzymes [84] [43].
- Protocol:
- Cell Lysis: Lyse cells to release intracellular enzymes.
- Gel Electrophoresis: Separate the enzymes on a non-denaturing gel based on their charge and size.
- Enzyme-Specific Staining: Apply a substrate stain specific to a particular enzyme (e.g., lactate dehydrogenase, glucose-6-phosphate dehydrogenase). The resulting band patterns are species-characteristic [43].
- Advantages: The technique is robust and returns rapid results. However, it can be subject to low reproducibility and is not suitable for detecting intra-species contamination [84].
Karyotyping
Karyotyping, or the cytogenetic analysis of stained chromosomes, is a traditional test for cell line identity that provides information on the genomic stability of a cell line.
- Principle: It involves the microscopic examination of chromosomes to determine their number, size, shape, and banding pattern [84].
- Protocol:
- Cell Arrest and Harvesting: Treat cells with a mitotic inhibitor (e.g., colcemid) to arrest them in metaphase. Harvest the cells.
- Hypotonic Treatment and Fixation: Swell the cells in a hypotonic solution and fix them with Carnoy's fixative (methanol:acetic acid).
- Slide Preparation and Staining: Drop the cell suspension onto slides to spread the chromosomes. Stain the chromosomes with Giemsa stain (G-banding) or other dyes.
- Microscopy and Analysis: Analyze the stained chromosomes under a microscope to create a karyotype [43].
- Advantages: Karyotyping can reveal large-scale genetic changes, such as aneuploidy or translocations, that may occur with long-term culture ("genetic drift") [84].
Table 2: Cell Line Authentication Methods
| Method | Primary Application | Key Principle | Advantages | Disadvantages |
|---|---|---|---|---|
| STR Profiling [84] [43] | Intra-species authentication | Analysis of polymorphic short tandem repeat loci in DNA | High discrimination; gold standard for human cells; high-throughput | Requires reference database |
| Isoenzyme Analysis [84] [43] | Inter-species detection | Electrophoretic separation of species-specific enzyme isoforms | Rapid; robust; low cost | Low reproducibility; poor intra-species discrimination |
| Karyotyping [84] [43] | Genetic stability & identity | Microscopic examination of chromosome number and structure | Detects genetic drift and large-scale changes | Labor-intensive; low resolution |
A Proactive Approach: Prevention and Best Practices
Mitigating the risks associated with non-repository cell acquisition requires a proactive, multi-faceted approach centered on good cell culture practices (GCCP).
Diagram 1: A workflow for preventing cell line misidentification, from sourcing to use.
- Source from Reputable Cell Banks: The single most effective action is to obtain cell lines from reputable cell banks like the American Type Culture Collection (ATCC) or the European Collection of Authenticated Cell Cultures (ECACC) [57]. These repositories perform rigorous authentication and quality control, providing a validated starting point for research.
- Implement Authentication at Key Stages: Cell line authentication should not be a one-time event. It should be performed upon receipt of a new cell line, at the establishment of master and working cell banks, and at regular intervals during extended culture (e.g., every 3 months or after 10 passages). Crucially, authentication should be performed before publication of any findings [84].
- Adopt Good Cell Banking Practices: Researchers should establish a system of master cell banks (MCBs) and working cell banks (WCBs) frozen at early passages. This ensures a continuous supply of low-passage, authenticated cells, reducing the impact of genetic drift and providing a fallback if working stocks become contaminated [84].
- Maintain Meticulous Documentation: Accurate and legible labeling of all cell culture vessels and vials is essential. Labels must withstand ultra-low temperature storage, and detailed inventory records must be kept to prevent misidentification due to mislabeling or the use of unlabeled vials [84].
- Practice Rigorous Aseptic Technique: Preventing cross-contamination in the first place is paramount. This includes using biosafety cabinets correctly, regularly cleaning shared equipment, and avoiding the handling of multiple cell lines simultaneously [57].
Table 3: Essential Research Reagent Solutions for Authentication
| Reagent / Tool | Function in Authentication | Example Use Case |
|---|---|---|
| STR Multiplex Kits [84] | Simultaneously amplifies multiple polymorphic STR loci for DNA fingerprinting. | Generating a unique genetic profile for a human cell line to compare against a reference database. |
| Isoenzyme Analysis Gels [43] | Separates enzyme isoforms by electrophoresis to reveal species-specific band patterns. | Quickly checking a new culture for inter-species contamination (e.g., mouse in human). |
| Cell Dissociation Reagents [5] | Detaches adherent cells for subculturing or preparation for analysis without degrading epitopes. | Harvesting cells for DNA extraction for STR profiling or for flow cytometry. |
| Mycoplasma Detection Kits [57] | Detects the presence of mycoplasma, a common biological contaminant that can alter cell behavior. | Routine screening to ensure cell culture health and validity of experimental results. |
The Path Forward: A Collective Responsibility
Addressing the problem of cell line misidentification requires a concerted effort from all stakeholders in the scientific community. Researchers must take personal responsibility for authenticating their cell lines and adhering to good cell culture practices. Funding agencies and peer-reviewed journals play a pivotal role by making cell line authentication a mandatory condition for grant approval and manuscript publication, a policy that an increasing number of journals are adopting [84]. Organizations like the International Cell Line Authentication Committee (ICLAC) provide critical resources, such as the Register of Misidentified Cell Lines, to guide researchers [84].
In conclusion, while the acquisition of cell lines from non-repository sources presents a severe and documented risk to research integrity, the solutions are readily available. By practicing source vigilance—prioritizing acquisition from authenticated repositories and implementing routine, rigorous identity testing—the scientific community can safeguard the validity of its work, ensure the reproducibility of findings, and make the most efficient use of precious research resources. The time and cost of authentication are negligible compared to the price of building a scientific legacy on a foundation of false cells.
Establishing and Validating Master Cell Banks
The establishment and validation of a Master Cell Bank (MCB) is a critical milestone in the development of biopharmaceuticals, cell therapies, and biomedical research. This process ensures a consistent, well-characterized, and secure starting material for all production and testing activities. Operating within the context of a broader thesis on cross-contamination in cell line research, this technical guide details how robust MCB practices serve as a fundamental defense against the pervasive problem of cell misidentification and contamination. It provides researchers, scientists, and drug development professionals with in-depth methodologies, validation protocols, and quality control measures essential for creating a reliable MCB, thereby safeguarding product safety, efficacy, and data integrity.
Cell line cross-contamination and misidentification represent a "silent and neglected danger" that has compromised biomedical research for decades [85]. Estimates suggest that 15–20% of cell lines currently in use may not be what they are documented to be, leading to invalidated research results, irreproducible data, and compromised therapeutic products [86]. The International Cell Line Authentication Committee (ICLAC) lists 576 misidentified or cross-contaminated cell lines in its latest register, highlighting the scale of this persistent issue [5].
A Master Cell Bank (MCB) is defined as "an aliquot of a single pool of cells that generally has been prepared from the selected cell clone under defined conditions, dispensed into multiple containers, and stored under defined conditions" [87]. It serves as the primary and characterized source of cells from which all subsequent cell banks, such as Working Cell Banks (WCBs), and production batches are derived [88]. The rigorous establishment and validation of an MCB is therefore the first and most crucial barrier against cross-contamination. It provides a uniform composition from a single source, enabling traceability and ensuring that any cell-based product or research has a consistent, authentic, and well-documented origin [89]. This practice is indispensable for adhering to Good Cell Culture Practice (GCCP) and is a regulatory expectation for biologics development [5] [90].
Master Cell Bank vs. Working Cell Bank: A Tiered System
In a standardized two-tiered cell banking system, the MCB and WCB serve distinct but interconnected purposes. The table below summarizes the key differences.
Table 1: Key Differences Between Master Cell Bank (MCB) and Working Cell Bank (WCB)
| Aspect | Master Cell Bank (MCB) | Working Cell Bank (WCB) |
|---|---|---|
| Source | Cell lines established from engineered cells, or isolated from original tissue [88]. | Aliquots derived from the expansion of a single MCB vial [88]. |
| Purpose | Establish a large repository of extensively characterized cells that serve as the stable and consistent starting material for all production [88]. | Provide a renewable and consistent source of cells for day-to-day manufacturing and research needs [88]. |
| Characterization & Testing | Undergoes rigorous and comprehensive testing for identity, purity, sterility, and genetic stability [90] [87]. | Abbreviated testing compared to MCB, primarily focused on sterility and adventitious agents that may have been introduced during banking [90] [91]. |
| Frequency of Use | Used infrequently as a stable reference; vials are only accessed to create new WCBs [88]. | Used regularly as the direct source for production or experimental work [88]. |
| Regulatory Status | Requires full GMP-compliant characterization and is a key part of regulatory submissions [90]. | Testing, while less extensive, must still be performed under appropriate quality systems [91]. |
The logical workflow of this system ensures that the integrity of the original MCB is preserved while providing a functional supply of cells for ongoing use.
Establishing a Master Cell Bank: A Step-by-Step Protocol
Cell Line Sourcing and Prequalification
The process begins with the careful selection and acquisition of the cell line. Sourcing from reputable cell banks like the American Type Culture Collection (ATCC) or the European Collection of Authenticated Cell Cultures (ECACC) is recommended, as they provide authenticated and characterized cells [86]. For in-house developed lines, meticulous documentation of the isolation and transformation process is critical. Before MCB generation, a risk-based prequalification assessment is advised. For higher-risk cells (e.g., those from other labs with poor documentation), initial tests for mycoplasma, sterility (without antibiotics), and identity (e.g., STR profiling or isoenzyme analysis) should be performed to ensure the cells are suitable for banking [91].
Cell Banking Facilities and Equipment
MCB preparation requires a dedicated laboratory space with specialized equipment to ensure sterility, containment, and reproducibility [87]. Key components include:
- Biosafety Cabinets (BSCs): Class II BSCs are standard for non-hazardous cell lines, while Type B2 (100% exhaust) are used for viral vector work or primary human cells [87].
- CO₂ Incubators: Dual-stack systems provide redundancy [87].
- Cryopreservation Equipment: Controlled-rate freezers are used to ensure consistent and viable freezing of cell aliquots [88].
- Storage Systems: Liquid nitrogen (LN₂) freezers, preferably in the vapor phase (below -130°C), are the standard for long-term storage of MCBs to ensure genetic stability and viability [90] [87].
MCB Manufacturing Workflow
The following diagram and protocol detail the core process of creating an MCB.
- Cell Expansion: A prequalified cell clone is expanded under defined and stable culture conditions. The passage number should be kept as low as possible (e.g., passage 2) to minimize genetic drift [89].
- Harvest and Pool: Cells are harvested using a gentle dissociation reagent (e.g., Accutase or a non-enzymatic solution) to preserve cell surface proteins and viability [5]. The cell population is pooled to create a single, homogeneous suspension.
- Cryopreservation and Aliquoting: The cell pool is mixed with a cryoprotectant (e.g., DMSO), dispensed in uniform aliquots into cryovials, and frozen using a controlled-rate freezer. Vials must be legibly and indelibly labeled with the cell line name, passage number, and a unique MCB identifier [88] [7].
- Documentation: Comprehensive records of the entire process, including the history and certificates of analysis for all raw materials (especially animal-derived components like FBS), must be maintained. This traceability is crucial for regulatory acceptance [90].
Validating and Characterizing the Master Cell Bank
MCB characterization is a rigorous process driven by international quality guidelines like ICH Q5A(R1), Q5B, and Q5D [90]. The testing strategy is designed to confirm three fundamental attributes: identity, purity, and stability/function.
Table 2: Master Cell Bank Characterization and Validation Tests
| Test Category | Specific Assays | Purpose & Rationale |
|---|---|---|
| Identity | Short Tandem Repeat (STR) Profiling [43] [86] | The standard method for intra-species authentication of human cell lines. Creates a unique DNA fingerprint. |
| Isoenzyme Analysis [43] [86] | Rapid technique for detecting inter-species cross-contamination. | |
| Karyotyping [86] | Examines chromosomal number and structure to assess genotypic stability and identify major abnormalities. | |
| Purity & Safety | Sterility Testing [90] [87] | Detects bacterial and fungal contaminants. |
| Mycoplasma Testing [90] [87] | Essential test for this common, non-visible contamination that can alter cell behavior. | |
| Adventitious Virus Testing [90] [87] | In vitro and in vivo assays to detect viral contaminants. | |
| Tests for Species-Specific Viruses | Based on the cell line's species (e.g., retroviruses for murine cells) [90]. | |
| Stability & Function | Genetic Stability [90] [87] | Ensures the gene encoding the product is stable through the intended production lifespan. |
| Potency / Bioassay [91] [89] | Validates the biological functionality and activity of the cells or the product they are engineered to produce. | |
| Growth Kinetics & Viability [89] | Assesses population doubling time and post-thaw recovery. |
The following diagram illustrates the logical strategy for releasing a fully validated MCB.
The Scientist's Toolkit: Essential Reagents and Materials
The following table details key reagents and materials critical for successful MCB establishment and validation.
Table 3: Essential Research Reagent Solutions for MCB Development
| Reagent / Material | Function in MCB Process | Key Considerations |
|---|---|---|
| Chemically Defined Media | Supports cell growth and proliferation in a consistent, serum-free formulation. | Reduces variability and risk of adventitious agents from animal sera; supports regulatory compliance [90]. |
| Gentle Dissociation Agents (e.g., Accutase) | Detaches adherent cells for passaging and banking while preserving surface epitopes. | Prevents degradation of cell surface proteins that can occur with trypsin, crucial for subsequent flow cytometry or phenotyping [5]. |
| Cryoprotectants (e.g., DMSO) | Protects cells from ice crystal formation and damage during the freezing process. | Concentration and cooling rate must be optimized for each cell type to maximize post-thaw viability [87]. |
| Authentication Kits (STR, Mycoplasma PCR) | Validates cell line identity and ensures freedom from mycoplasma contamination. | STR profiling is the gold standard for human cell lines. PCR-based mycoplasma testing is fast and sensitive [91] [86]. |
| Quality-Controlled Sera & Reagents | Provides essential growth factors and nutrients in culture media. | Sourcing with full traceability and certificates of analysis (CoA) is critical for risk assessment, especially for animal-derived materials [90]. |
The establishment and validation of a Master Cell Bank is a foundational discipline in biomedical research and biopharmaceutical development. By implementing the detailed protocols and validation strategies outlined in this guide—from rigorous prequalification and aseptic banking practices to comprehensive identity and safety testing—scientists can create a robust and reliable MCB. This MCB serves as a bulwark against the pervasive threat of cross-contamination, ensuring a consistent and authentic cell source. Ultimately, a well-characterized MCB is not merely a regulatory requirement; it is a critical investment that underpins the integrity of scientific data, the safety of biologics and cell therapies, and the success of the entire development pipeline.
Contamination in cell culture is a critical crisis that can compromise data integrity, invalidate research findings, and lead to massive financial losses, with one misidentified cell line potentially wasting over $50 billion in research funds [92]. Within the broader context of cross-contamination in cell lines, where fast-growing cells like HeLa can silently overgrow and replace other cultures, a structured and immediate response is essential to manage the incident and safeguard scientific integrity [4] [93]. This guide provides a detailed protocol for researchers and drug development professionals to follow when contamination is detected.
Immediate Response and Containment
The initial moments after detecting contamination are crucial for preventing its spread. The immediate goals are to isolate the threat and preserve evidence for the subsequent investigation.
Confirm and Document the Contamination: Use appropriate detection methods to confirm the contaminant type. Under a microscope, bacteria may appear as tiny, moving granules; yeast as ovoid, budding particles; and molds as thin, filamentous hyphae [57] [93]. Document all observations with images and notes on culture morphology, medium turbidity, and pH changes [57].
Isolate the Contaminated Culture: Immediately move the contaminated culture away from all other cell lines and working areas [57]. Quarantine not only the flask or dish in question but also all media, reagents, and consumables that have been in contact with it.
Contain the Area: Decontaminate all work surfaces, incubators, and biosafety cabinets that may have been exposed [57] [94]. Restrict access to the affected area if the scale of the incident is large. Notify all laboratory personnel working in the vicinity to heighten awareness and prevent accidental spread [95].
Investigation and Root Cause Analysis
Once the immediate threat is contained, a thorough investigation must be launched to identify the root cause and determine the extent of the impact.
Contaminant Identification and Testing
Accurately identifying the contaminant is the first step in the investigative process. The table below summarizes standard testing methods.
Table 1: Contaminant Identification Methods
| Contaminant Type | Primary Detection Methods | Key Characteristics |
|---|---|---|
| Bacteria | Microbial culture, Gram stain, PCR | Turbid culture, rapid pH drop (acidic) [57] [93] |
| Yeast/Fungi | Microbial culture, visual inspection | Turbid culture, visible mycelia (mold), sometimes odor [57] [93] |
| Mycoplasma | PCR, Hoechst staining, specialized kits | No visible turbidity; alters cell physiology and gene expression [1] [57] [96] |
| Virus | PCR, electron microscopy, immunoassays, in vivo testing | Often cryptic; may require co-cultivation or advanced sequencing [57] [93] [95] |
| Cellular Cross-Contamination | STR profiling, NGS-based authentication, karyotyping | Misidentified cell line; overgrowth by a faster-growing line (e.g., HeLa) [4] [92] [96] |
Determine the Scope of Impact
After identifying the contaminant, assess how far it has spread.
- Test Related Cultures: Check all cell cultures that were handled in the same biosafety cabinet, stored in the same incubator, or used in concurrent experiments [94].
- Audit Reagents and Media: Test batches of culture media, serum, and other reagents that were in use when the contamination was first suspected, as these can be common sources [97].
- Environmental Sampling: In severe or recurring cases, swab surfaces such as biosafety cabinet workstations, incubator shelves, and shared equipment to identify environmental reservoirs [94].
The following workflow outlines the comprehensive crisis management process from detection to resumption of work.
Decontamination, Remediation, and Restoration
The course of remediation depends on the value of the contaminated culture and the nature of the contaminant.
Decontamination and Disposal
For most routine contaminations, the safest and most recommended action is prompt disposal.
- Standard Procedure: Dispose of the contaminated culture according to your institution's biological waste guidelines, typically by autoclaving [1].
- Decontamination Attempts: Decontamination should only be considered for irreplaceable cell lines. This involves treating the culture with high concentrations of antibiotics or antimycotics, but it requires a careful dose-response test to determine levels that are toxic to the contaminant but not the cells. Success is not guaranteed, and the decontaminated culture must be rigorously monitored [57].
Restoring Authentic Cultures
Before restarting experiments, it is imperative to establish a clean, authenticated cell stock.
- Return to Authenticated Stocks: Use a frozen stock from a certified cell bank that has been previously authenticated and tested for contaminants [1] [57]. If no authenticated stock exists, obtain a new one from a reputable bank.
- Cell Line Authentication: Authenticate your cell lines upon receipt and at regular intervals during maintenance. The International Cell Line Authentication Committee (ICLAC) lists nearly 600 misidentified cell lines, underscoring the prevalence of this issue [4].
Table 2: Cell Line Authentication & Contamination Detection Methods
| Method | Technology | Key Function | Throughput | Relative Sensitivity |
|---|---|---|---|---|
| STR Profiling | Multiplex PCR of short tandem repeats | Human cell line identity confirmation | Low | ~5-10% contamination [92] |
| NGS-based SNP Profiling | Next-generation sequencing of 600+ SNPs | Identity confirmation for human/mouse lines; detects genetic drift | High | Outperforms STR [92] |
| Mycoplasma PCR | Polymerase chain reaction | Detects mycoplasma DNA | Medium | High [57] [96] |
| Karyotyping | Chromosome analysis | Confirms species and reveals gross genetic abnormalities | Low | Low |
The following diagram details the decision-making process for selecting the appropriate authentication method based on the sample type and required information.
Essential Research Reagent Solutions
The table below lists key reagents and tools used in contamination prevention, detection, and cell line authentication.
Table 3: Research Reagent Solutions for Contamination Control
| Reagent / Tool | Function | Example Use Case |
|---|---|---|
| Antibiotics/Antimycotics | Suppress bacterial and fungal growth | Short-term use during culture establishment; not recommended for long-term cultures [57] |
| Mycoplasma Detection Kit | Specific detection of mycoplasma contamination | Routine screening of cell stocks and cultures using PCR or fluorescence staining [96] |
| STR Profiling Kit | DNA fingerprinting for human cell line identity | Authenticating a new cell line upon arrival in the lab [92] [96] |
| NGS Authentication Panel | High-throughput SNP profiling for identity and purity | Comprehensive authentication of a large biobank of cell lines [92] |
| Gamma-Irradiated Serum | Virus-inactivated serum for media preparation | Mitigating risk of viral contamination from animal-derived reagents [93] [95] |
| HEPA-Filtered Biosafety Cabinet | Provides a sterile workspace for cell handling | Primary engineering control for preventing environmental contamination during all cell culture procedures [1] [93] |
Special Considerations for Different Environments
The context of the contamination dictates specific aspects of the response.
In a Research Laboratory
The primary impact is on data integrity and reproducibility. The response should focus on identifying all affected experiments, halting their use, reculturing authenticated cells, and repeating the experiments where necessary [1]. The financial cost lies in wasted time and resources.
In a GMP Bioproduction Facility
Contamination presents a serious risk to patient safety, batch consistency, and regulatory compliance [1] [97]. The response is far more stringent and must follow established Standard Operating Procedures (SOPs). Key steps include:
- Quarantine and Investigation: A full root cause analysis is mandatory, documented in a deviation report [94] [95].
- Regulatory Compliance Actions: Document all actions and report serious events to regulatory bodies like the FDA [1] [94].
- Batch Failure: The entire affected batch must be rejected, leading to significant financial loss and potential drug shortages [97] [95].
Corrective and Preventive Actions (CAPA)
The ultimate goal of a contamination crisis is to learn from it and prevent recurrence.
- Review and Train: Reinforce staff training on aseptic technique, which is the most critical factor in preventing contamination [1] [93]. This includes proper use of biosafety cabinets, avoiding simultaneous work with different cell lines, and rigorous cleaning protocols.
- Revise Protocols: Update SOPs based on the investigation's findings. This may include mandating regular cell line authentication or more frequent environmental monitoring [94].
- Establish a Rigorous Quality Control Program: Implement routine scheduled testing for mycoplasma and microbial contamination. Authenticate all cell lines upon acquisition, before freezing down stocks, and at regular intervals during extended culture [92] [96].
A contamination event is a serious setback, but a systematic, thorough, and documented response can not only manage the immediate crisis but also strengthen your laboratory's overall research integrity and operational resilience.
Ensuring Integrity: Validation Protocols and Evolving Standards
In cell line research, cross-contamination represents one of the most significant yet preventable threats to scientific integrity and reproducible research. This phenomenon, where foreign cells or microorganisms are inadvertently introduced into a cell culture, has reached alarming prevalence. Rough estimates suggest that approximately 16.1% of published papers may have used problematic cell lines, while the International Cell Line Authentication Committee (ICLAC) lists 576 misidentified or cross-contaminated cell lines in its latest register [5]. The consequences extend beyond wasted resources to include false conclusions, retracted publications, and compromised therapeutic development.
Good Cell Culture Practice (GCCP) establishes a framework for maintaining the authenticity, purity, and biological characteristics of cell lines throughout their use in research [5]. When cell-based research progresses toward therapeutic application, Good Manufacturing Practice (GMP) provides the quality management system necessary to ensure the safety, quality, and efficacy of manufactured products [98] [99]. Together with other quality frameworks like Good Laboratory Practice (GLP) and Good Clinical Practice (GCP), these standards form a comprehensive continuum of quality assurance from basic research to clinical application [98] [99]. This technical guide examines the intersection of these regulatory frameworks with a specific focus on preventing, detecting, and managing cross-contamination in cell line research and development.
Defining Cross-Contamination in Cell Culture Systems
In cell culture laboratories, cross-contamination manifests in two primary forms, each with distinct origins and consequences:
Inter- and Intra-species Cellular Cross-Contamination: This occurs when one cell line is replaced by or mixed with another, typically through laboratory errors such as using shared reagents, inadequate technique, or mislabeling [5] [43]. The most infamous example is HeLa cell contamination, which has compromised numerous cell lines over decades of research.
Microbiological Contamination: This involves the introduction of microorganisms including bacteria, fungi, yeast, mycoplasma, or viruses into cell cultures [5] [71]. The physiological temperature, humidity, and nutrient-rich environment of cell culture systems provide ideal conditions for microbial growth [71].
Mechanisms and Pathways of Contamination
The transfer of contaminants follows predictable pathways that can be modeled and quantified. Laboratory studies of bacterial transfer provide a framework for understanding these mechanisms, where the transfer fraction is calculated as:
Transfer Fraction = Number of CFU on Recipient / Number of CFU on Source [100]
This quantitative approach enables risk assessment and modeling of contamination spread. In practical cell culture settings, primary contamination routes include:
- Direct transfer via contaminated pipettes, shared media, or improperly sterilized equipment
- Aerosol generation during vigorous pipetting or bottle opening
- Surface-mediated transfer through contaminated work surfaces, water baths, or incubators [71]
- Procedural errors such as working with multiple cell lines simultaneously without adequate containment
The Regulatory Framework Continuum: GCP, GLP, GMP, and GCCP
Quality guidelines establish specific requirements across the drug development lifecycle, each with distinct focus areas and compliance objectives relevant to preventing cross-contamination.
Table 1: Comparison of Regulatory Frameworks in Pharmaceutical Development
| Framework | Scope and Focus | Regulatory Stage | Primary Quality Concerns | Documentation Requirements |
|---|---|---|---|---|
| GCCP | Basic and translational cell culture research; authentication, contamination prevention | Preclinical research phase | Cellular misidentification, microbial contamination, genetic drift | Cell line authentication records, contamination testing protocols, passage number documentation |
| GLP | Non-clinical laboratory studies for safety and efficacy | Preclinical testing phase | Study reliability, data traceability, protocol adherence | Study plans, raw data, SOPs, quality assurance reports |
| GMP | Manufacturing of products for human use | Production and quality control | Product quality, consistency, contamination control, process validation | Batch records, quality control testing, deviation investigations |
| GCP | Clinical trials involving human subjects | Clinical research phase | Human subject protection, data integrity, ethical conduct | Protocol amendments, informed consent, case report forms |
Good Cell Culture Practice (GCCP)
GCCP guidelines provide fundamental principles for maintaining cell line authenticity and preventing contamination through several key strategies:
- Cell Line Authentication: Regular testing using methods such as short tandem repeat (STR) profiling to verify cell line identity [43]
- Mycoplasma Testing Routine: Establishing scheduled testing intervals using PCR or ELISA-based methods to detect this common and often invisible contaminant [71]
- Aseptic Technique: Maintaining strict sterile workflows including surface disinfection, regulated access to cell culture areas, and proper personal protective equipment [71]
- Quarantine Procedures: Isolating newly acquired cell lines until quality control confirms their authenticity and sterility [71]
Good Laboratory Practice (GLP)
GLP governs non-clinical laboratory studies, focusing on data reliability and study integrity through:
- Study Planning and Protocol: Requiring pre-approved protocols that clearly define objectives, methodologies, and data collection procedures [99] [101]
- Quality Assurance Units: Mandating dedicated QA personnel responsible for monitoring study progress and ensuring SOP compliance [99]
- Data Traceability: Ensuring all generated data is verifiable and reproducible through comprehensive documentation [99]
- Facility and Equipment Standards: Maintaining appropriate laboratory environments with calibrated equipment and validated processes [99]
Good Manufacturing Practice (GMP)
GMP ensures that therapeutic products are consistently produced and controlled according to quality standards, with specific relevance to cell-based products:
- Quality Management System: Implementing a robust QMS that defines procedures for every manufacturing aspect [99]
- Process Validation: Requiring manufacturing processes to be validated to consistently produce products meeting quality attributes [99]
- Facility and Equipment Controls: Maintaining stringent standards for cleanliness, maintenance, and prevention of cross-contamination [98] [99]
- Quality Control Testing: Testing raw materials, in-process materials, and finished products to ensure specification compliance [99]
The relationship between these frameworks across the product development lifecycle can be visualized as a continuous quality continuum:
Diagram 1: Quality Framework Continuum in Biopharmaceutical Development
Experimental Protocols for Detection and Prevention
Cell Line Authentication Methodologies
Short Tandem Repeat (STR) Profiling Protocol
STR profiling has emerged as the international reference standard for human cell line authentication due to its high discrimination power and reproducibility [43].
Table 2: Comparison of Cell Line Authentication Methods
| Method | Principle | Discrimination Power | Time Requirement | Key Applications |
|---|---|---|---|---|
| STR Profiling | PCR amplification of highly polymorphic microsatellite regions | High for human cell lines | 1-2 days | Routine authentication of human cell lines |
| Isoenzyme Analysis | Electrophoretic separation of isoenzymes with species-specific mobility | Limited to inter-species discrimination | 1 day | Initial screening for interspecies contamination |
| DNA Barcoding | Sequencing of cytochrome c oxidase subunit I (COI) gene | Moderate for inter-species | 2-3 days | Identification of species origin |
| Karyotyping | Chromosomal analysis for number and structure | Low to moderate | 1-2 weeks | Detection of genetic instability |
Procedure:
- DNA Extraction: Isolate high-quality genomic DNA from cell pellets using silica-membrane technology
- PCR Amplification: Amplify 8-16 STR loci using commercially available kits
- Capillary Electrophoresis: Separate amplified fragments and detect fluorescence
- Data Analysis: Compare resulting profile with reference databases
- Interpretation: Match profiles with reference cell lines; ≥80% match score generally indicates authenticity
Quality Controls:
- Include positive control DNA with known profile
- Monitor signal strength and heterozygote balance
- Establish minimum data quality thresholds
- Document all procedures and results for audit trails
Mycoplasma Detection Protocols
PCR-Based Detection Method
Mycoplasma contamination affects an estimated 15-35% of cell cultures and can significantly alter cell behavior without visible culture changes [5] [71].
Procedure:
- Sample Collection: Collect supernatant from test cultures after 3 days without antibiotics
- DNA Extraction: Use commercial kits optimized for mycoplasma DNA recovery
- Primer Design: Select primers targeting 16S rRNA genes conserved across Mycoplasmatales
- PCR Amplification: Include positive (mycoplasma DNA) and negative (water) controls
- Gel Electrophoresis: Visualize amplification products; positive samples show characteristic bands
Alternative Methods:
- Microbiological Culture: Gold standard but requires 4-5 weeks for results
- Fluorochrome Staining: Uses DNA-binding dyes like Hoechst 33258
- ELISA-Based Tests: Commercial kits for specific mycoplasma species
- RNA Hybridization: Detects mycoplasma rRNA with specific probes
The comprehensive workflow for preventing and detecting cross-contamination integrates multiple quality checkpoints:
Diagram 2: Cell Line Quality Assurance Workflow
The Scientist's Toolkit: Essential Reagents and Materials
Implementing effective contamination control requires specific reagents and materials with defined functions in prevention and detection protocols.
Table 3: Essential Research Reagents for Cross-Contamination Prevention
| Reagent/Material | Function | Application Specifics | Quality Requirements |
|---|---|---|---|
| STR Profiling Kits | Multiplex PCR amplification of polymorphic loci | Cell line authentication | Validated for human or species-specific markers |
| Mycoplasma Detection Kits | PCR or ELISA-based detection | Routine screening for mycoplasma | Detection limit of ≤10 CFU/mL |
| Antibiotic-Antimycotic Solutions | Suppression of microbial growth | Culture media supplement | Validated for cell type, used judiciously |
| Cell Dissociation Reagents | Detachment of adherent cells | Cell passaging | Minimal proteolytic activity to preserve surface markers |
| Sterilization Indicators | Verification of sterilization efficacy | Autoclave validation | Color-changing chemical indicators |
| Surface Disinfectants | Laboratory surface decontamination | Work area cleaning | 70% ethanol, isopropanol, or validated alternatives |
| Personal Protective Equipment | Personnel-based contamination barrier | Aseptic technique | Lab coats, gloves, face protection |
Strategic Implementation of Prevention Measures
Facility Design and Process Controls
Effective contamination prevention requires integrated strategies addressing facility, process, and personnel factors:
- Physical Separation: Establish dedicated areas for different cell lines and procedures, particularly isolating quarantined cultures [71]
- Unidirectional Workflow: Design workflows that move from clean to potentially contaminated areas without backtracking
- Environmental Monitoring: Implement regular monitoring of air quality, water baths, and incubator environments [71]
- Single-Use Policy: Where possible, use single-use materials to prevent carryover contamination
- Liquid Handling Controls: Use filtered pipette tips and avoid shared media bottles
Quality Management Systems
A robust quality system forms the foundation for contamination prevention:
- Standard Operating Procedures (SOPs): Develop and maintain detailed SOPs for all critical processes including cell culture, authentication, and contamination testing [98] [99]
- Documentation Practices: Implement comprehensive documentation systems with complete traceability of cell line history [99]
- Training Programs: Ensure all personnel receive regular training in aseptic techniques and contamination prevention [99] [71]
- Audit Schedules: Conduct regular internal and external audits to verify compliance with established procedures [98]
The integration of GCCP, GLP, and GMP standards creates a defensible framework for preventing cross-contamination throughout the research and development continuum. In an era where an estimated 20% of cell lines may be misidentified, proactive implementation of authentication protocols, rigorous aseptic technique, and comprehensive quality systems is not merely regulatory compliance but fundamental scientific responsibility [43]. The strategic application of these standards, supported by the experimental protocols and detection methodologies detailed in this guide, provides researchers with the tools necessary to ensure the integrity of cell-based research and the safety of resulting therapeutics. As cell line technologies continue to evolve toward more complex applications including regenerative medicine and personalized therapeutics, the principles outlined here will form the critical foundation for scientific validity and public trust.
The Role of Journals and Funding Agencies in Enforcing Authentication
Cell lines serve as essential experimental models in biomedical research and drug development, but their scientific utility is critically compromised by widespread cross-contamination and misidentification. Cross-contamination occurs when a fast-growing cell line overtakes another culture, while misidentification involves incorrectly labeling or handling cell lines. These issues lead to experimental data that are unreliable and irreproducible, creating a ripple effect of wasted resources, misleading follow-up studies, and compromised evidence-based conclusions [102]. The International Cell Line Authentication Committee (ICLAC) registry documents nearly 600 misidentified or contaminated cell lines, with HeLa being one of the most common contaminants due to its prolific growth capacity [102] [4]. Despite long-standing awareness of this problem, numerous studies—possibly numbering in the tens of thousands—have used lines that are either contaminated with other cells or mislabeled, threatening the very foundation of biomedical research validity [102].
The Scope and Impact of Cell Line Misidentification
Quantitative Assessment of the Problem
The scale of cell line misidentification is extensive, with significant implications for research integrity. The table below summarizes key statistics that highlight the magnitude of this ongoing issue:
Table 1: Quantitative Impact of Cell Line Misidentification
| Metric | Statistical Value | Source/Reference |
|---|---|---|
| Misidentified cell lines in ICLAC registry | 593 lines | ICLAC Register (v13, Apr 2024) [102] |
| Estimated studies using misidentified cells | 32,755 studies | Research Integrity & Peer Review (2025) [102] |
| Subsequent citations of problematic studies | ~500,000 citations | Research Integrity & Peer Review (2025) [102] |
| Misidentification rate among all cell lines | 8.6% | Research Integrity & Peer Review (2025) [102] |
| Manuscript rejection rate due to cell line issues | ~4% of manuscripts | International Journal of Cancer [49] |
| Common contaminant (HeLa) in liver cell lines | 21 listed liver lines | ICLAC Register [4] |
Consequences of Undetected Cross-Contamination
The use of misidentified cell lines generates scientifically invalid data that undermines research conclusions. For instance, several studies have attributed liver-specific mechanisms or drug responses to cell lines subsequently identified as being contaminated with HeLa cervical cancer cells [102]. In one documented case, researchers incorrectly concluded that a compound derived from Anemonoides raddeana exerted therapeutic effects on hepatocellular carcinoma because they used QGY-7703 cells, which are actually HeLa-contaminated [102]. Similarly, other studies have drawn invalid conclusions about gastric cancer and normal liver cells using contaminated lines such as BGC-823, BEL-7402, and L-02 [102]. These errors potentially misdirect future research and drug development efforts, ultimately delaying therapeutic advances for patients.
Authentication Methodologies: Technical Standards and Protocols
Short Tandem Repeat (STR) Profiling: The Gold Standard
Short tandem repeat profiling stands as the internationally recognized gold standard for cell line authentication, particularly for human cell lines [41]. This method compares small sections of DNA occurring at specific locations in the genome to verify genetic content and identity [49]. STR profiling's precision in identifying genetic variation makes it particularly valuable for detecting cross-contamination and misidentification [39].
The American Type Culture Collection Standards Development Organization Workgroup initially recommended eight STR markers for human cell line authentication, later expanding to 13 STRs to improve accuracy [39]. However, forensic-grade STR kits now target more markers, with systems available for 23-24 STR loci including sex-determining markers [39] [49]. These expanded panels offer superior discrimination power by lowering the Probability of Identity (POI), making it significantly less likely for different cell lines to share the same STR profile [49].
Table 2: Standard STR Markers for Cell Line Authentication
| STR Loci | ANSI/ATCC ASN-0002-2022 (13+1) | Other Providers (15+1) | Expanded Panels (21+3) |
|---|---|---|---|
| D8S1179 | ● | ● | ⬤ |
| D21S11 | ● | ● | ⬤ |
| D7S820 | ● | ● | ⬤ |
| CSF1PO | ● | ● | ⬤ |
| D3S1358 | ● | ● | ⬤ |
| TH01 | ● | ● | ⬤ |
| D13S317 | ● | ● | ⬤ |
| D16S539 | ● | ● | ⬤ |
| vWA | ● | ● | ⬤ |
| TPOX | ● | ● | ⬤ |
| D18S51 | ● | ● | ⬤ |
| D5S818 | ● | ● | ⬤ |
| FGA | ● | ● | ⬤ |
| Amelogenin | ● | ● | ⬤ |
| D2S1338 | ● | ⬤ | |
| D19S433 | ● | ⬤ | |
| D10S1248 | ⬤ | ||
| D1S1656 | ⬤ | ||
| D12S391 | ⬤ | ||
| SE33 | ⬤ | ||
| Y-indel | ⬤ |
Experimental Protocol for STR-Based Authentication
A standardized STR profiling protocol involves multiple critical steps to ensure accurate and reproducible results [39] [49]:
Sample Preparation and DNA Extraction: Cell lines are cultured following standard conditions. Genomic DNA is extracted from approximately 5 × 10^6 cells using commercial kits (e.g., QIAamp DNA Blood Mini Kit). DNA quantification is performed using fluorometric methods (e.g., Qubit fluorometer), and samples are stored at -80°C until use.
STR Multiplex PCR: Multiple target DNA regions are amplified simultaneously in a single PCR reaction. The SiFaSTR 23-plex system or GlobalFiler kit targeting 24 STR loci can be used according to manufacturers' protocols. These systems typically include 21-24 autosomal STRs and 2-3 sex-related polymorphisms (Amelogenin and Y indel).
Capillary Electrophoresis: PCR products are separated by size using capillary electrophoresis systems (e.g., ABI 3730xl DNA Analyzer or Classic 116 Genetic Analyzer). DNA genotyping is performed using specialized software (e.g., GeneMapper or GeneManager) to determine allele sizes for each STR locus.
Data Analysis and Interpretation: STR profiles are analyzed using established algorithms such as the Tanabe and Masters algorithms for authentication:
- Tanabe Algorithm: Percent match = (2 × number of shared alleles) / (total alleles in query profile + total alleles in reference profile) × 100%
- Masters Algorithm: Percent match = (number of shared alleles) / (total number of alleles in query profile) × 100%
According to the Tanabe algorithm, similarity scores ≥90% indicate relatedness, while the Masters algorithm uses a slightly more lenient ≥80% threshold [39]. The alteration status of STR loci is classified as stable (S), loss of heterozygosity (L), occurrence of an additional allele (Aadd), or occurrence of a new allele (Anew) [39].
Database Comparison: The obtained STR results are compared against reference databases using online STR similarity search tools such as CLASTR (Cell Line Authentication using STR, version 1.4.4) to identify correct reference cell lines and detect potential misidentification.
Figure 1: STR Profiling Workflow for Cell Line Authentication
Advanced and Emerging Authentication Technologies
While STR profiling remains the gold standard, other methods are available for specific applications:
- SNP-based authentication: Useful for authenticating consanguineous cell lines with close genetic similarities. Tools like CCLHunter utilize single nucleotide polymorphisms, expression profiles, and kindred topology to authenticate cancer cell lines from RNA-seq data with reported accuracy rates of 93.27% [103].
- Morphological verification: Microscopic examination to confirm expected cellular morphology.
- Karyotyping and cytogenetic analysis: Chromosomal analysis to identify species origin and major genetic abnormalities.
- Isoenzyme analysis: Electrophoretic methods to determine species-specific enzyme patterns.
- Mycoplasma testing: Essential for detecting this common contamination that affects cell behavior [41].
Journal Authentication Policies and Enforcement Mechanisms
Policy Requirements Across Major Publishers
Scientific journals have implemented increasingly stringent authentication requirements to combat misidentification. The table below summarizes authentication mandates from major publishers:
Table 3: Journal Cell Line Authentication Requirements
| Journal/Publisher | Authentication Requirement | Documentation Required |
|---|---|---|
| American Association for Cancer Research (AACR) | Required for all cell lines | Source, testing method, date of last authentication [104] |
| Nature Publishing Group | Strongly recommended, certificates encouraged | Statement on source, authentication method, mycoplasma testing [104] |
| BioMed Central Journals | Strongly encouraged for human cell lines | Source, authentication method, mycoplasma status [104] |
| International Journal of Cancer | Required for established human tumor cell lines | DNA (STR) profiling recommended [104] |
| Society for Endocrinology | Required for all cell lines used | Authentication of correct origin [104] |
| PLOS ONE | Recommended, may be required during review | Check against ICLAC misidentified cell lines [104] |
| Journal of Cell Communication and Signaling | Required with comprehensive details | Species, sex, tissue origin, RRID, source, STR method [41] |
Documentation and Reporting Standards
Journals typically require authors to include specific authentication information in the Materials and Methods section of manuscripts:
- The source of the cell line and when it was obtained
- Whether the cell line has been tested and authenticated
- The method used for authentication (e.g., STR profiling)
- When the cells were last tested
- Mycoplasma contamination testing status [104]
Additionally, many journals now recommend or require Research Resource Identifiers (RRIDs) for immortalized cell lines to enable consistent tracking throughout the scientific literature [41]. The International Cell Line Authentication Committee (ICLAC) provides continuously updated resources on misidentified cell lines that researchers are expected to consult prior to submission [41].
Editorial Responses to Misidentification
Journal responses to identified misidentification vary significantly. A 2025 analysis of four cases involving misidentified cell lines revealed:
- In two cases, editors promptly published comments, resulting in transparent corrections
- In one case, the editor conducted an internal investigation without immediate public correction
- In one case, the journal declined to address concerns publicly [102]
This variability highlights the lack of universal standards in addressing misidentification despite growing recognition of the problem.
Funding Agency Mandates and Compliance Requirements
NIH Authentication Policies
The National Institutes of Health has implemented rigorous authentication requirements for funded research:
- The June 2015 Notice "NOT-OD-15-103: Enhancing Reproducibility through Rigor and Transparency" requires grant applicants to describe methods for authenticating key biological resources, including cell lines [104].
- For grants submitted since January 25, 2016, NIH expects that "key biological and/or chemical resources will be regularly authenticated to ensure their identity and validity for use in the proposed studies" [104].
- The NIH Genomic Data Sharing Policy requires investigators using new collections of biospecimens and/or cell lines in generating large-scale genomic data to obtain informed consent and implement appropriate authentication procedures [105].
Compliance Framework and Implementation
Funding agency mandates have created a compliance framework that reinforces journal requirements:
- Authentication plans must be included in grant applications with specific methodological details
- Regular authentication at critical points in research (e.g., every 10 passages, before freezing stocks, when beginning new studies) is expected [49]
- Documentation of authentication results must be maintained and available for review
- Failure to comply with authentication requirements can result in funding restrictions or retraction of published work
Figure 2: Authentication Enforcement Ecosystem
The Scientist's Toolkit: Essential Research Reagent Solutions
Table 4: Essential Resources for Cell Line Authentication
| Resource Type | Specific Examples | Function/Purpose |
|---|---|---|
| STR Profiling Kits | GlobalFiler (24-plex), SiFaSTR (23-plex) | Simultaneous amplification of multiple STR loci for identification [39] [49] |
| Reference Databases | ICLAC Register of Misidentified Cell Lines, Cellosaurus, CLASTR | Identify known problematic lines; compare STR profiles [102] [41] |
| Analysis Tools | CCLHunter, GeneMapper, Tanabe & Masters algorithms | Authenticate cell lines; calculate matching percentages [39] [103] |
| Quality Control Kits | Mycoplasma detection kits (PCR, bioluminescence) | Detect microbial contamination that compromises experiments [41] |
| Documentation Systems | Research Resource Identifiers (RRIDs) | Consistent tracking of cell lines across publications [41] |
The enforcement of cell line authentication by journals and funding agencies represents a critical evolution in research standards aimed at preserving scientific integrity. While technical methods like STR profiling provide robust authentication tools, their effectiveness depends on consistent implementation supported by policy mandates. The growing alignment between journal requirements and funding agency mandates creates a reinforcing ecosystem that promotes authentication as a fundamental research practice rather than an optional add-on. As research becomes increasingly complex and collaborative, rigorous cell line authentication provides the foundation upon which reproducible, translatable scientific discoveries are built. Widespread adoption of these standards across the research community represents the most promising path toward eliminating the persistent problem of misidentification and restoring full confidence in cell-based research outcomes.
Cell line cross-contamination and misidentification represent a persistent and critical challenge in biomedical research, undermining the validity and reproducibility of countless studies. This phenomenon occurs when a cell culture is inadvertently replaced by or mixed with a different, often more aggressive, cell line. Despite being a known issue for decades, misidentification remains widespread, creating a ripple effect of wasted resources, misleading follow-up studies, and compromised evidence-based conclusions [4] [26]. The International Cell Line Authentication Committee (ICLAC) registry vividly illustrates the scale of this problem, listing 593 misidentified or cross-contaminated cell lines as of April 2024 [4]. The problem is particularly acute with rapidly growing lines like HeLa (derived from human cervical carcinoma cells), which have contaminated numerous cell lines worldwide. This case study analyzes the impact of such misidentifications on the scientific literature, examines the root causes, and outlines established and emerging protocols to safeguard research integrity.
Table 1: Quantifying the Misidentification Problem in Cell Research
| Aspect of the Problem | Quantitative Measure | Source/Context |
|---|---|---|
| ICLAC Listed Misidentified Lines | 593 cell lines | ICLAC Registry Version 13 (April 2024) [4] |
| Incidence in a Study of 278 Cell Lines | 46.0% (128/278) | Survey of cell lines from 28 institutes in China [21] |
| Misidentification of Cell Lines Established in China | 73.2% (52/71) | Same survey, highlighting a specific vulnerability [21] |
| HeLa Cell Contamination | 46.9% (60/128) of misidentified cases | The most common contaminant identified [21] |
| Estimated Problematic Publications | ~16.1% of papers | Rough estimate of papers using problematic cell lines [5] |
Analysis of Published Case Studies
The use of misidentified cell lines has directly led to publications with invalid data and unsupported conclusions. The following cases, drawn from recent literature on liver research, exemplify this critical issue.
Case Study 1: The Pervasive HeLa Contamination
A comprehensive investigation into 278 widely used tumor cell lines uncovered that 46% were cross-contaminated or misidentified [21]. Among cell lines established within China, the misidentification rate soared to 73.2%. A significant portion of these misidentified lines (40.6%) were originally established by Chinese researchers. Strikingly, HeLa cells accounted for 46.9% of all cross-contamination incidents, affecting 31 different cell lines purported to be of other tissue origins [21]. This includes so-called "liver" lines such as QGY-7703, BEL-7402, L-02, and WRL 68, all of which are listed in the ICLAC register as being HeLa contaminants [4]. Research papers using these lines to investigate liver-specific biology or drug responses are, in reality, studying cervical cancer cells, fundamentally invalidating their conclusions related to hepatic mechanisms.
Case Study 2: The Challenge of Subtle Misidentification
Not all misidentification is as straightforward as HeLa contamination. The study by Huang et al. also revealed more complex scenarios. For instance, the bile duct cancer cell line HCCC-9810 and the lung cancer cell line Calu-6 showed an 88.9% match when compared using a standard 9-loci STR profile, suggesting a common origin [21]. However, when a more precise 21-loci STR analysis was applied, the match percentage dropped to 48.2%. Subsequent Single Nucleotide Polymorphism (SNP) profiling confirmed that HCCC-9810 and Calu-6 are indeed distinct cell lines [21]. This case highlights the critical importance of using highly discriminatory authentication methods and curated databases to avoid false conclusions about cell line identity, demonstrating that less rigorous protocols can fail to distinguish between different cell types.
Impact on the Scientific Record and Varied Editorial Responses
The propagation of erroneous data has a lasting, detrimental impact. A literature search for just five misidentified liver cell lines (QGY-7703, BGC-823, BEL-7402, L-02, and WRL-68) identified nearly 6,000 publications that relied on these problematic models [4]. When such errors are discovered, the responsibility for correction often falls to journal editors, but their responses are inconsistent. A 2025 study reported four distinct editorial outcomes after notifying journals of papers based on misidentified cells: 1) two journals quickly published comments, enabling transparent correction; 2) one editor conducted an internal investigation without an immediate public correction; and 3) one journal declined to address the concerns publicly [4]. This inconsistency creates a fragmented scientific record and allows misleading information to remain in circulation.
Experimental Protocols for Cell Line Authentication
Preventing the publication of invalid data requires rigorous, routine authentication of cell lines. Several well-established methodologies can reliably verify cell identity.
Short Tandem Repeat (STR) Profiling
STR profiling is the international gold standard for authenticating human cell lines [21] [106]. This method analyzes the length polymorphisms in microsatellite regions scattered throughout the genome.
Protocol Workflow:
- DNA Extraction: Isolate high-quality genomic DNA from the cell line under investigation.
- PCR Amplification: Amplify multiple STR loci using fluorescently-labeled primers. Modern kits analyze 21 or more loci for high discrimination.
- Capillary Electrophoresis: Separate the amplified fragments by size to create a unique DNA profile.
- Data Analysis and Comparison: Compare the resulting STR profile against reference databases from international cell banks (e.g., ATCC, DSMZ) or the Cellosaurus database. A match score of ≥80% is typically considered a pass [21].
Key Considerations: The number of loci analyzed is critical. Using too few loci (e.g., 9) can fail to distinguish between similar but distinct lines, as seen in the HCCC-9810/Calu-6 case [21]. Authentication should be performed when creating new cell banks, before freezing stocks, and prior to publishing research findings [106].
Isoenzyme Analysis and Karyotyping
These traditional methods provide supplementary data but are less definitive than STR profiling.
- Isoenzyme Analysis: This technique examines the electrophoretic mobility of metabolic enzymes (e.g., glucose-6-phosphate dehydrogenase), which can be species-specific. It is a quick method to check for interspecies contamination but lacks the discriminatory power for intra-species authentication [106].
- Karyotyping: This involves staining and visualizing the chromosomes of a cell under a microscope. It can reveal gross chromosomal abnormalities and aneuploidy common in continuous cell lines. While useful for identifying major mismatches, it cannot distinguish between many closely related human cell lines [106].
Emerging and Supporting Methodologies
- SNP Profiling: Interrogates single nucleotide polymorphisms across the genome. It is highly discriminatory and can resolve ambiguities that STR profiling may not, as demonstrated in the HCCC-9810/Calu-6 case [21].
- Gene Expression Profiling: RNA sequencing or microarray analysis can confirm that a cell line expresses the expected tissue-specific markers, providing functional validation of its identity.
Table 2: Cell Line Authentication Methods
| Method | Principle | Application | Discriminatory Power |
|---|---|---|---|
| STR Profiling | DNA length polymorphism at microsatellite loci | Primary method for human cell line authentication; gold standard | High |
| SNP Profiling | Single nucleotide polymorphism across the genome | Resolving complex cases; supplementary authentication | Very High |
| Isoenzyme Analysis | Electrophoretic mobility of metabolic enzymes | Rapid check for interspecies contamination | Low |
| Karyotyping | Microscopic analysis of chromosome number and structure | Detecting gross chromosomal changes and major mismatches | Moderate |
| Gene Expression Profiling | Analysis of tissue-specific RNA transcripts | Functional validation of cell type identity | High |
The Scientist's Toolkit: Essential Research Reagent Solutions
Implementing a robust authentication strategy requires specific reagents and resources. The following tools are essential for maintaining cell line integrity.
Table 3: Key Research Reagent Solutions for Cell Line Authentication
| Reagent / Resource | Function and Importance |
|---|---|
| STR Profiling Kits | Commercial kits containing primers for multiplex PCR amplification of core STR loci. Essential for generating a standardized DNA fingerprint for comparison. |
| Authenticated Reference Cell Lines | Cell lines obtained from reputable cell banks (e.g., ATCC, ECACC) with a verified STR profile. These serve as essential positive controls for authentication assays. |
| Cell Line Databases (e.g., Cellosaurus, ICLAC) | Curated public databases listing STR profiles of known cell lines and registers of known misidentified lines. Critical for comparing and verifying results. |
| Mycoplasma Detection Kits | Kits to test for mycoplasma contamination, which can alter cell behavior and compromise research integrity. Testing should be performed alongside authentication [5]. |
| Cell Dissociation Reagents (e.g., Accutase) | Mild enzymatic or non-enzymatic reagents for detaching adherent cells without degrading surface proteins, which is important for subsequent analyses like flow cytometry [5]. |
Visualizing the Authentication and Contamination Workflow
The following diagram illustrates the pathways leading to cell line misidentification and the essential workflow for authentication and prevention, incorporating the mandatory color palette.
Diagram 1: Pathways of cell line misidentification and authentication.
The case studies presented herein underscore a clear and present danger to biomedical research. The persistence of publications using misidentified cell lines like HeLa-contaminated "liver" models reveals systemic vulnerabilities in the research workflow. To combat this, a collaborative, multi-stakeholder approach is essential. The following best practices, derived from the International Society for Stem Cell Research (ISSCR) and other expert bodies, should be adopted to uphold scientific integrity [107] [5] [106]:
- Mandatory Authentication: Researchers must perform cell line authentication using STR profiling at key points: upon receiving a new line, before creating working banks, before initiating critical experiments, and prior to manuscript submission.
- Sourcing from Reputable Providers: Cell lines should be procured from recognized cell banks that provide Certificates of Analysis and authenticated STR profiles.
- Rigorous Peer Review: Journal reviewers and editors must mandate evidence of cell line authentication as a condition for publication. They should utilize resources like the ICLAC registry and Cellosaurus to screen for known problematic lines.
- Education and Training: Institutions must train scientists in Good Cell Culture Practice (GCCP), emphasizing the causes and consequences of cross-contamination and the importance of routine authentication.
- Data Transparency: Authors should explicitly state the source and authentication status of all cell lines used in their methods sections, including the specific technique and database used for verification.
Adherence to these principles is not merely a technical formality but a fundamental ethical obligation to ensure that scientific progress is built upon a foundation of reliable and reproducible data.
Cell line authentication serves as a critical safeguard in biomedical science, yet its implementation varies dramatically between research and Good Manufacturing Practice (GMP) environments. Within the broader context of cross-contamination in cell line research, authentication provides the foundational assurance of cell line identity and purity. Cross-contamination, where unintended cell lines infiltrate a culture, persists as a widespread problem affecting an estimated 15-20% of published papers and compromising data integrity [108] [67]. The International Cell Line Authentication Committee (ICLAC) currently lists 576 misidentified or cross-contaminated cell lines in its register, highlighting the scale of this issue [5].
This technical guide examines how authentication practices diverge between research use only (RUO) and GMP manufacturing contexts, exploring the distinct drivers, methodologies, and consequences in each setting. Where RUO environments prioritize data integrity and reproducibility, GMP frameworks enforce rigorous authentication as part of a comprehensive quality system designed to ensure patient safety and regulatory compliance [109] [1]. Understanding these distinctions is essential for researchers, scientists, and drug development professionals navigating the transition from basic research to clinical application.
Understanding the Contexts: RUO vs. GMP
Research Use Only (RUO) Framework
RUO products are specifically designed for laboratory research and are not intended for human clinical applications [109]. In this context, authentication focuses primarily on ensuring data integrity and reproducibility. The driving concern is preventing false conclusions and wasted resources, with studies suggesting that approximately 16.1% of published papers may have used problematic cell lines [5]. RUO environments offer greater flexibility and cost-effectiveness but operate with fewer regulatory requirements, placing greater responsibility on individual researchers to implement appropriate authentication practices [109].
Good Manufacturing Practice (GMP) Framework
GMP manufacturing refers to the production of products that must adhere to strict regulatory standards for human use [109]. The World Health Organization defines GMP as the aspect of quality assurance that ensures medicinal products are "consistently produced and controlled to the quality standards appropriate to their intended use" [110]. Unlike RUO, GMP encompasses a comprehensive quality management system with legal components covering distribution, contract manufacturing, testing, and responses to defects [110]. The primary driver is patient safety, with authentication serving as a critical control point within a validated system that ensures traceability and compliance with regulatory requirements from agencies like the FDA and EMA [111] [112].
The Problem of Cross-Contamination
Cross-contamination occurs when unintended cell lines infiltrate a culture, leading to misidentification and potentially invalid experimental outcomes [1]. In shared research environments, the risk is particularly high due to improper labelling, inadequate cleaning procedures, or unintentional mixing of cultures [1]. Highly proliferative cell lines, such as HeLa or HEK293, can overgrow slower-growing populations, fundamentally altering study results [108]. The problem has persisted for decades, with observations of cross-contamination dating back to the early days of cell culture following the establishment of the HeLa cell line [108].
The consequences of undetected cross-contamination include:
- Scientific Misinterpretation: Contaminated cell lines can produce false-positive or false-negative findings, skewing scientific conclusions [1].
- Wasted Resources: Millions of dollars in research funding and countless hours of effort are wasted on studies using misidentified cells [67].
- Compromised Literature: Contaminated findings enter the scientific literature, creating a legacy of invalid research that can mislead future studies [5].
- Therapeutic Risk: In GMP contexts, undetected cross-contamination can compromise product safety and efficacy, potentially endangering patients [1].
Table 1: Documented Impact of Cell Line Misidentification
| Impact Area | Research Context | GMP Manufacturing Context |
|---|---|---|
| Primary Concern | Data integrity and reproducibility [1] | Patient safety and regulatory compliance [1] [112] |
| Financial Consequences | Wasted research funds and resources [67] | Batch failures, costly production delays [1] |
| Scientific Consequences | False publications, compromised literature [5] | Inability to demonstrate product consistency and safety [112] |
| Estimated Prevalence | 15-20% of cell lines misidentified [108] [67] | Strict controls minimize risk when properly implemented [1] |
Authentication Methods and Techniques
Core Authentication Technologies
Multiple complementary methods exist for authenticating cell lines, each with distinct advantages and applications:
Short Tandem Repeat (STR) Profiling
STR profiling has emerged as the gold standard for human cell line authentication, particularly following the ANSI/ATCC ASN-0002-2011 consensus guidelines [67]. This technique analyzes repetitive sequence elements 2-7 base pairs long located throughout the human genome [67]. The updated ASN-0002 Revised 2022 recommends profiling 13 autosomal STR loci: CSF1PO, D3S1358, D5S818, D7S820, D8S1179, D13S317, D16S539, D18S51, D21S11, FGA, TH01, TPOX and vWA [67]. STR works by amplifying these regions using PCR, separating the resulting amplicons via capillary electrophoresis, and comparing the profile to reference databases [66] [67]. A match threshold of 80% is typically used to account for expected genetic drift in cultured cells [67].
Morphological Analysis
Morphological analysis involves examining the physical characteristics of cells under a microscope, assessing cell shape, size, and growth patterns [72]. This method provides a quick, accessible means of monitoring cell health and identifying obvious contamination but is insufficient alone due to the potential for similar appearance among different cell lines [72]. Morphology can vary with plating density, culture conditions, and differentiation state, making it most valuable as an initial screening tool when used alongside more definitive methods [66].
Karyotyping
Karyotyping involves analyzing the number and structure of chromosomes in a cell line [72] [108]. This traditional method provides insights into chromosomal abnormalities and variations, helping distinguish between cell lines with similar morphological characteristics but different chromosomal profiles [72]. It is particularly useful for identifying cell lines that have undergone genetic changes or mutations and is performed routinely by some cell repositories to determine genotype stability [108].
Isoenzyme Analysis
Isoenzyme analysis uses band patterns from the separation of proteins by electrophoresis to detect species-specific differences in the structure and mobility of individual enzyme isoforms [66] [108]. This technique is robust and returns rapid results but can be subject to low reproducibility [108]. It remains valuable for verifying species of origin and detecting interspecies contamination [66].
Proteomic Analysis
Proteomic analysis examines the protein expression profiles of cell lines using techniques like mass spectrometry to identify unique protein markers specific to certain cell lines [72]. This method complements genetic approaches by providing functional insights into cell behavior and can distinguish between cell lines with similar genetic backgrounds but different protein expressions [72].
Experimental Protocols
STR Profiling Protocol
Sample Preparation:
- Extract genomic DNA from cell pellets or use cells conserved on sample storage cards [67].
- Quantify DNA concentration and ensure sample integrity [67].
PCR Amplification:
- Use multiplex PCR to simultaneously amplify the recommended STR loci [66] [67].
- Systems like the GenePrint 24 System amplify all ANSI-0002 recommended loci [67].
- Typical reaction conditions: 5ng input DNA, amplification in less than 1.5 hours [67].
Capillary Electrophoresis:
- Separate amplified fragments using capillary electrophoresis systems [67].
- Instruments like the Spectrum Compact CE System provide automated analysis [67].
Data Analysis:
- Determine allele sizes using appropriate sizing software [66].
- Compare obtained profile to reference databases (ATCC, DSMZ, Cellosaurus) [67].
- Calculate percent match using established algorithms with 80% match threshold [67].
- Check for multiple alleles at multiple loci indicating cross-contamination [67].
Mycoplasma Detection Protocol
Hoechst Staining Method:
- Culture cells on sterile coverslips in appropriate medium [66].
- Fix cells with fresh Carnoy's fixative (methanol:glacial acetic acid, 3:1) [66].
- Stain with Hoechst 33258 fluorescent dye (50μg/mL in PBS) for 30 minutes [66].
- Examine under fluorescence microscopy at 500X magnification [66].
- Identify characteristic patterns of extracellular particulate or filamentous fluorescence indicating mycoplasma contamination [66].
Comparative Analysis: Authentication in Research vs. GMP
Methodological Approaches
While both research and GMP environments utilize similar core authentication technologies, their implementation differs significantly in rigor, documentation, and frequency.
Table 2: Authentication Method Comparison in Research vs. GMP Contexts
| Authentication Method | Research Application | GMP Application |
|---|---|---|
| STR Profiling | Recommended at key points (new lines, freezing, publication) [67] | Required for Master and Working Cell Banks with full validation [112] |
| Morphology Checks | Frequent visual monitoring by trained personnel [66] | Documented according to SOPs with defined acceptance criteria [1] |
| Karyotyping/Isoenzyme | Used for species verification and initial characterization [66] [108] | Part of comprehensive characterization package for regulatory submission [112] |
| Mycoplasma Testing | Periodic testing using PCR or fluorescence methods [66] [1] | Required for each cell bank lot with validated methods [1] [112] |
| Documentation | Laboratory notebooks and publication methods sections [66] | Comprehensive batch records within Quality Management System [112] |
Frequency and Triggers for Authentication
The timing and triggers for authentication differ substantially between research and GMP environments:
Research Context Authentication Triggers:
- When establishing or acquiring a new cell line [67]
- Within the first week of passaging a new cell culture [67]
- When starting a new series of experiments [67]
- When routinely passaging cell lines [67]
- When observing inconsistent cell behavior or unexpected results [67]
- When preparing to publish [67]
- When freezing cell stocks to verify purity [67]
GMP Context Authentication Triggers:
- During cell bank characterization (Master and Working Cell Banks) [112]
- As part of pre-defined testing schedule for cell banks [1]
- Following any deviation in manufacturing process [1]
- When investigating out-of-specification results [1]
- As required by regulatory submission documents [112]
Quality Systems and Documentation
The most significant differences between research and GMP authentication practices lie in their approach to quality systems and documentation:
Research Quality Practices:
- Follow Good Cell Culture Practice (GCCP) guidelines [5]
- Maintain accurate records of cell line sources and passage numbers [66]
- Implement regular cleaning and disinfection of shared equipment [108]
- Use proper labeling techniques suitable for low temperature storage [108]
- Establish written lab policies and training protocols [67]
GMP Quality Systems:
- Implement comprehensive Quality Management Systems (QMS) [112]
- Maintain detailed documentation including storage of information [112]
- Establish Standard Operating Procedures (SOPs) for all processes [1] [112]
- Validate all equipment, methods, and processes [112]
- Conduct regular audits and personnel training [112]
- Implement the Plan-Do-Check-Action (PDCA) cycle for continuous improvement [112]
Consequences of Failure
Research Context Consequences
In research settings, authentication failures primarily affect scientific integrity and resource utilization:
- Invalidated Data: Misidentified cell lines can lead to experimental results that are not reproducible, potentially invalidating publications [67].
- Wasted Resources: One study estimates that up to 20% of published papers could be invalid due to misidentified cell lines, representing enormous waste of research funding and effort [67].
- Publication Rejection: Many prominent journals now require cell line authentication prior to publication, with some manuscripts becoming unpublishable when authentication reveals use of the wrong cell line [108] [67].
- Compromised Scientific Legacy: Contaminated findings enter the scientific literature, creating false pathways that mislead future research [5].
GMP Context Consequences
In GMP manufacturing, authentication failures carry more severe implications:
- Batch Rejection: Failure to properly authenticate cell lines or control cross-contamination can lead to rejection of entire production batches [1].
- Regulatory Action: Non-compliance with GMP standards can result in regulatory actions including warning letters, consent decrees, or shutdown of manufacturing facilities [111] [1].
- Patient Safety Risks: Historically, insufficient processing and contamination control of biological products has led to serious patient harm, including the early polio vaccine that inadvertently gave children polio [112].
- Financial Impacts: Batch failures and regulatory actions result in significant financial losses, with costly production delays and remediation requirements [1].
Visualizing Authentication Workflows
Diagram 1: Authentication workflows for research versus GMP
The Scientist's Toolkit: Essential Reagents and Materials
Table 3: Key Reagent Solutions for Cell Line Authentication
| Reagent/Material | Function | Application Context |
|---|---|---|
| STR Profiling Kits (e.g., GenePrint 24 System) | Amplifies STR loci for DNA fingerprinting | Research and GMP human cell line authentication [67] |
| Capillary Electrophoresis System | Separates and analyzes amplified STR fragments | Research and GMP analysis of STR profiles [67] |
| Hoechst 33258 Stain | Fluorescent DNA binding dye for mycoplasma detection | Routine screening in research and GMP environments [66] |
| Cell Culture Storage Cards | Preserve cell samples for DNA analysis | Convenient sample storage for both contexts [67] |
| Validated Reference Standards | Provide controls for authentication assays | Primarily GMP for assay qualification/validation [112] |
| Mycoplasma Detection Kits | PCR-based detection of mycoplasma contamination | Essential for both research and GMP testing [1] |
Cell line authentication represents a critical defense against cross-contamination, but its implementation must be appropriately scaled to the context of use. Research environments focus on authentication as a means to ensure data integrity and reproducibility, typically employing STR profiling and morphological analysis at key points in the research lifecycle. In contrast, GMP manufacturing treats authentication as an integral component of a comprehensive quality system designed to ensure patient safety and regulatory compliance, with rigorous testing protocols, extensive documentation, and validation requirements.
The consequences of authentication failures escalate dramatically from research to GMP contexts. While research failures result in wasted resources and compromised publications, GMP failures can lead to batch rejection, regulatory action, and potentially patient harm. As research moves toward clinical application, understanding these distinctions becomes essential for successful translation. By implementing appropriate authentication practices from the outset, researchers and manufacturers can protect both scientific integrity and patient safety while advancing biomedical innovation.
Cell line misidentification and cross-contamination represent one of the most persistent and damaging problems in biomedical research. Cross-contamination occurs when an unintended cell line is introduced into a culture, eventually overgrowing and replacing the original cell line [1]. This issue has plagued cell biology since the earliest days of cell culture, with Stanley Gartler demonstrating as early as 1967 that 18 extensively used cell lines had all been taken over by HeLa cells [35]. Decades later, the problem remains alarmingly prevalent; an estimated 15-20% of cell lines used in experiments are misidentified or cross-contaminated [113], and the International Cell Line Authentication Committee (ICLAC) registry currently lists 593 misidentified or cross-contaminated cell lines [4].
The scientific and financial consequences are staggering. Misidentified cell lines compromise data integrity, lead to irreproducible results, and invalidate experimental conclusions. The cost extends beyond wasted reagents to encompass squandered staff time, delayed progress toward milestones, and potential damage to grant renewals and investor confidence [114]. One poignant example involves researchers who spent three years working on two supposedly related breast cancer cell lines, only to discover they were actually unrelated cell lines, leading to cancelled publication of a manuscript containing erroneous conclusions [113]. This review examines the growing movement toward universal authentication standards as an essential solution to this enduring problem.
The Scope and Impact of the Problem
Quantitative Assessment of Cell Line Misidentification
The scale of the cross-contamination problem is extensive, affecting numerous cell lines across different tissue types and species. The following table summarizes data from the ICLAC registry on commonly misidentified cell lines, highlighting the pervasive nature of HeLa cell contamination.
Table 1: Examples of Misidentified Cell Lines from the ICLAC Registry (Version 13, 2024) [4]
| Misidentified Cell Line | Claimed Tissue Type | Claimed Species | Contaminating Cell Line | Actual Tissue Type |
|---|---|---|---|---|
| BEL-7402 | Liver, hepatocellular carcinoma | Human | HeLa/HCT 8 | Cervical adenocarcinoma/colon carcinoma |
| L-02 | Liver, normal hepatic cells | Human | HeLa | Cervical adenocarcinoma |
| QGY-7703 | Liver, hepatocellular carcinoma | Human | HeLa | Cervical adenocarcinoma |
| WRL 68 | Liver, embryonic cells | Human | HeLa | Cervical adenocarcinoma |
| Chang liver | Liver, normal hepatic cells | Human | HeLa | Cervical adenocarcinoma |
| BGC-823 | Gastric carcinoma | Human | HeLa | Cervical adenocarcinoma |
The impact of using misidentified cell lines extends throughout the research ecosystem. A comprehensive literature search identified nearly 6,000 publications using just five misidentified liver cell lines (QGY-7703, BGC-823, BEL-7402, L-02, and WRL-68) [4]. When these foundational studies contain invalid data due to cell line issues, they create a ripple effect of wasted resources, misleading follow-up studies, and compromised evidence-based conclusions [4].
Consequences for Research and Drug Development
The implications of cell line misidentification extend beyond academic research to directly impact drug development and patient safety. In the biopharmaceutical industry, cell lines serve as factories for producing therapeutic proteins, antibodies, and vaccines [115]. Contamination or misidentification in these production systems can lead to batch failures, resulting in costly production delays and regulatory scrutiny [1]. The cell line development market, valued at USD 7.96 billion in 2023 and projected to reach USD 16.99 billion by 2032 [115], depends heavily on authentic, well-characterized cell lines to ensure consistent quality and yield of biopharmaceutical products.
Current Authentication Methods and Standards
Established Authentication Techniques
Multiple techniques are available for verifying cell line identity and purity. Each method offers unique advantages and is appropriate for different applications and research stages.
Table 2: Cell Line Authentication Methods and Their Applications [72] [66]
| Method | Principle | Key Applications | Advantages | Limitations |
|---|---|---|---|---|
| STR Profiling | Analyzes highly polymorphic short tandem repeat loci in the genome | Gold standard for human cell line authentication; species confirmation | High discrimination power; quantitative; standardized | Primarily for human cells; requires specialized equipment |
| Morphological Analysis | Microscopic examination of physical cell characteristics | Routine monitoring; initial identity assessment | Simple, rapid, inexpensive | Subjective; insufficient alone due to similar appearances |
| Karyotyping | Analysis of chromosome number and structure | Identifying genetic changes and chromosomal abnormalities | Detects gross genetic changes; distinguishes similar lines | Low resolution; labor-intensive |
| Isoenzyme Analysis | Electrophoretic separation of species-specific enzymes | Species verification | Effective for interspecies contamination detection | Limited discriminatory power for intraspecies contamination |
| Proteomic Analysis | Mass spectrometry-based protein expression profiling | Functional authentication; distinguishing similar genetic lines | Provides functional data; identifies unique protein markers | Complex; not yet standardized for authentication |
Short Tandem Repeat (STR) Profiling: The Gold Standard
STR profiling has emerged as the most reliable method for authenticating human cell lines. This technique examines specific regions of the genome containing short, repetitive sequence elements that vary greatly among individuals [35]. The American National Standards Institute (ANSI) published the first consensus standard for STR profiling (ASN-0002) in 2012, with revisions in 2021 [35]. The standard details how to authenticate cell lines for research use and establishes guidelines for evaluation and interpretation of STR data.
The process involves several key steps:
- DNA Extraction: Isolation of genomic DNA from the cell line to be tested
- Multiplex PCR Amplification: Simultaneous amplification of multiple STR loci using fluorescently labeled primers
- Capillary Electrophoresis: Separation of PCR products by size
- Data Analysis: Comparison of the resulting STR profile to reference databases [35]
Modern STR kits can examine up to 26 different STR loci simultaneously by using multiple fluorescent dyes, allowing 3-5 STR loci to be analyzed per dye [35]. The random match probability for a well-chosen panel of STR loci can be as low as 1 in 2.92 × 10⁹, providing exceptional discriminatory power [113].
Diagram: Cell Line Authentication Workflow Using STR Profiling
The Evolving Landscape of Authentication Standards
Current Regulatory and Journal Requirements
Growing recognition of the cell line misidentification problem has led to increasing requirements from funding agencies and scientific journals. Many journals, including Nature, International Journal of Cancer, and Cell Biochemistry and Biophysics, now require cell line authentication prior to publication [113]. The National Institutes of Health (NIH) has also implemented policies encouraging authentication, and the FDA requires that in-process materials, such as cell lines used to produce pharmaceuticals, be tested for identity and purity [113].
However, enforcement remains inconsistent. A 2025 study demonstrated varying responses from journal editors when notified about papers using misidentified cell lines. Of four cases presented to editors, only two resulted in transparent corrections, while one journal conducted an internal investigation without immediate correction, and another declined to address concerns publicly [4]. This highlights the need for universal standards and consistent enforcement.
Emerging Technologies and Approaches
Technological advancements are creating new opportunities for improved cell line authentication:
- CRISPR-Cas9 Gene Editing: Enables more precise cell line engineering and tracking of specific genetic markers [115]
- 3D Cell Culture Systems: Provide more physiologically relevant models but require enhanced characterization methods [5]
- High-Throughput Screening: Allows rapid authentication of large cell line collections [115]
- Artificial Intelligence and Automation: Improve analysis consistency and reduce human error [115]
These innovations enable faster timelines from research to commercial production, reducing costs and improving overall efficiency in biopharmaceutical manufacturing while maintaining quality standards [115].
Implementing Universal Authentication: A Practical Framework
Essential Research Reagent Solutions
Successful cell line authentication requires specific reagents and tools. The following table outlines key resources for establishing an effective authentication program.
Table 3: Essential Research Reagents for Cell Line Authentication [113] [35] [66]
| Reagent/Tool | Function | Application Example |
|---|---|---|
| STR Profiling Kits (e.g., PowerPlex, Cell ID) | Multiplex PCR amplification of STR loci | Simultaneous analysis of 9-17 STR loci plus amelogenin for gender determination |
| Capillary Electrophoresis System | High-resolution separation of DNA fragments | Accurate sizing of STR amplicons with single-base-pair resolution |
| Allelic Ladders & Size Standards | Reference for accurate allele calling | Precise determination of STR allele sizes in tested samples |
| DNA Extraction Kits | High-quality genomic DNA isolation | Purification of PCR-ready DNA from cell line samples |
| Mycoplasma Detection Kits (e.g., Hoechst 33258) | Fluorescent staining of microbial contaminants | Detection of mycoplasma contamination that can affect cell behavior |
| Reference Database Access (e.g., ATCC, Cellosaurus) | Comparison of STR profiles to known standards | Verification against established cell line fingerprints |
Recommended Authentication Workflow
Based on current best practices, the following comprehensive workflow ensures robust cell line authentication:
- Upon Acquisition: Authenticate all new cell lines immediately upon receipt, before beginning experiments
- Master Cell Bank: Create a comprehensively characterized master cell bank using multiple methods (STR profiling, species verification, mycoplasma testing)
- Routine Monitoring: Test working cell banks regularly and establish a maximum passage number for experimental use
- Pre-Publication Verification: Authenticate cell lines immediately before manuscript submission
- Documentation: Maintain detailed records of authentication results, including STR profiles, passage numbers, and testing dates [66]
Authentication should be performed at key points throughout the cell line lifecycle, including upon receipt, during master cell bank creation, at the start of new projects, and before publication [66]. Establishing these checkpoints ensures ongoing confidence in cell line identity.
The push for universal authentication standards represents a critical evolution in biomedical research practices. While significant progress has been made in developing technical standards and raising awareness, full adoption requires continued effort across multiple fronts. Researchers must prioritize authentication as an essential component of experimental design rather than an optional addition. Journals and funding agencies need to implement consistent, enforced policies requiring authentication. Finally, the scientific community must continue to develop and refine technologies that make authentication more accessible, reliable, and cost-effective.
Universal cell line authentication standards are not merely a technical formality but a fundamental requirement for research integrity. By embracing these standards, the scientific community can protect substantial research investments, ensure the validity of published findings, and accelerate the translation of basic research into meaningful clinical applications. The tools and frameworks exist; widespread implementation is the necessary next step for restoring and maintaining confidence in cell-based research.
Cell line cross-contamination represents a fundamental crisis in biomedical research, potentially compromising decades of scientific findings and drug development efforts. This phenomenon occurs when a fast-growing cell line, such as the renowned HeLa line, inadvertently overtakes another culture, leading to misidentified research models [116]. Historical evidence indicates this problem emerged in the 1950s but persists with alarming prevalence today [26]. Current estimates suggest that 15-20% of cell lines currently in use may not be what they are documented to be, with the International Cell Line Authentication Committee (ICLAC) listing 576 misidentified or cross-contaminated cell lines in its latest register [5]. The consequences are severe: misguided research directions, invalid preclinical data, retracted publications, and wasted resources exceeding millions of dollars annually [26] [116].
Within this context of quality control crisis, technological solutions have emerged to safeguard research integrity. This technical guide examines two critical validation tools—SciScore and the Research Resource Identification (RRID) Portal—that together provide a systematic approach to detecting and preventing cross-contamination while enhancing methodological transparency and reproducibility in biomedical research.
Understanding Cell Line Cross-Contamination
Historical Context and Prevalence
The cross-contamination problem traces back to the early days of cell culture. Stanley Gartler's landmark 1960s study using isoenzyme analysis revealed that 18 cell lines of presumed independent origin shared a rare enzyme isoform with HeLa cells [116]. Despite this early warning, the issue has persisted and evolved. A striking 2008 analysis of 40 human thyroid cancer cell lines found only 23 unique genetic profiles, meaning many cross-contaminated lines had been used for decades in thyroid cancer research despite not being thyroid in origin [116].
Causes and Consequences
Multiple factors contribute to this persistent problem:
- Laboratory Practices: Inadequate technique during shared media or equipment use allows vigorous lines to contaminate other cultures [116].
- Insufficient Authentication: Surveys indicate more than a third of researchers obtain cell lines from other laboratories rather than validated repositories, and almost half do not perform identity testing [116].
- Genetic Drift: Even without cross-contamination, cell lines may undergo genetic changes the longer they remain in culture [116].
- Mislabeling: Simple errors in vial identification propagate through research generations [116].
The scientific consequences manifest as published irreproducible results, with approximately 16.1% of published papers potentially using problematic cell lines [5]. This contamination of the scientific literature creates cascading problems, as subsequent research builds upon flawed foundations.
Authentication Methods: Technical Foundations
Several established methodologies form the technical basis for detecting cross-contamination and verifying cell line identity:
Table 1: Cell Line Authentication Methods
| Method | Principle | Application | Limitations |
|---|---|---|---|
| Short Tandem Repeat (STR) Profiling | PCR-based amplification of polymorphic STR loci to create unique genetic fingerprint [43] [116] | Standard for intra-species identity testing of human cell lines; recommended by ANSI ASN-0002 standard [116] | Less effective for detecting interspecies contamination |
| Isoenzyme Analysis | Electrophoretic separation of species-specific enzyme isoforms [43] [116] | Detection of interspecies cross-contamination; rapid results [116] | Subject to low reproducibility [116] |
| Karyotyping | Microscopic examination of stained chromosomes for structural and numerical abnormalities [116] | Detection of gross genetic instability and interspecies contamination [116] | Labor-intensive; requires specialized expertise |
| DNA Barcoding | Cytochrome c oxidase (COI) subunit sequencing [116] | Species identification and detection of interspecies contamination [116] | Emerging method; not yet standardized |
These authentication methods provide the technical foundation for addressing cross-contamination, yet their implementation remains inconsistent across the research community. The development of standardized tools and portals has emerged to bridge this gap between technical capability and practical implementation.
SciScore: Automated Methods Validation
SciScore is an advanced, text-mining-based validation tool that evaluates scientific manuscripts for compliance with rigor and reproducibility guidelines [117] [118]. It serves as an automated methods reviewer, checking for the presence and completeness of key methodological elements essential for research replication. The tool analyzes text for adherence to multiple established reporting frameworks including MDAR (Materials, Design, Analysis, and Reporting), ARRIVE (Animal Research: Reporting In Vivo Experiments), CONSORT (Consolidated Standards of Reporting Trials), and RRID standards [119] [120].
SciScore generates a composite score between 1-10, with the average across all journals in PubMed Central recorded at 4.2 in 2019 [119]. This score is based on both rigor adherence and resource reporting completeness, providing researchers and journal editors with a rapid assessment of methodological transparency [117].
Scoring Criteria and Rigor Assessment
SciScore evaluates manuscripts against specific rigor criteria derived from major reporting guidelines:
Table 2: SciScore Rigor and Transparency Assessment Criteria
| Criterion | Reporting Guidelines | Detection Method | Example Statement |
|---|---|---|---|
| Sex as Biological Variable | NIH, MDAR, CONSORT, ARRIVE [119] | Text mining for sex reporting | "All females were of reproductive age and none were on progestin." [119] |
| Randomization | NIH, MDAR, CONSORT, ARRIVE [119] | Sentence pattern recognition | "Animals were assigned to experimental groups using simple randomization." [119] |
| Blinding | NIH, MDAR, CONSORT, ARRIVE [119] | Keyword and context analysis | "Responses were then scored by an experimenter blinded to injection condition." [119] |
| Power Analysis | NIH, MDAR, CONSORT, ARRIVE [119] | Statistical terminology detection | "Sample size was based on estimations by power analysis with a level of significance of 0.05." [119] |
| Authentication of Cell Lines | MDAR, RRID [117] [119] | RRID and catalog number verification | Detection of RRIDs for cell lines and other key biological resources [117] |
For cell line research specifically, SciScore checks for evidence of authentication practices and the inclusion of Research Resource Identifiers (RRIDs), which have become critical markers of proper resource documentation [118].
Implementation and Effectiveness
Studies on SciScore implementation demonstrate measurable improvements in methodological reporting. Across different use cases:
- "Free for All" implementation (authors run SciScore freely during submission): Average scores increased over time, with RRID usage rising to approximately 25% of manuscripts (115 per month) [120] [121].
- "Editor Knows Best" approach (editors use SciScore for verification): Manuscript revisions showed significantly higher scores than original submissions, indicating effective improvement through the review process [120] [121].
These results suggest that automated tools like SciScore can effectively drive better reporting practices when integrated into manuscript submission workflows.
Research Resource Identification Portal
RRID System Fundamentals
The Research Resource Identifier (RRID) system provides persistent, unique identifiers for key biological resources including antibodies, cell lines, model organisms, and software tools [122]. RRIDs function similarly to ORCIDs for researchers—they create unambiguous linkages between research materials and their documentation in the scientific literature [117]. The primary mission of the RRID initiative is to "help authors identify all 'key biological resources', support the proper citation and authentication of each resource, and enable the FAIR sharing of resource information" [122].
Implementation and Integration
RRIDs are integrated within multiple major reporting frameworks and standards:
- Journal Checklists: ARRIVE, STAR Methods, and MDAR checklists all include RRID requirements [122].
- Technical Standards: RRIDs are part of the NISO JATS standard for journal article tagging and the DataCite Metadata schema version 4.6+ [122].
- Publisher Policies: Over 1,000 journals now request authors to identify key resources using RRIDs, resulting in 500,000+ RRIDs used in scholarly literature by 2022 [120] [121].
To locate RRIDs, researchers can use the centralized portal at https://scicrunch.org/resources, entering catalog numbers or resource names to find appropriate identifiers [117]. The portal provides citation-ready text for inclusion in method sections, simplifying proper resource documentation.
Integrated Validation Workflow
Combining these tools creates a comprehensive validation system for cell line research. The following workflow diagram illustrates how SciScore and RRIDs integrate to address cross-contamination risks:
This integrated workflow addresses both experimental and documentation aspects of validation. In the laboratory phase, researchers authenticate cell lines using appropriate methods (STR profiling, isoenzyme analysis) and obtain RRIDs for properly identified resources. During manuscript preparation, SciScore evaluates the completeness of methodological reporting, including the presence of RRIDs and rigor criteria statements.
Research Reagent Solutions for Authentication
Implementing effective cross-contamination prevention requires specific reagents and materials. The following table details essential components of a cell line authentication system:
Table 3: Research Reagent Solutions for Cell Line Authentication
| Reagent/Resource | Function in Authentication | Application Notes |
|---|---|---|
| STR Profiling Kits | Multiplex PCR amplification of standardized STR loci for genetic fingerprinting [116] | Select kits with markers recommended by ANSI/ATCC standard; verify species compatibility |
| Isoenzyme Analysis Gels | Electrophoretic separation of species-specific enzyme patterns for contamination detection [43] [116] | Use fresh cell extracts; include control samples for comparison |
| Authentication Databases | Reference STR profiles for comparison (ATCC, ICLAC) [116] | Regularly update database access; use multiple comparison algorithms |
| Reference Cell Lines | Positive controls for authentication methods [116] | Source from certified repositories (ATCC, ECACC); maintain proper storage |
| RRID Portal | Centralized resource for obtaining persistent identifiers [122] | Bookmark https://scicrunch.org/resources; use "cite this" function for proper citation text |
These reagents form the practical toolkit for implementing the authentication workflows described in this guide. Proper selection and use of these materials enables researchers to establish robust quality control systems within their laboratories.
Experimental Protocols for Validation
Cell Line Authentication Protocol
STR Profiling Methodology [43] [116]:
- DNA Extraction: Isolate high-quality genomic DNA from cell cultures during active growth phase (logarithmic growth)
- PCR Amplification: Perform multiplex PCR using standardized STR primer sets targeting 8-16 core loci
- Fragment Analysis: Separate amplified products using capillary electrophoresis for precise fragment sizing
- Profile Comparison: Compare resulting STR profile with reference databases (ATCC, DSMZ, ICLAC)
- Match Interpretation: Calculate match probabilities using population frequency data; ≥80% match score generally indicates authentication
- Documentation: Record all experimental parameters and generate RRID for authenticated line
SciScore Implementation Protocol
Methods Section Optimization [117] [119]:
- Resource Identification: Locate RRIDs for all key biological resources (cell lines, antibodies, organisms) using SciCrunch portal
- Rigor Statement Inclusion: Explicitly address blinding, randomization, power analysis, and sex as biological variable
- Authentication Disclosure: Describe cell line authentication method and frequency in methods section
- Pre-submission Checking: Run methods section through SciScore (available at sciscore.com) using free credits for ORCID users
- Score Improvement: Address missing criteria identified in SciScore report; add RRIDs where missing
- Iterative Refinement: Resubmit revised methods until target score achieved (journals often recommend >4)
Cell line cross-contamination represents a persistent and costly challenge in biomedical research, with potentially 15-20% of cell lines currently misidentified [116]. This problem demands systematic solutions that integrate both laboratory practices and documentation standards. SciScore and the RRID system provide complementary technologies that address different aspects of this challenge: SciScore automates the detection of methodological omissions in manuscripts, while the RRID system enables unambiguous identification of research resources.
When implemented as part of an integrated validation workflow, these tools empower researchers to detect cross-contamination early, document resources properly, and enhance the reproducibility of their findings. As major publishers, funders, and scientific societies increasingly mandate such validation practices [120] [118], these tools will become essential components of the research infrastructure—transforming quality control from an optional exercise to an integral part of the scientific process.
The scientific community's widespread adoption of these validation technologies represents a crucial step toward restoring confidence in cell line research and ensuring that future biomedical discoveries build upon a foundation of authenticated, properly documented research materials.
Conclusion
Cell line cross-contamination remains a significant, yet preventable, threat to the validity of biomedical research and the development of safe therapeutics. A proactive, multi-faceted approach—combining foundational awareness, rigorous methodological authentication, robust preventative protocols, and strict validation standards—is essential to mitigate this risk. The scientific community must collectively champion a culture of vigilance, where routine cell line authentication becomes as fundamental as any other core laboratory technique. Embracing these practices will not only conserve valuable resources and protect scientific reputations but also fortify the very foundation of evidence-based research, ensuring that future discoveries are built upon a platform of integrity and reproducibility.
References
- 1. Cell culture challenges: Contamination & prevention [https://greenelephantbiotech.com/blog/cell-culture-challenges-contamination-prevention/]
- 2. Cell Line Cross-Contamination and Accidental Co-Culture [https://www.semanticscholar.org/paper/Cell-Line-Cross-Contamination-and-Accidental-Ali/e3b019260b02009ef28e22565c55c66c1c7775d5]
- 3. Chemical alternative for cell identification and cross- ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8881561/]
- 4. Misidentified cell lines: failures of peer review, varying journal ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12247328/]
- 5. A Beginner's Guide to Cell Culture: Practical Advice for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC10000895/]
- 6. Keeping it clean: the cell culture quality control experience at ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8506661/]
- 7. Top Tips on How to Prevent Cell Line Cross-Contamination [https://bitesizebio.com/23671/top-tips-on-how-to-prevent-cell-line-cross-contamination/]
- 8. Detection of viral contamination in cell lines using ... [https://www.frontiersin.org/journals/microbiology/articles/10.3389/fmicb.2025.1595180/full]
- 9. The Importance of HeLa Cells [https://www.hopkinsmedicine.org/henrietta-lacks/importance-of-hela-cells]
- 10. Cell Line Cross-Contamination and Misidentification [https://www.sigmaaldrich.com/US/en/technical-documents/technical-article/cell-culture-and-cell-culture-analysis/mammalian-cell-culture/cell-culture-troubleshooting-cell-line-misidentification?srsltid=AfmBOorchv1iGjsy21i_BWydWfZ0hclZfDcNQr6L9hsbvQKcnbStWfns]
- 11. Discovery of HeLa Cell Contamination in HES Cells [https://pmc.ncbi.nlm.nih.gov/articles/PMC4126216/]
- 12. HeLa cells cross-contaminated nasopharyngeal carcinoma ... [https://www.nature.com/articles/s41416-024-02675-x]
- 13. culture and maintenance Cell | Abcam protocol [https://www.abcam.com/en-us/technical-resources/protocols/cell-culture-and-maintenance-protocol]
- 14. Research reporting guidelines for cell lines - PubMed Central [https://pmc.ncbi.nlm.nih.gov/articles/PMC10777224/]
- 15. Impact of Cell Culture Contamination - CLYTE Technologies [https://www.clyte.tech/post/how-operator-mistakes-lead-to-cell-culture-contamination-and-the-broader-impact-on-research-and-heal?srsltid=AfmBOooJEgOD5ojyoE3hRMzyIDq6NjUc8CtyqaOsbkeg_LiyBOb1MqnB]
- 16. Cell Line Characterization and Development Market ... [https://finance.yahoo.com/news/cell-line-characterization-development-market-082500805.html]
- 17. Viral contamination in cell culture: analyzing the impact of ... [https://www.frontiersin.org/journals/microbiology/articles/10.3389/fmicb.2025.1442321/full]
- 18. Cell Line Cross-Contamination and Misidentification [https://www.sigmaaldrich.com/US/en/technical-documents/technical-article/cell-culture-and-cell-culture-analysis/mammalian-cell-culture/cell-culture-troubleshooting-cell-line-misidentification?srsltid=AfmBOorVNAYI6-YutLWtrcQbh_SEleBuF6BMR-xTKu2RqffAxCNZhp4u]
- 19. Hundreds of researchers are using the wrong cells. That's ... [https://retractionwatch.com/2015/12/08/hela-is-the-tip-of-the-contamination-iceberg-guest-post-from-cell-culture-scientist/]
- 20. Widespread intraspecies cross-contamination of human ... [https://pubmed.ncbi.nlm.nih.gov/10508494/]
- 21. Investigation of Cross-Contamination and Misidentification of ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0170384]
- 22. Cross-contamination of a UROtsa stock with T24 cells [https://pubmed.ncbi.nlm.nih.gov/23691160/]
- 23. Cross-Contamination of a UROtsa Stock with T24 Cells [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0064139]
- 24. Bacteriophages are more virulent to bacteria with human ... [https://www.nature.com/articles/s41598-018-23418-y]
- 25. Cell line cross-contamination in biomedical research [https://pubmed.ncbi.nlm.nih.gov/18565286/]
- 26. Cell line cross-contamination in biomedical research [https://www.nature.com/articles/aps2008106.pdf]
- 27. Contaminated cell lines throw thousands of studies into question [https://www.statnews.com/2016/07/21/studies-wrong-cells/]
- 28. Reproducibility Crisis, Meet Cell Mimics – A Timely Solution [https://slingshotbio.com/reproducibility-crisis-meet-cell-mimics-a-timely-solution-to-a-persistent-challenge/]
- 29. Register of Misidentified Cell Lines [https://iclac.org/databases/cross-contaminations/]
- 30. Authenticated Cell Lines - BioSample - NCBI - NIH [https://www.ncbi.nlm.nih.gov/biosample/docs/authenticate/]
- 31. ICLAC – International Cell Line Authentication Committee [https://iclac.org/]
- 32. Databases and Datasets – ICLAC [https://iclac.org/databases/]
- 33. The Resource Identification Initiative: a cultural shift in ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC4834942/]
- 34. A Combination of Species Identification and STR Profiling Identifies Cross-contaminated Cells from 482 Human Tumor Cell Lines | Scientific Reports [https://www.nature.com/articles/s41598-017-09660-w]
- 35. Authentication of Human and Mouse Cell Lines by Short ... [https://www.ncbi.nlm.nih.gov/books/NBK144066/]
- 36. Short Tandem Repeat (STR) [http://www.wicell.org/test-cells/str/]
- 37. Authentication of Human Cell Lines Through STR Profiling [https://blog.ansi.org/ansi/authentication-human-cell-lines-str-atcc-asn-0002/]
- 38. Cell Line Authentication [https://research.pathology.wisc.edu/cell-line-authentication/]
- 39. Innovative use of forensic STRs for authentication ... [https://www.oaepublish.com/articles/jtgg.2025.08]
- 40. Authentication of African green monkey cell lines using human ... [https://bmcbiotechnol.biomedcentral.com/articles/10.1186/1472-6750-11-102]
- 41. Cell line authentication and validation is a key requirement ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12181071/]
- 42. Cell Lines as Biological Models: Practical Steps for More ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC6748863/]
- 43. Identity tests: determination of cell line cross-contamination [https://pmc.ncbi.nlm.nih.gov/articles/PMC3449683/]
- 44. | PPTX Karyotyping [https://www.slideshare.net/slideshow/karyotyping-77042313/77042313]
- 45. - Wikipedia Karyotype [https://en.wikipedia.org/wiki/Karyotype]
- 46. Isoenzyme Analysis - an overview [https://www.sciencedirect.com/topics/medicine-and-dentistry/isoenzyme-analysis]
- 47. Cell Line Authentication Using Isoenzyme Analysis [https://www.biopharminternational.com/view/cell-line-authentication-using-isoenzyme-analysis]
- 48. DNA Fingerprinting of the NCI-60 Cell Line Panel - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC4020356/]
- 49. Why the Future of Biological Research Requires Cell Line ... [https://www.psomagen.com/blog/future-of-research-requires-cell-line-authentication]
- 50. Best Practices for Cell Line Authentication [https://cellculturedish.com/best-practices-for-cell-line-authentication/]
- 51. Authentication, characterization and contamination ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7671372/]
- 52. DNA barcoding for species identification [https://bento.bio/protocol/dna-barcoding/]
- 53. Species determination via CO1 Barcoding - Authentication [https://www.atcc.org/the-science/authentication/species-determination]
- 54. Single Laboratory Validated Method for DNA-Barcoding [https://www.fda.gov/food/reference-databases-and-monitoring-programs-food/single-laboratory-validated-method-dna-barcoding-species-identification-fish]
- 55. High-throughput detection and multiplex identification of cell ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC2764421/]
- 56. Cell Line Quality Control Facility [https://www.qimrb.edu.au/core-facilities/cell-line-qc]
- 57. Cell Culture Contamination | Thermo Fisher Scientific - US [https://www.thermofisher.com/us/en/home/references/gibco-cell-culture-basics/biological-contamination.html]
- 58. How to Detect Cell Culture Contamination [https://www.goldbio.com/blogs/articles/how-to-detect-cell-culture-contamination?srsltid=AfmBOoqrFV7iX_0E0f_6SAV8C-qOIvyyAGN_rPPGdcMzXahEtDJnUtyk]
- 59. Guidelines for the use of cell lines in biomedical research - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC4453835/]
- 60. Meta-Research: Incidences of problematic cell lines are ... [https://elifesciences.org/articles/41676]
- 61. Nasopharyngeal Carcinoma Cell Lines [https://www.mdpi.com/2073-4409/13/7/559]
- 62. Cellosaurus cell line NCI-H157 (CVCL_0463) [https://www.cellosaurus.org/CVCL_0463]
- 63. ICLAC Info | Cell Line Authentication - Labcorp [https://celllineauthentication.labcorp.com/resources/iclac-info]
- 64. Cellosaurus cell line DB (CVCL_1168) [https://www.cellosaurus.org/CVCL_1168]
- 65. ATCC Cell Line Land: Advancing Transcriptome ... [https://www.atcc.org/resources/white-papers/atcc-cell-line-land-advancing-transcriptome-sequencing-for-cell-lines]
- 66. Cell Line Authentication Test Recommendations [https://www.atcc.org/resources/technical-documents/cell-line-authentication-test-recommendations]
- 67. Cell Line Authentication Resources [https://www.promega.com/resources/guides/cell-biology/cell-line-authentication/]
- 68. Preventing and Avoiding Cell Culture Contamination [https://www.technologynetworks.com/cell-science/how-to-guides/preventing-and-avoiding-cell-culture-contamination-299231]
- 69. Guidelines for the use of cell lines in biomedical research [https://www.nature.com/articles/bjc2014166]
- 70. Best Practices for Authentication of Cell Lines to Ensure Data ... [https://pubmed.ncbi.nlm.nih.gov/34860238/]
- 71. Prevention of Contaminations in Cell Culture [https://ibidi.com/content/436-prevention-of-contaminations]
- 72. Cell Line Authentication Methods: Ensuring Research ... [https://cellculturecompany.com/cell-line-authentication-methods-ensuring-research-integrity/]
- 73. Cell Culture Contamination: 5 Common Sources and How ... [https://www.capricorn-scientific.com/knowledge-center/cell-culture-contamination]
- 74. Managing Human Error in Pharma Contamination Control [https://www.pharmanow.live/hr-in-pharma/human-factors-contamination-control]
- 75. Aseptic Laboratory Techniques and Safety in Cell Culture [https://www.thermofisher.com/us/en/home/references/gibco-cell-culture-basics/aseptic-technique.html]
- 76. Tips and Tricks to Minimize Cell Culture Contamination [https://cellculturecompany.com/tips-and-tricks-to-minimize-cell-culture-contamination/]
- 77. Interfering with Interventions in Aseptic Processing [https://www.pharmtech.com/view/interfering-with-interventions-in-aseptic-processing]
- 78. Speeding Up Aseptic Processes [https://www.biopharminternational.com/view/speeding-up-aseptic-processes]
- 79. Appendix 3: Cell Culture Hygiene Practices [https://www.isscr.org/basic-research-standards/appendix-3]
- 80. for naming, receiving, and Best in culture practices managing cells [https://pubmed.ncbi.nlm.nih.gov/28986713/]
- 81. Cell Line Management [https://www.titian.co.uk/en-us/solutions/cell-line-management]
- 82. CellPort: The Cell Culture Management Software [https://www.cellportsoftware.com/blog/cellport-the-cell-culture-management-software]
- 83. Layout and Multi-Product Facility for Line Therapy... Management Cell [https://www.linkedin.com/pulse/facility-layout-multi-product-line-management-cell-therapy-lbeye]
- 84. Cell Line Cross-Contamination and Misidentification [https://www.sigmaaldrich.com/US/en/technical-documents/technical-article/cell-culture-and-cell-culture-analysis/mammalian-cell-culture/cell-culture-troubleshooting-cell-line-misidentification?srsltid=AfmBOoqnTCxg1JjaUmxoI4fWLGfp2_YGupizsdbfuxRiZCUVbI7MCKvN]
- 85. Cell cross-contamination in cell cultures: the silent and neglected danger - PubMed [https://pubmed.ncbi.nlm.nih.gov/9542623/]
- 86. Cell Line Cross-Contamination and Misidentification [https://www.sigmaaldrich.com/US/en/technical-documents/technical-article/cell-culture-and-cell-culture-analysis/mammalian-cell-culture/cell-culture-troubleshooting-cell-line-misidentification?srsltid=AfmBOopnCAbB3KFAdiFodZ44_Lnx7XVOLhuQt_eRPdbK91H80OsgMN6Y]
- 87. Cell bank system, establishment, and application in the ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12409320/]
- 88. The differences between master cell bank (MCB) and ... [https://www.susupport.com/blogs/knowledge/the-differences-between-master-cell-bank-mcb-and-working-cell-bank-wcb]
- 89. A cell bank paradigm for preclinical evaluation of an ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11534090/]
- 90. Cell Bank Preparation and Characterization [https://www.bioprocessintl.com/cell-line-development/cell-banking-in-the-spotlight-advising-biologics-developers-about-cell-bank-preparation-and-characterization]
- 91. Recommendations for Cell Banks Used in GXP Assays [https://www.bioprocessintl.com/cell-therapies/recommendations-for-cell-banks-used-in-gxp-assays]
- 92. Authenticating Your Cell Lines – Why, When and How! [https://blog.crownbio.com/authenticating-your-cell-lines]
- 93. Cell Culture Contamination: How to Prevent Fungal, Yeast, ... [https://www.corning.com/worldwide/en/products/life-sciences/resources/stories/at-the-bench/how-to-control-bacterial-contamination-and-other-unwelcome-micro.html]
- 94. How to respond to a pharmaceutical contamination incident [https://pharmaceuticalmanufacturer.media/pharmaceutical-industry-insights/latest-pharmaceutical-manufacturing-industry-insights/how-to-respond-to-a-pharmaceutical-contamination-incident/]
- 95. Viral Contamination in Bioproduction Facilities [https://www.bioprocessintl.com/viral-clearance/a-response-plan-for-viral-contamination-in-bioproduction-facilities]
- 96. Biocontainment and Safety [https://www.atcc.org/the-science/culturing-cells/biocontainment-and-safety]
- 97. Comprehensive Microbial Control Strategy [https://www.bioprocessintl.com/qa-qc/beyond-traditional-microbiology-testing-developing-a-comprehensive-strategy-for-microbial-control-and-detection]
- 98. The Differences Between GCP, GLP and GMP Audits [https://www.thefdagroup.com/blog/2015/07/gxp-audits/]
- 99. Key Differences Between GCP, GLP, and GMP [https://jafconsulting.com/key-differences-between-gcp-glp-and-gmp-an-in-depth-analysis/]
- 100. Modelling and magnitude estimation of cross‐ ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7691616/]
- 101. Good Laboratory Practices vs. Good Manufacturing Practices [https://www.eurofinsus.com/food-testing/resources/good-laboratory-practices-vs-good-manufacturing-practices-whats-the-difference/]
- 102. Misidentified cell lines: failures of peer review, varying journal responses to misidentification inquiries, and strategies for safeguarding biomedical research | Research Integrity and Peer Review | Full Text [https://researchintegrityjournal.biomedcentral.com/articles/10.1186/s41073-025-00170-2]
- 103. An efficient toolkit for cancer cell line authentication [https://www.sciencedirect.com/science/article/pii/S2001037023003537]
- 104. Journal & NIH funding guidelines - Cell Line Authentication [https://celllineauthentication.labcorp.com/resources/journal-nih-funding-guidelines]
- 105. Federal Regulations and the Ethical Collection of Specimens ... [https://dctd.cancer.gov/research/research-areas/biobanking-biospecimen-science/elsi/federal-regulations]
- 106. Authenticating Cell Lines: Preventing Misidentification and ... [https://www.cytion.com/us/Knowledge-Hub/Blog/Authenticating-Cell-Lines-Preventing-Misidentification-and-Cross-Contamination/]
- 107. Guidelines — International Society for Stem Cell Research [https://www.isscr.org/guidelines]
- 108. Cell Line Cross-Contamination and Misidentification [https://www.sigmaaldrich.com/US/en/technical-documents/technical-article/cell-culture-and-cell-culture-analysis/mammalian-cell-culture/cell-culture-troubleshooting-cell-line-misidentification?srsltid=AfmBOopeR-tCY8vKW83MY5FWPwKe13tpIkSc8e364WKMX1yX6SWRY1B2]
- 109. RUO vs GMP: Understanding the Differences Between ... [https://cellculturecompany.com/ruo-vs-gmp-understanding-the-differences/]
- 110. Good Manufacturing Practice (GMP) standards [https://www.who.int/teams/health-product-policy-and-standards/standards-and-specifications/norms-and-standards/gmp]
- 111. Current Good Manufacturing Practice (CGMP) Regulations [https://www.fda.gov/drugs/pharmaceutical-quality-resources/current-good-manufacturing-practice-cgmp-regulations]
- 112. Research Use Only to Good Manufacturing Practices [https://www.thermofisher.com/us/en/home/biotech-lab-solutions/biotech-learning-center/ruo-gmp-compliant-biologics.html]
- 113. Doing Good Science: Authenticating Cell Line Identity [https://www.promega.com.br/en/resources/pubhub/cell-line-authentication-with-strs-2012-update/]
- 114. Why Cell Line Characterization Protects Your Research ... [https://cellculturecompany.com/why-cell-line-characterization-protects-your-research-investment/]
- 115. Cell Line Development Market Trends and Forecast Analysis [https://introspectivemarketresearch.com/reports/cell-line-development-market/]
- 116. Cell Line Cross-Contamination and Misidentification [https://www.sigmaaldrich.com/US/en/technical-documents/technical-article/cell-culture-and-cell-culture-analysis/mammalian-cell-culture/cell-culture-troubleshooting-cell-line-misidentification?srsltid=AfmBOool4llW-Y-GGX8zYWEcGQbYZzt915WilHHht9zsLWdHodd8i95S]
- 117. SciScore: The best methods review tool for scientific research [https://sciscore.com/]
- 118. The best methods review tool for scientific research [https://www.sciscore.com/news/SciScore_AACR_Press_Release_02062020.php]
- 119. SciScore Report FAQ - SciCrunch [https://www.scicrunch.com/sciscorereport-faq]
- 120. Assessing the Effectiveness of SciScore in Supporting the ... [https://www.csescienceeditor.org/article/4257/]
- 121. Assessing the Effectiveness of SciScore in Supporting ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12338114/]
- 122. Research Resource Identifier [https://www.rrids.org/]